Phishing campaign targets European officials assisting in refugee operations
A phishing campaign with possible links to a state-sponsored actor is targeting European officials assisting in the effort to evacuate Ukrainian refugees, cybersecurity firm Proofpoint said in a report Wednesday.
Although the company said attribution remains unclear at this point, it found similarities with campaigns conducted by the cyberespionage group known as UNC1151 (also referred to as GhostWriter or TA445). The group is believed to be a Belarusian state-sponsored actor that supports Russia amidst its invasion of Ukraine.
Proofpoint said the campaign originated from an email address that appears to belong to a compromised Ukrainian armed service member. The email contained a number of malicious attachments, one of which attempted to download Lua malware called SunSeed intended for European personnel involved in overseeing transportation and population efforts within the region. Another macro attachment used language that made it look like it was related to a February 23 Emergency Meeting of the NATO Security Council, which Proofpoint said was used to lure targets into clicking on it.
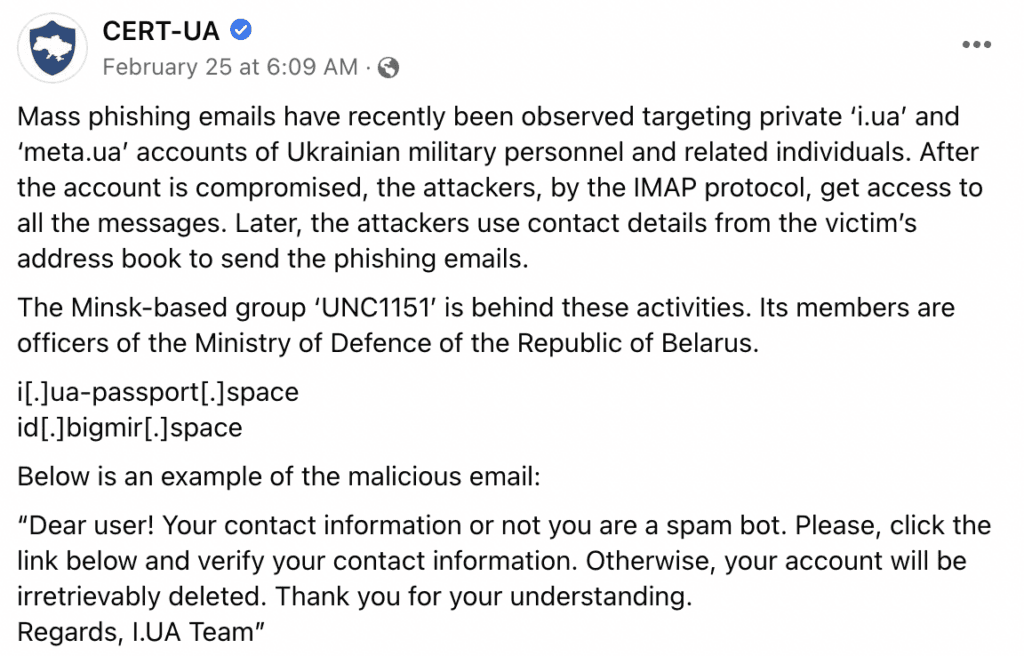
The phishing attacks announced by Proofpoint were not the first to target Ukraine and its allies amidst the ongoing conflict with Russia. Last week, Ukraine’s Computer Emergency Response Team (CERT-UA) posted a public service announcement on Facebook alerting civilians to recent mass phishing emails directed at Ukrainian military personnel with ‘i.ua’ and ‘meta.ua’ accounts. After the malware infiltrates the account, the threat actor gains access to all messages and contacts within the system, the agency said.
After the phishing attack of ‘meta.ua’ accounts, Meta announced that they had removed and blocked the accounts linked to UNC1151.
“Phishing is popular simply because it’s easy and it works,” said Brett Callow, a threat analyst at Emsisoft. “Campaigns orchestrated by both state and non-state actors are an ongoing concern and it wouldn’t be at all surprising if they were being leveraged now for the purpose of intelligence gathering during the war. In fact, it would be far more surprising if they weren’t.”
Although Proofpoint said it hasn’t “observed concrete technical overlaps” between the phishing campaign and previous UNC1151 attacks, it added that there are several reasons to believe they are linked.
“While Proofpoint has not definitively attributed this campaign to the threat actor TA445, researchers acknowledge that the timeline, use of compromised sender addresses aligning with Ukrainian government reports, and the victimology of the campaign align with published TA445 tactics to include the targeting and collection around refugee movement in Europe,” the report stated.
Emma Vail
Emma Vail is an editorial intern for The Record. She is currently studying anthropology and women, gender, and sexuality at Northeastern University. After creating her own blog in 2018, she decided to pursue journalism and further her experience by joining the team.


