New ransomware task force wants more support for victims who don’t pay
A new government and industry coalition on Thursday put its weight behind a number of aggressive measures aimed at curbing ransomware, including financially supporting victims who refuse to pay attackers and making it easier to track cryptocurrency payments.
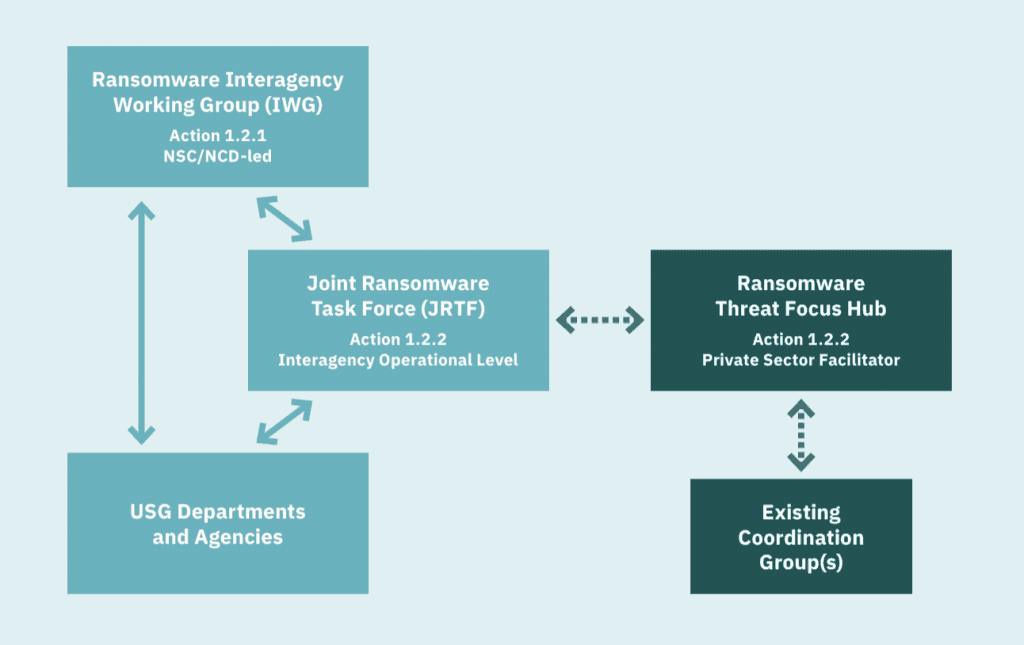
The Ransomware Task Force, which is being spearheaded by the nonprofit Institute for Security and Technology, contains dozens of members from leading cybersecurity firms and government agencies. It is a separate initiative from a Department of Justice task force that The Wall Street Journal reported on last week.
The group has been working over the last four months on an 80-page report released today that highlights the growing threat of ransomware and proposes a long list of actions that would reverse the trend that cybersecurity experts have been observing in recent years. Although ransomware has only been around for about a decade, it has gone from an attack vector that mostly held individual devices for three-figure ransoms to one that cripples organizations of all sizes unless multimillion-dollar demands are paid.
In recent years, hospitals, schools and critical infrastructure operators have faced weeks-long disruptions, and the average demand reached more than $230,000 in the third quarter of 2020, according to a report by cybersecurity firm Coveware. Some ransoms have reportedly reached tens of millions of dollars.
<style>
.overlay-marker {
width: 150px;
height: 50px;
position: relative;
top: 45px;
/* chartArea top */
right: -430px;
/* chartArea left */
z-index: 1;
}
</style>
<title>Ransomware Attacks Against Healthcare Organizations</title>
<script type="text/javascript" src="https://www.gstatic.com/charts/loader.js"></script>
<script type="text/javascript">
google.charts.load('current', {packages: ['corechart','line']});
</script>
<div class="overlay-marker">
<img src="https://www.recordedfuture.com/wp-content/uploads/logo-primary-black-2020.svg" height="15">
</div>
<div id="Health_container" style="width: 550px; height: 400px;"></div>
<script language="JavaScript">
function drawHealthChart() {
// Define the chart to be drawn.
