North Korean hacking group Kimsuky targeting regional experts, news outlets
The North Korean government-backed hacking group Kimsuky is targeting experts in North Korean affairs and media as part of a campaign to gather intelligence — even resorting to stealing subscription information for news outlets reporting on the country's affairs.
The findings, published on Tuesday by SentinelOne, coincide with an alert from the National Security Agency last week warning that Kimsuky is using social engineering and malware to target think tanks, academia, and the media.
SentinelOne worked with the news outlet NK News to track the social engineering campaign, finding that it largely focused on the theft of email credentials, the delivery of malware for information gathering and the theft of NK News subscription credentials.
In the campaign uncovered by SentinelOne, Kimsuky actors engage in “extensive” correspondence over email and use spoofed URLs, websites imitating legitimate web platforms, and Microsoft Office documents weaponized with malware.
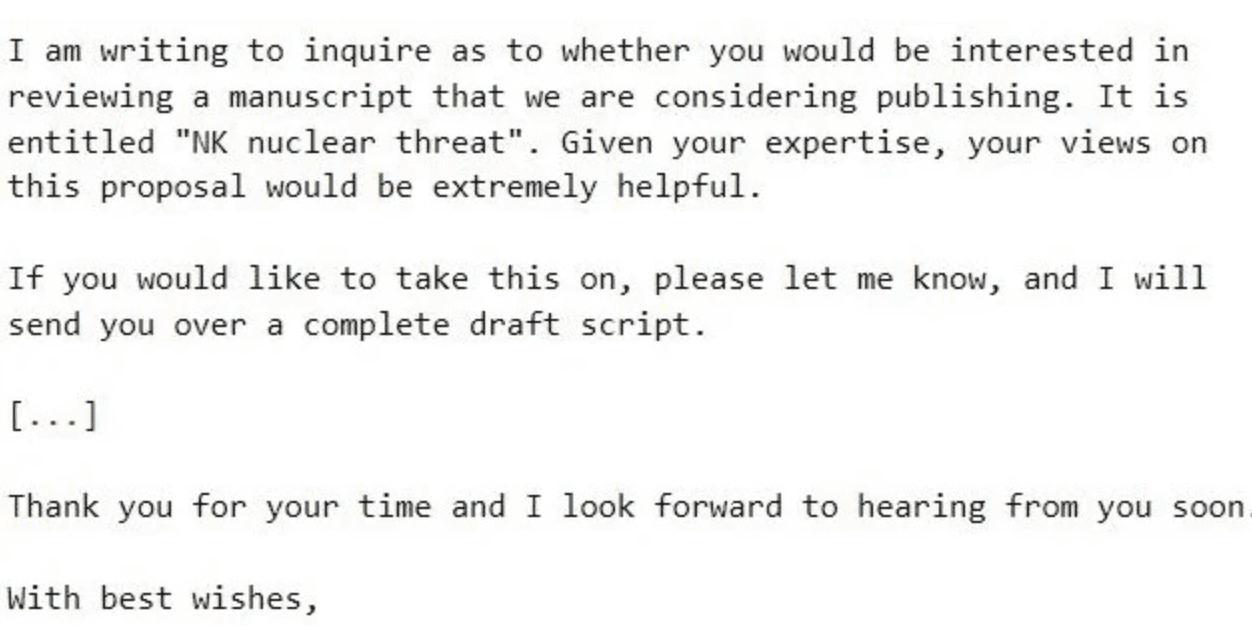 An example of an email believed to be sent by Kimsuky hackers.
An example of an email believed to be sent by Kimsuky hackers.
Aleksandar Milenkoski, senior threat researcher at SentinelOne, told Recorded Future News that this Kimsuky campaign serves as an indication of the group's growing efforts to establish early communication and foster trust with their targets prior to initiating malicious operations, including the delivery of malware.
“This approach highlights their commitment to creating a sense of rapport with the individuals they target, potentially increasing the success rate of their subsequent malicious activities,” Milenkoski said.
“By actively targeting high-profile experts in North Korean affairs and attempting to steal subscription credentials from prominent news and analysis outlets focusing on North Korea, Kimsuky demonstrates a heightened curiosity in understanding how the international community perceives developments concerning North Korea, such as the country's military activities. These actions are probably part of their broader objective to gather strategic intelligence, contributing to North Korea's decision-making processes.”
The malware, as well as the infrastructure and tactics, were what led SentinelOne to tie the activity to Kimsuky, which has operated in some form since 2021. The NSA said Kimsuky is “administratively subordinate to an element within North Korea’s Reconnaissance General Bureau (RGB)” — which is “primarily responsible for this network of cyber actors and activities.”
In the campaign, Kimsuky actors impersonated NK News to target experts, asking for analysis in long-running correspondence chains.
More specifically, the hackers pretended to be NK News founder Chad O’Carroll and used a hacker-controlled domain — nknews[.]pro — that resembled the news outlet's real website.
