New JavaScript malware works as a "RAT dispenser"
Cybersecurity experts from HP said they discovered a new strain of JavaScript malware that criminals are using as a way to infect systems and then deploy dangerous remote access trojans (RATs).
Cleverly named RATDispenser, the malware has been distributed in the wild for at least three months in the form of email messages carrying malicious file attachments.
These files abuse the classic double-extension trick (filename.txt.js) to pose as text files but run JavaScript code when users try to open them.
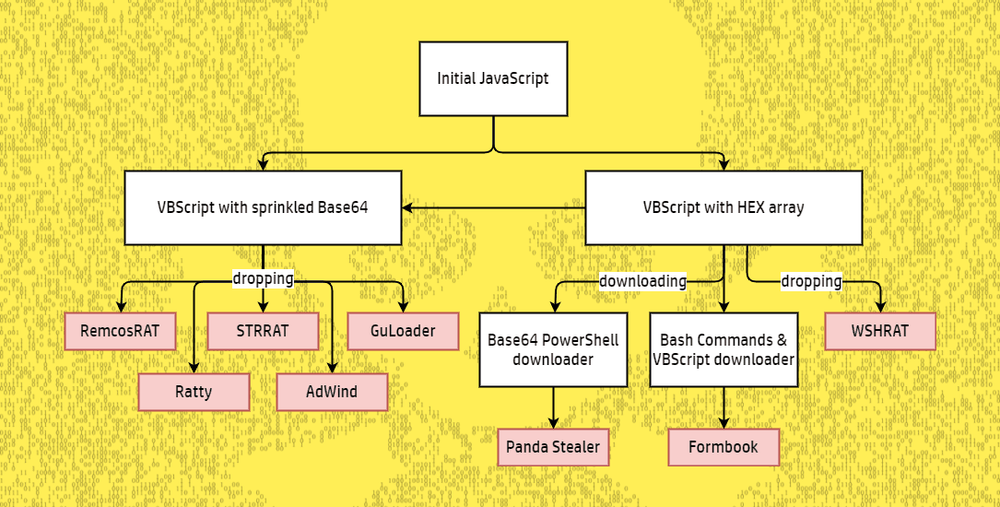
Once this happens, HP says the RATDispenser malware decodes itself and runs a self-contained VBScript file that then installs a commodity remote access trojan on the infected device.
Over the past three months, HP said the malware had been used to drop at least eight different RAT strains, such as STTRAT, WSHRAT, AdWind, Formbook, Remcos, Panda Stealer, GuLoader, and Ratty.
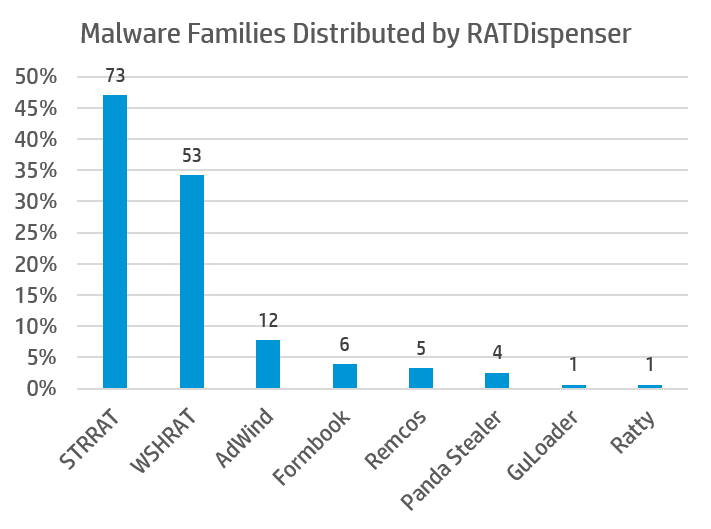
"The variety in malware families, many of which can be purchased or downloaded freely from underground marketplaces, and the preference of malware operators to drop their payloads, suggest that the authors of RATDispenser may be operating under a malware-as-a-service business model," Patrick Schläpfer, malware analyst at HP's Wolf Security, said in a report published this week.
Schläpfer said HP has discovered around 155 samples of this new malware, spanning across three different versions, suggesting the malware may be in its first months of development.
Schläpfer described RATDispenser as a dropper, a type of malware used to install other threats. Droppers are different from loaders (also known as downloaders), as they contain the final payload in their body and don't communicate with a command and control server, meaning they are less versatile but slightly stealthier.
Indicators of compromise are available in the HP Wolf Security report.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.