var data = new google.visualization.DataTable();
data.addColumn('string', 'Month');
data.addColumn('number', 'Incidents');
data.addRows([
['01/20', 5],
['02/20', 6],
['03/20', 5],
['04/20', 9],
['05/20', 12],
['06/20', 4],
['07/20', 7],
['08/20', 9],
['09/20', 16],
['10/20', 13],
['11/20', 3],
['12/20', 9],
['01/21', 4],
['02/21', 7],
['03/21', 17]
]);
// Set chart options
var options = {
chart: {
title: 'Ransomware Attacks Against Healthcare Organizations',
subtitle: 'Source: Recorded Future. Graphs can be repurposed with attribution.',
},
hAxis: {
title: 'Month',
},
legend: {
position: 'none'
},
series: {
0:{color:'#fc791b'},
},
'width':550,
'height':400,
};
// Instantiate and draw the chart.
var chart = new google.charts.Line(document.getElementById('Health_container'));
chart.draw(data, options);
}
google.charts.setOnLoadCallback(drawHealthChart);
</script>
Michael Daniel, the president and chief executive of the Cyber Threat Alliance and a co-chair of the Ransomware Task Force, said the group was motivated by the increasing seriousness of the issue, coupled with a lack of countermeasures that would curb the rising trend.
“Absent action from the government and private sector, it's not going to get better by itself,” said Daniel, who served as the White House's cybersecurity coordinator and special assistant to President Barack Obama from 2012 to 2017.
The group formed around the end of 2020, and although it wasn’t driven by the new administration in the White House, task force leaders saw the Biden transition as a moment to act.
“Certainly the impression that we had a window of opportunity with a new administration played into the decision to get going,” Daniel said.
Department of Homeland Security Secretary Alejandro Mayorkas, who has initiated a handful of cybersecurity “sprints” at the department aimed at addressing issues including ransomware, is scheduled to speak today at an event formally unveiling the task force at 1pm ET. Officials from the FBI, the Cybersecurity and Infrastructure Security Agency, the U.S. Secret Service, and other agencies are also participating in the task force. Recorded Future, which publishes The Record, is also a member of the task force.
New measures
The task force introduced dozens of recommendations in its report, with the most notable ones aimed at destabilizing the underlying business model.
The group called for increased support for ransomware victims by creating emergency response authorities and establishing a Ransomware Response Fund to support victims in refusing to make ransomware payments.
“If such funding were available for ransomware victims, then cost would play a smaller role in an organization’s decision about whether to pay the ransom,” the report said. “As an incentive to invest in cybersecurity, governments could consider requiring the organization to cover some portion of the ransom as a ‘deductible.’”
Additionally, the group advocated for the creation of a Ransomware Incident Response Network that would encourage organizations to report incidents, and require organizations to share payment details with the government prior to making the payment.
To help organizations prepare for ransomware attacks, the task force mainly focused on awareness campaigns and potentially using tax breaks as an incentive for organizations to adopt secure IT services. Although the task force for the most part avoided policies that would mandate organizations to adhere to specific practices, they advocated for requirements that local governments and managed service providers adopt “baseline security measures” given the damage that attacks on these groups can cause.
In 2019, for example, the city of Baltimore was hit by a ransomware attack that disrupted critical services for weeks and cost more than $18 million to restore affected systems back to their original state. Other cities including Atlanta have faced similar struggles with ransomware attacks in recent years.
One of the more notable goals of the task force is to disrupt the ransomware business model at its core by making it more difficult to pay attackers using cryptocurrency. The group advocated for new policies that would require cryptocurrency exchanges, crypto kiosks, and over-the-counter trading desks to comply with existing Know Your Customer, Anti-Money Laundering, and Combatting Financing of Terrorism laws. Requiring these organizations to report suspicious transactions to law enforcement, as well as incentivizing information sharing between the entities and the Treasury Department, would interrupt the flow of money to ransomware operators, the task force said.
The report included a note on prohibiting ransomware payments, and said that task force members were not able to reach a consensus on the topic, “though we do agree that payments should be discouraged as far as possible,” it said.
Daniel predicts that one of the biggest hurdles the task force will have to overcome is getting certain policies turned into law. But he said there’s some appetite in Capitol Hill for cybersecurity action, especially after incidents like the SolarWinds breach and Microsoft Exchange vulnerabilities affected government agencies.
“A very large number of recommendations would require legislative action, and that’s been challenging in the U.S. for a while now,” Daniel said. “That’s going to take time—the best time to have started this was four years ago, but the next best time is now.”
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



