North Korean hackers use fake job offers, salary bumps as lure for crypto theft
Hackers connected to the North Korean military used a variety of new phishing methods in 2022 to steal cryptocurrency, according to a new report from Proofpoint.
The hackers bombarded people with emails about fake job opportunities at prestigious firms or fictitious salary increases as a way to get people to open emails carrying malware that enables the group to steal cryptocurrency.
According to Greg Lesnewich, senior threat researcher at Proofpoint, the North Korea-linked advanced persistent threat (APT) group TA444 operates “with a startup mentality and a passion for cryptocurrency."
"TA444 spearheads North Korea’s cashflow generation for the regime by bringing in launderable funds," he told The Record. "This threat actor rapidly ideates new attack methods while embracing social media as part of their MO.
“In 2022, TA444 took its focus on cryptocurrencies to a new level and has taken to mimicking the cybercrime ecosystem by testing a variety of infection chains to help expand its revenue streams.”
Proofpoint specifically tracked the work of the group but said its activity overlaps with others, tagged as APT38, Lazarus Group, Stardust Chollima, and COPERNICIUM – all of which operate with the primary goal of raising money for North Korea’s government.
The researchers noted that the activity stands out among government hacking groups because while most are focused on espionage and data theft, TA444 is solely interested in stealing funds – deploying methods typically used by cybercriminals.
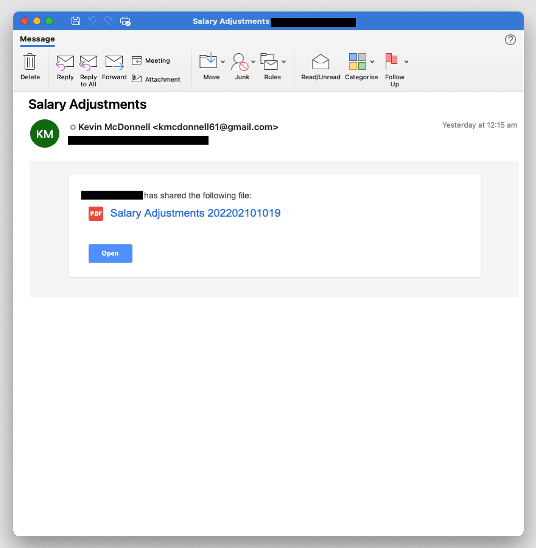
The group typically delivers its malware through malicious documents but expanded its work last year, abusing email marketing tools like SendInBlue and SendGrid with a range of scam emails.
The group has even developed a social media component to its attacks, communicating with victims on LinkedIn before sending malicious links. Proofpoint researchers said they saw communications in English, Spanish, Polish, and Japanese.
In December 2022, the researchers saw another arm of the group emerge with a widespread credential harvesting campaign targeting organizations across the U.S. and Canada in finance, education, government, and healthcare.
“The lure emails enticed users to click a SendGrid URL which redirected to a credential harvesting page. The deviation in TA444’s targeting and volume of messages made us thoroughly analyze the campaign to both understand the activity, but also challenged our assumptions about the group,” the researchers said.
“This spam wave alone nearly doubled the total volume of TA444 email messages we had observed in our data during 2022, so we were concerned about false positive detection, as well as understanding a potential change in TA444 objectives.”
The emails appeared legitimate based on the senders' addresses and included a link that redirected victims to a page that replicated their company’s iconography.
The group uses a variety of post-exploitation backdoors as well as virtualized listeners, and browser extensions to facilitate theft.
Proofpoint researchers noted that the group has previously been tied to headline-grabbing cyberattacks on Bangladesh Bank and several cryptocurrency firms.
Both Tornado Cash and BlenderIO – two well-known cryptocurrency mixing services – were sanctioned by the United States Treasury Department for helping TA444 launder more than $120 million in stolen coins.
On Monday, the FBI attributed the $100 million hack of Harmony Bridge to APT38.
“TA444 and related clusters are assessed to have stolen nearly $400 million dollars’ worth of cryptocurrency and related assets in 2021. In 2022, the group surpassed that value in a single heist worth over $500 million, gathering more than $1 billion during 2022,” the researchers said.
“North Korea, like other cryptocurrency enthusiasts, has weathered the declining value of cryptocurrencies, but remains engaged in its efforts to use cryptocurrency as a vehicle to provide usable funds to the regime.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



