US offering $10 million for info on Russian military hackers accused of NotPetya attacks
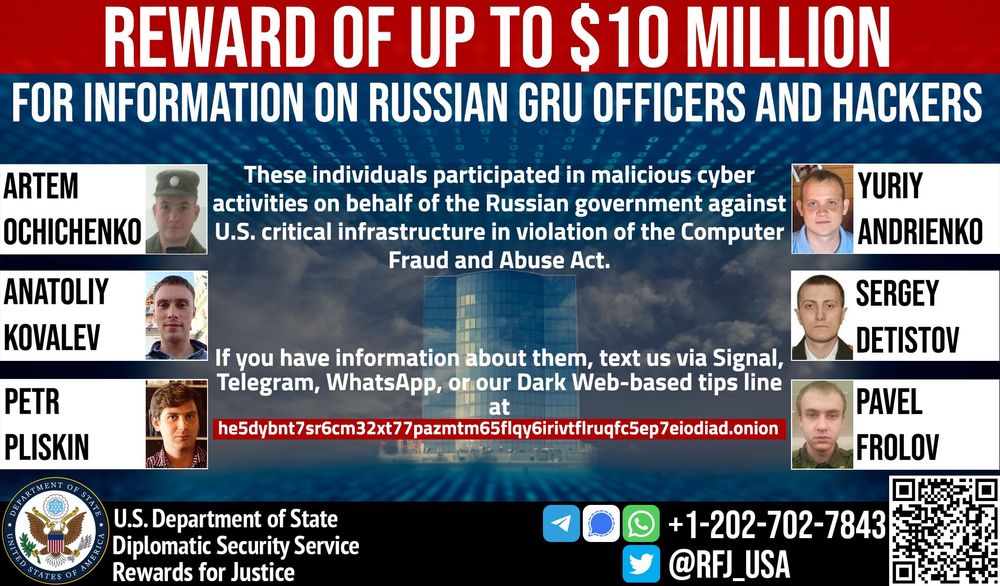
The U.S. State Department announced a $10 million reward Tuesday for information about six hackers working within the GRU, Russia’s foreign military intelligence agency.
The six — all of them tied to the infamous “Sandworm” hacking group — were implicated in the creation and propagation of the NotPetya malware in charges filed by the Justice Department in 2020.
U.S. officials previously said NotPetya caused $10 billion worth of damage worldwide but noted in a release on Tuesday that the malware collectively cost U.S. organizations nearly $1 billion in losses.
GRU officers Yuriy Sergeyevich Andrienko, Sergey Vladimirovich Detistov, Pavel Valeryevich Frolov, Anatoliy Sergeyevich Kovalev, Artem Valeryevich Ochichenko and Petr Nikolayevich Pliskin are listed in the notice and are accused of violating the Computer Fraud and Abuse Act (CFAA) through attacks on U.S. critical infrastructure.
“These individuals were members of the criminal conspiracy responsible for the June 27, 2017, destructive malware infection of computers in the United States and worldwide using malware known as NotPetya,” the State Department said. “These cyber intrusions damaged the computers of hospitals and other medical facilities in the Heritage Valley Health System (Heritage Valley) in western Pennsylvania, a large U.S. pharmaceutical manufacturer, and other US private sector entities.”
REWARD! Up to $10M for information on 6 Russian GRU hackers. They targeted U.S. critical infrastructure with malicious cyber ops. Send us info on their activities via our Dark Web-based tips line at: https://t.co/WvkI416g4Whttps://t.co/oZCKNHU3fY pic.twitter.com/u1NMAZ9HQl
— Rewards for Justice (@RFJ_USA) April 26, 2022
The DOJ has previously said that NotPetya crippled Heritage Valley’s two hospitals, 60 offices, and 18 community satellite facilities, keeping hospital officials from accessing patient histories, exam files and lab records.
The hospitals had no access to computer systems connected to cardiology, nuclear medicine, radiology, and surgery departments for a week, and their administrative systems were down for nearly a month.
The six GRU members worked within Unit 74455, which is also known by some researchers as Voodoo Bear, Telebots and Iron Viking.
In 2020, they were charged with a range of offenses connected to attacks on Ukraine, Georgia, France and South Korea.
In addition to NotPetya, the group used destructive malware like KillDisk and Industroyer to cause blackouts in Ukraine. They also deployed the Olympic Destroyer malware against systems managing the 2018 PyeongChang Winter Olympics and launched attacks on French organizations supporting President Emmanuel Macron in 2017.
The U.S. government says Andrienko, Pliskin, Detistov and Frolov developed components of the NotPetya, Olympic Destroyer and KillDisk malware, while Kovalev and Ochichenko managed spearphishing campaigns targeting the IOC, Olympic athletes, 2018 PyeongChang Winter Olympic Games partners, government officials in France and government officials in Georgia.
Kovalev faced previous charges from the Justice Department for hacking into organizations tied to the administration of the U.S. presidential election in 2016.
According to the Justice Department, the group has also caused damage to systems in the Netherlands and the U.K.
“No country has weaponized its cyber capabilities as maliciously or irresponsibly as Russia, wantonly causing unprecedented damage to pursue small tactical advantages and to satisfy fits of spite,” Assistant Attorney General for National Security John C. Demers said in 2020 about the members of Sandworm.
“Today the department has charged these Russian officers with conducting the most disruptive and destructive series of computer attacks ever attributed to a single group, including by unleashing the NotPetya malware. No nation will recapture greatness while behaving in this way.”
Since the invasion of Ukraine earlier this year, Sandworm has been implicated in a range of attacks against Ukrainian critical infrastructure and government agencies.
Two weeks, ago, U.S. Attorney General Merrick Garland announced that federal agencies had disrupted a global botnet of thousands of infected devices that they believe was controlled by Sandworm.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.