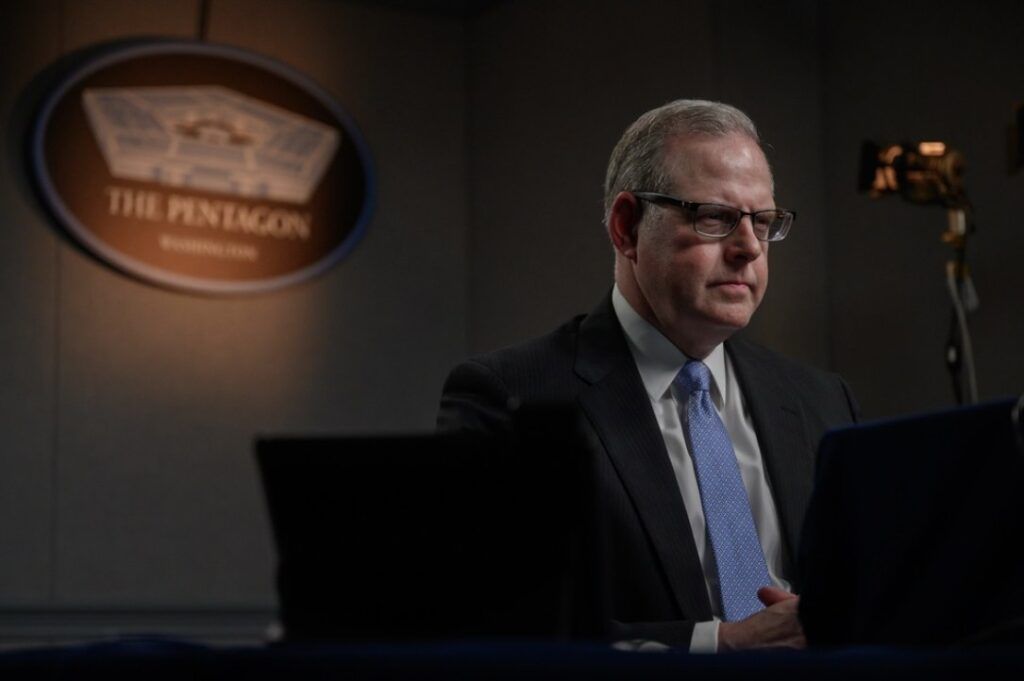
Pentagon CIO on protecting the military from high-level cyber threats
John Sherman was sworn in as the Pentagon’s new CIO at a time of unprecedented cyber risks.
He entered his new role as organizations around the world scrambled to shore up their networks against the Log4j vulnerability and the Defense Department shook up oversight of its high-tech innovation hubs in a bid to better compete with China.
Now, as Washington worries about hacks bleeding out of Ukraine’s conflict with Russia, Sherman spoke to The Record about the digital threats facing the federal government’s largest agency.
This interview took place shortly before Russia’s invasion of Ukraine and is the second part of a sit-down with Sherman. It has been edited for length and clarity.
The Record: In recent weeks White House officials, CISA and others have warned that Russia’s actions in Ukraine could result in cyberattacks against the U.S. What precautionary steps have you undertaken yourself to warn system administrators?
JS: What I'm going to talk to you about is the process, not the discrete steps, because I don't want to show our hand to potential adversaries in Moscow or anywhere else.
I'm in touch daily with [U.S. Cyber Command and NSA chief] Paul Nakasone, with General Bob Skinner, who is the Defense Information Systems Agency and the Joint Force Headquarters-Department of Defense Information Network commander. When he's on the JFHQ-DODIN side of things, he's working for General Nakasone. We are lucky here at DoD to have an entire command dedicated to protecting our networks. That's what JFHQ-DODIN exists to do.
We're working with supported combatant commands to make sure their particular areas of responsibility are tended to, that our most sensitive networks are being taken care of in a proactive set of steps that is tended to constantly.
For me as a CIO, I'm in a way a customer of their services, to highlight what I want to make sure is getting done and ensure that CYBERCOM is doing that.
Then with our military departments and the service cyber elements, that they're all leaning in to do what General Nakasone is getting done. Then finally with our military department colleagues to make sure they're thinking through, from a CIO perspective, if something goes down, what do we do?
One other thing I'll note is the defense industrial base. [Chief Information Security Officer] Dave McKeown is holding video or team calls with the DIB. The purpose of those is to talk about cyber hygiene to the DIB. What do we need to be aware of? Pointing them to different alerts and documents that NSA's put out and CYBERCOM and CISA.
"Tensions are high. We're always in a cybersecurity-threatened environment here. The enemy is always coming. Our adversaries are always coming at us. We have to be on, all the time."
—John Sherman, Defense Department CIO
We are putting things out on our websites to make sure that we are getting information out widely here.
