North Korean hackers posed as Samsung recruiters to target security researchers
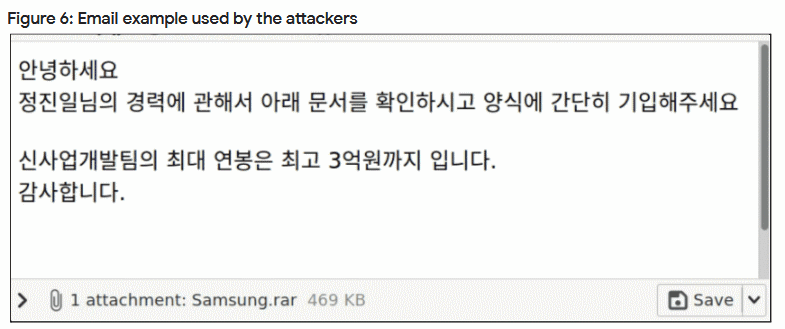
North Korean state-sponsored hackers posed as Samsung recruiters and sent fake job offers to employees at South Korean security companies that sell anti-malware software, Google said this week in the first edition of its new Threat Horizons report.
"The emails included a PDF allegedly claiming to be of a job description for a role at Samsung; however, the PDFs were malformed and did not open in a standard PDF reader," Google said.
If targets complained that they couldn't open the job offer archive, the hackers offered to help by providing them with a link to a "Secure PDF Reader" app users could install.
But Google says this file was a modified version of PDFTron, a legitimate PDF reader, altered to install a backdoor trojan on the victim's computers.
The Google Threat Analysis Group, the Google security team which detected the malicious emails, attributed the attacks to the same team of North Korean hackers who previously targeted security researchers on Twitter and other social networks in late 2020 and throughout 2021.
Tracked by Microsoft under the codename of "Zinc," this threat actor's tactics have perplexed the security community, which believes the group tried to acquire unreleased vulnerabilities and exploits from some of their naive and careless members.
However, the attack on South Korean antivirus makers might be different since compromising their employees might provide the group with access to the means to carry out a targeted supply chain attack against South Korean organizations, where those companies' anti-malware software might be running.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



