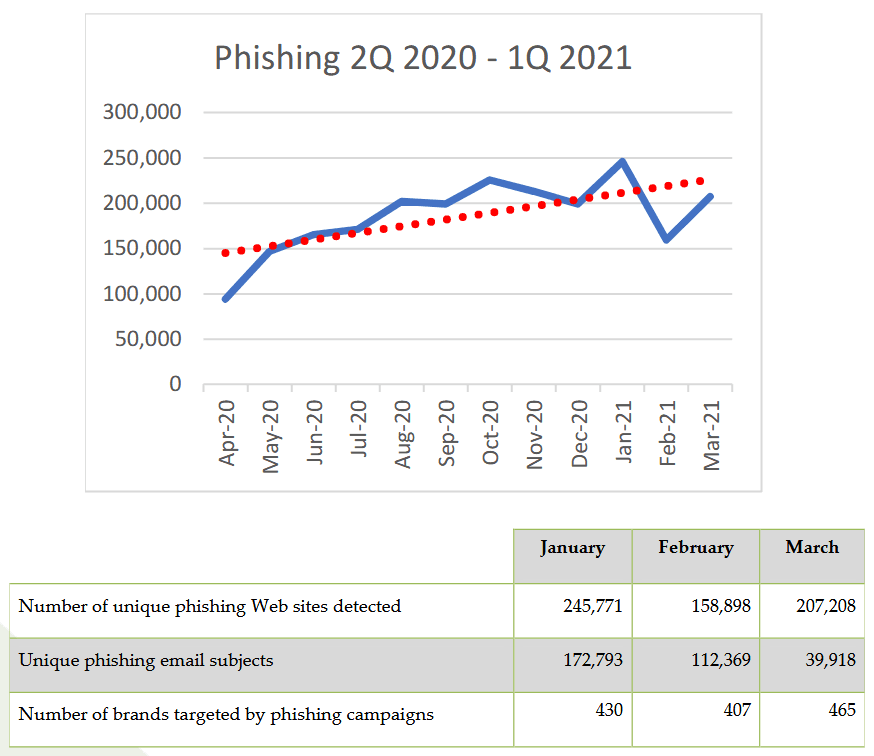
Phishing sites reached all-time high in January 2021
The number of active phishing sites hit a record number earlier this year in January, according to an industry report published this week by the Anti-Phishing Working Group (APWG).
A total of 245,771 phishing sites were detected in January. The number represents the unique base URLs of phishing sites found and reported by APWG members.
The APWG is an industry coalition made up of more than 2,200 organizations from the cyber-security industry, government, law enforcement, and NGOs sector, which includes some big names such as Microsoft, Facebook, PayPal, ICANN, AT&T, Comcast, Digicert, Cloudflare, Cisco, Salesforce, RSA, Verisign, ESET, McAfee, Avast, Symantec, Trend Micro, PhishLabs, Agari, Cofense, and many others.
APWG experts noted that while the number of phishing sites declined in February, the next month, in March, the number of phishing sites jumped above 200,000 again, amounting to the fourth-worst month in APWG's reporting history.
The industry vertical most targeted in phishing attacks in Q1 remained the financial sector, which saw almost a quarter of all phishing attempts.
Second was social media, with cybercrime groups attempting to hijack social media accounts to resell online on specialized marketplaces, according to the APWG report [PDF].

Furthermore, around 83% of all phishing sites seen in Q1 2020 were also hosted on an HTTP-based connection.
According to John LaCour, CTO of PhishLabs, in Q1 2021, 94.5% of all TLS certificates used in phishing attacks were "Domain Valid" or "DV" certificates.
"DV certificates are commonly granted for freeby providers such as Let's Encrypt and cPanel, and provide the weakest form of certificate validation, requiring no authentication of the user –only the domain name being used," LaCour said.
This finding reinforces a piece of well-known cybersecurity advice that if a website is loaded via HTTPS, it doesn't mean it's secure, but merely that its traffic can't be easily intercepted.
BEC wire transfers reach an all-time high too
In addition, the APWG also tracks business email compromise (BEC) scams, a scheme where criminal gangs used spoofed emails in attempts to trick companies into sending wire transfers to the wrong bank accounts.
The APWG said the average sum of an attempted wire transfer in BEC attacks reached a peak value of $85,000, up from $48,000 in Q3 2020 and over the previous high of $80,000 seen in Q1 2020.
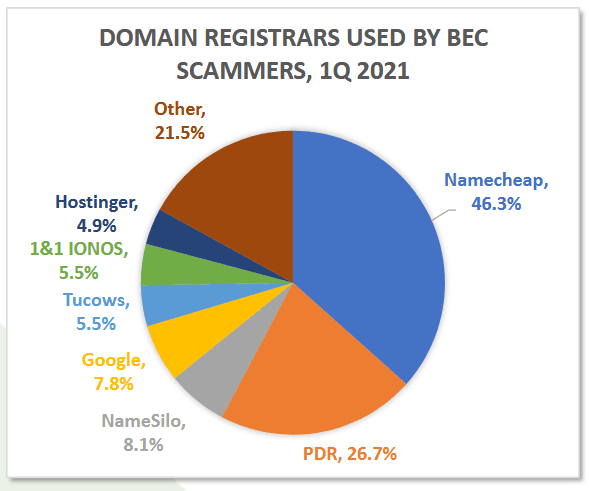
The APWG report also found that Namecheap continued to be the favorite domain registrar used by cybercriminals to register their malicious domains in BEC scams.
The company, which was sued last year by Facebook, was used to register 46.3% of all malicious domains used in BEC attacks, a number that went up from 32% in Q4 2020.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