Tensions are high. We're always in a cybersecurity-threatened environment here. The enemy is always coming. Our adversaries are always coming at us. We have to be on, all the time.
Right now, yes, tensions are high and we are particularly energized.
TR: Do you wish you could issue public advisories? Do you wish you could be more transparent about the steps? Are you comfortable where you are?
JS: I'm comfortable where we are.
We are following the White House’s lead on this very carefully, in terms of how we would want to message to U.S. industry and others.
I can promise you here, too, within the building, all the key stakeholders are aware that we need to be ready and watch.
I believe we are taking all the necessary steps. Going back to one of your questions, how do we get better at communicating with the DIB? How do we get to not just the Beltway ecosystem and companies that are major defense contractors, names we would all recognize, but subs to subs? That is a major issue I want to make sure we do better on.
TR: During your confirmation hearing, you called China a “paramount threat" to DOD systems, that we do not want the Chinese “in or near our system.” In your two months in office, what have you done on that?
JS: This gets back to really about cybersecurity, about Zero Trust. When I say, I don't want them on or near our systems, what I would say to amplify that, is maybe if they're going to get into our systems, I'm not going to let them move laterally in our systems.
They are a key pacing challenge, as the secretary indicates, and they're very sophisticated and we need to be ready for them to come after all facets of our IT ecosystem: our networks, our compute, our P&T, and everywhere else.
This goes back to the industry interaction, and others, that we have best-in-breed approaches.
I'll give you one example: moving away from signature-based analysis on Zero Trust of, ‘Okay, that you've just got the kind of common signatures,’ to behavioral-based analysis, which is a different way of coming at cybersecurity, which is more sophisticated.
Very fine-grained access in terms of identity and credential access management, other things that will complicate a sophisticated adversary's ability, like China, to maliciously harm our networks, monitor our networks, spoof our systems where if we're trying to go one way, they try to make us go another.
It is a constant endeavor; realize that they are always on this and we've got to always be progressing. We cannot stand still on any aspect of what we're doing.
TR: You also said the Pentagon is well-postured to withstand a digital barrage from Beijing, “based on what I know right now." Do you stand by that statement?
JS: I stand by that statement. China is a very sophisticated adversary, or challenge, I should say.
We are as prepared as I think as any large enterprise can be expected to be, but I'm not going to undersell the sophistication of their threat.
We are ready to stand up with all the best capability, technology and innovation that we're going to bring to the fight. But if China were to come at us with a massive barrage, that's a very serious issue. Same as whether they're coming with cyberattacks, or God forbid, some sort of kinetic sort of thing.
This would be a historic, very large-scale issue here. What I can tell you as CIO is that we are taking every step we know how to take that best-in-breed in industry, what best approaches and principles, that is an outcome I hope never happens because that would mean that we're at war with China perhaps.
That is the high-end possibility that we have to be ready for. I can promise you this pervades everything we're doing here in terms of where we set the bar, where we need to be ready to react to.
TR: Closer to home, Log4j. CISA has stated that it has not witnessed any disruption to critical infrastructure or other assets within the government. Have you seen any evidence of disruption within DOD systems because of Log4j?
JS: Not yet.
I'm never going to say that there is no threat there or that everything is perfectly taken care of because this is an ongoing issue here with Log4j.
[CISA Director Jen Easterly] and others have said that this is one of the largest issues we have faced in terms of how pervasive it is. This gets back, though, to having CYBERCOM and Joint Force Headquarters-DODIN look at all of our forward-facing capabilities, looking at our log servers and everywhere else this could be.
As indicated by CISA and others, this is going to take months and years to get after. I have a good feeling, as we're sitting here talking right now about this. But this may run so deep and so far, as it does every other government agency and many private sector companies. This has been eye-opening to how we need to think about being a consumer of software.
We need to think differently about how we're consumers of both open-source software, proprietary software and anything else for that matter about how we bring that into our ecosystem. This has been a bit of a wake-up call for everybody, and we are going to get after this in terms of both remediation of this vulnerability, but how we think broadly about software in the future.
TR: Besides a bug bounty by the Defense Digital Service, has the department launched any other efforts to eradicate potential weaknesses caused by this bug?
JS: All I will say at this time is there is robust activity by CYBERCOM and Joint Force Headquarters, as they would for any other vulnerability, to get after this with using a number of measures to make sure our networks and systems are safe.
Martin Matishak
is the senior cybersecurity reporter for The Record. Prior to joining Recorded Future News in 2021, he spent more than five years at Politico, where he covered digital and national security developments across Capitol Hill, the Pentagon and the U.S. intelligence community. He previously was a reporter at The Hill, National Journal Group and Inside Washington Publishers.



