TSA issues security directive to airports, carriers after 'no-fly' list leak
The Transportation Security Administration has issued a security directive to all U.S. airports and air carriers warning them about the need for more stringent cybersecurity protections following last week’s revelation that the federal "no-fly" list had been leaked.
Outrage has grown since a Swiss national published a blog post earlier this month explaining that a copy of the "no-fly" list from 2019 was left exposed on an unsecured server, alongside other sensitive data from CommuteAir, a regional airline under United Airlines.
A TSA spokesperson told The Record that the agency is still investigating the incident but has reached out to all domestic airlines to warn them about the prospect of further breaches.
The security directive, issued Friday, "reinforces existing requirements on handling sensitive security information and personally identifiable information,” the spokesperson said.
The agency ordered the carriers to review their systems and take immediate action to ensure files were protected.
“We will continue to work with partners to ensure that they implement security requirements to safeguard systems and networks from cyberattacks,” the spokesperson said.
TSA added that CommuteAir notified the government of the breach on January 18 and reiterated that none of the agency's systems were affected.
The spokesperson noted that other federal agencies are working alongside TSA to investigate the issue.
In its incident report to Maine’s attorney general office, CommuteAir noted that 1,473 people were affected. The airline previously told The Record that employee information also was leaked in the breach.
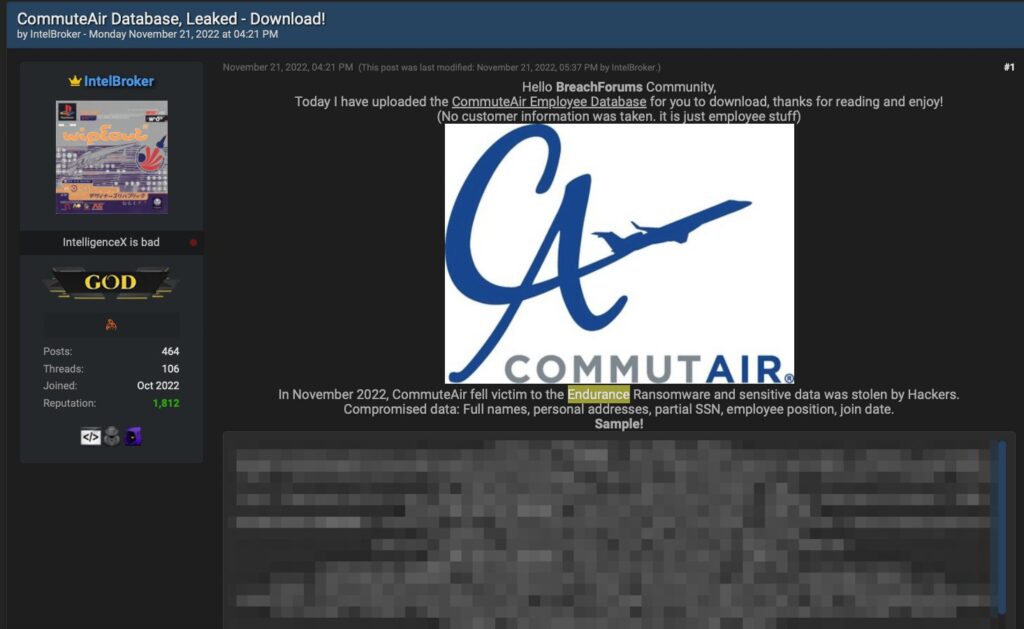
Researchers last week dug up a November dark web post from the Endurance ransomware group that claimed a database of employee information had been stolen from the company.
A CommuteAir spokesperson did not respond to questions about the ransomware attack but said there is “no evidence to support these two events are connected.”
In their letter to victims of both data breaches, the company said it is working with Mandiant to modernize their systems and investigate the incidents. They noted that the breaches were also reported to the Cybersecurity and Infrastructure Security Agency (CISA).
Rep. Dan Bishop (R-NC) expressed outrage at the leak of the list and said Congress would launch its own investigation into the incident.
Bishop and Committee on Homeland Security Chairman Mark Green (R-TN) sent a letter to TSA Administrator David Pekoske on Thursday demanding answers about how the hacker was able to access versions of the Federal Terrorist Screening Dataset, as well as a version of the "no-fly" list.
The entire US no-fly list - with 1.5 million+ entries - was found on an unsecured server by a Swiss hacker.
— Rep. Dan Bishop (@RepDanBishop) January 21, 2023
Besides the fact that the list is a civil liberties nightmare, how was this info so easily accessible?
We’ll be coming for answers. https://t.co/9sN2AhucnM
Green and Bishop noted that the hacker behind the incident told The Record that it may have been possible for them to exploit their access to the server in order to cancel or delay flights, and even switch out crew members.
“If this were to be the case, the national security implications of this are alarming. As you are keenly aware, the transportation systems sector is one of 16 critical infrastructure sectors in the United States, ensuring the free movement of people and goods essential to the American economy and way of life,” they wrote.
“The notion that such a consequential database be left unsecure is a matter concerning cybersecurity, aviation security, as well as civil rights and liberties.”
The letter included 10 questions about the breach and demanded answers from TSA by February 8.
The White House has organized meetings with aviation industry leaders in recent months as it seeks to bolster cybersecurity protections in key sectors. Another congressman has called for federal agencies to investigate cybersecurity vulnerabilities in all systems underpinning air travel.
A recent report found that there were 62 ransomware attacks on global aviation stakeholders in 2020 alone, and the value of ransom demands broke records in 2021.
The European Air Traffic Management Computer Emergency Response Team (EATM-CERT) found the number of reported cyberattacks among airline industry organizations grew 530% from 2019 to 2020. The organization has tracked dozens of attacks against airports and airlines over the last six months.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



