North Korean hackers targeted ethnic Koreans in China with Android ‘BirdCall’ malware
Ethnic Koreans living in the Yanbian region of China were targeted by a sophisticated North Korean hacking group with a strain of malware attached to a popular Android mobile game.
Researchers at cybersecurity firm ESET attributed the campaign to APT37 and said the hackers used a backdoor attached to a suite of card games from a company called Sqgame.
The backdoor, named BirdCall by the researchers, allowed APT37 to take screenshots, record calls, steal personal data and more. The Yanbian region of China is on the border with North Korea and is often referred to as “Third Korea.” ESET researchers said the campaign was likely aimed at refugees or defectors from the North Korean regime.
The backdoor was initially thought to target only Windows devices, but an Android version was later discovered. Through BirdCall, APT37 is able to collect contact information, SMS texts, call logs, media files and private keys. The Android version of the backdoor was developed over the span of several months and ESET says it found seven versions of it.
ESET researcher Filip Jurčacko said victims typically downloaded the compromised games through a web browser on their devices and installed them directly, without going through the Google Play store.
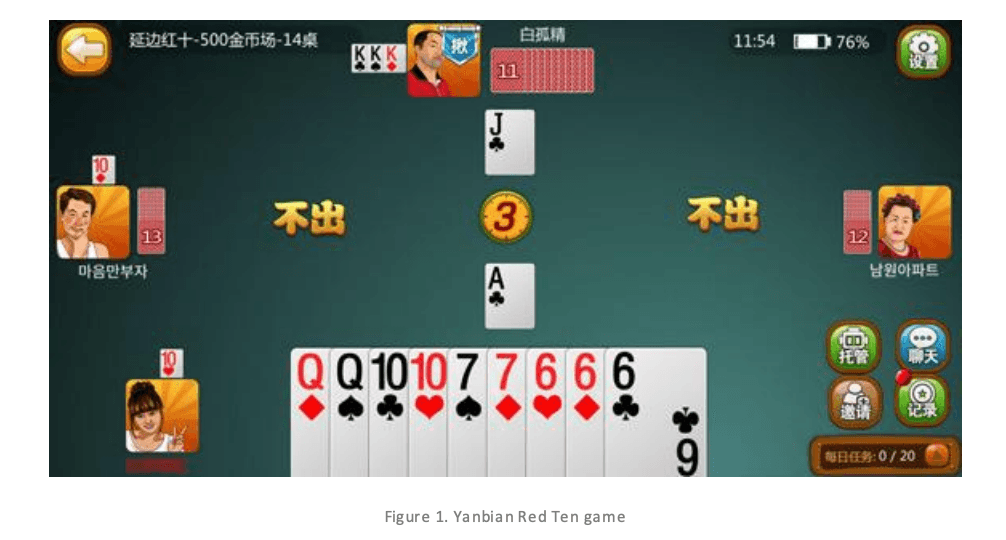
Image: ESET
“We were unable to determine when the website was first compromised and the supply-chain attack started,” Jurčacko said.
APT37 has operated since 2012 and is allegedly housed within North Korea’s Ministry of State Security, focusing much of its work on espionage campaigns targeting South Korea and other Asian countries. The group has previously targeted government or military organizations as well as North Korean defectors.
The Windows version of BirdCall being used by APT37 was initially discovered by South Korean cybersecurity vendor AhnLab and others in 2021.
ESET noted that the initial file downloaded from the Sqgame website by victims was not malicious. It became malicious due to a subsequent update package delivered by the platform that had been compromised since at least November 2024.
ESET added that they contacted Sqgame in December 2025 but did not receive a response. The update package is no longer malicious, the researchers said.
The malware hands attackers a host of information about the device on its first run and “can record audio via the microphone and eavesdrop on the surroundings of the compromised device.” It also searches any shared external storage devices for specific file types.
Last year, researchers found another strain of Android spyware developed and used by APT37 embedded in apps that could be found in the Google Play store.
APT37 reportedly targeted South Korean academic experts and a North Korea-focused news outlet in 2024.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