The first email asks victims to look over a draft of an article about North Korea’s nuclear weapons. If they get an answer, the hackers send a URL to a Google document that takes victims to a malicious website designed to steal Google login credentials.
The hackers were also seen sending malicious Office documents that contained a malware called “ReconShark” that is designed to exfiltrate victim information that is “relevant for conducting subsequent precision attacks, such as deployed detection mechanisms and hardware information.”
The group distributes emails that lure targeted individuals to log in on the malicious website nknews[.]pro, which masquerades as the authentic NK News site. The login form that is presented to the target is designed to capture entered credentials.
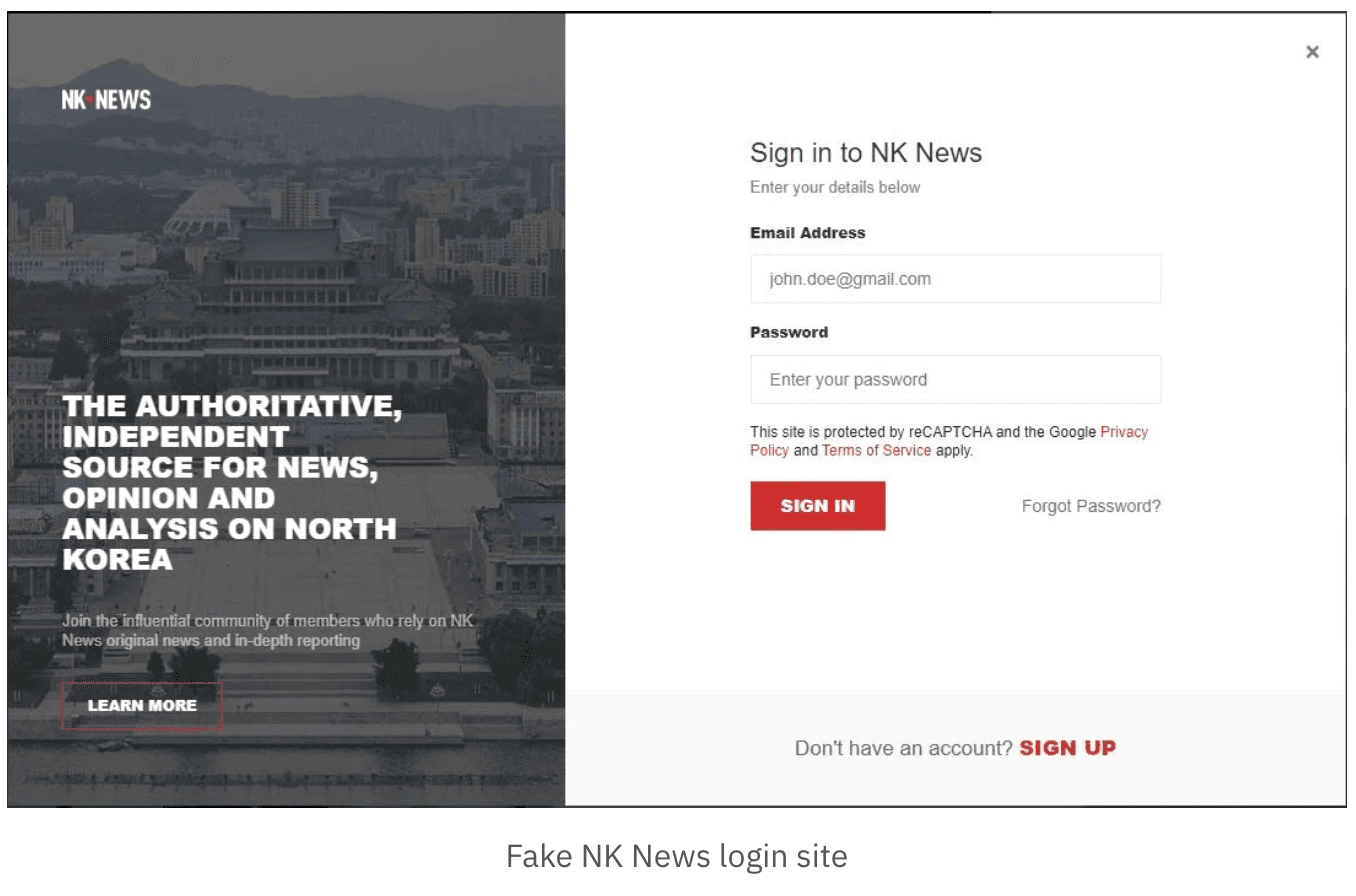 A fake login page for NK News.
A fake login page for NK News.
The group appears to be intent on seeing how the international community views news developments in North Korea, likely “contributing to North Korea’s decision-making processes,” according to SentinelOne.
NSA Director of Cybersecurity Rob Joyce said last week that North Korea state-sponsored cyber actors “continue to impersonate trusted sources to collect sensitive information.”
“These cyber actors are strategically impersonating legitimate sources to collect intelligence on geopolitical events, foreign policy strategies, and security developments of interest to the DPRK on the Korean Peninsula,” Joyce said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



