Most K-12 apps send kids’ personal info to advertisers and other third parties, study finds
The COVID-19 pandemic has pushed schools around the country to adopt and rely heavily on new technology. But a study published today from the nonprofit Me2b Alliance suggests that these tools might be syphoning children's’ data and sending them to advertisers like Google and Facebook without informing users or parents.
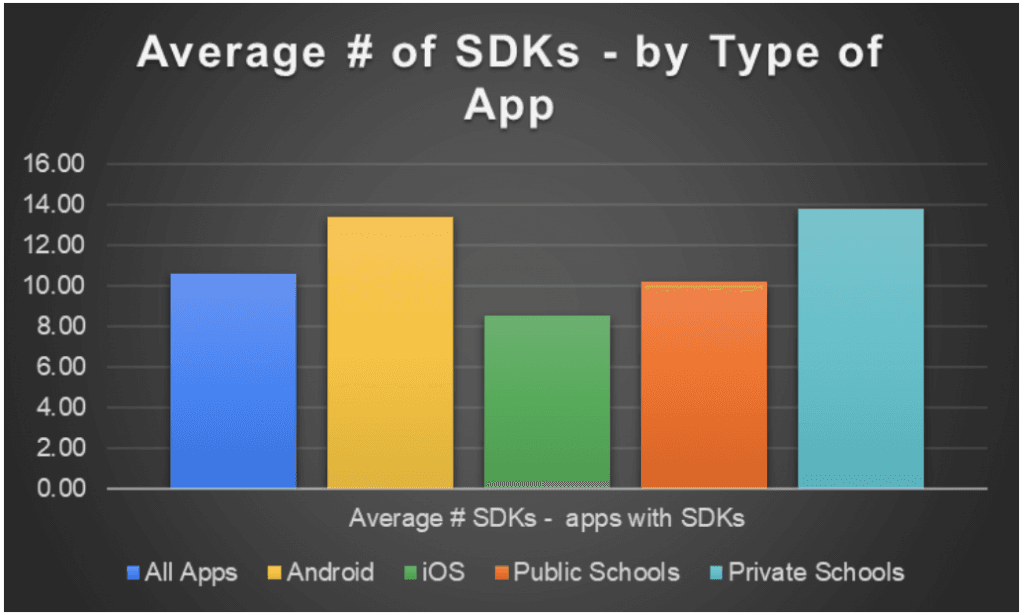
The group audited a random sample of 73 apps from 38 schools in 14 states across the country, and found that 60% of these apps were sending student data to a variety of third parties. Roughly half of the apps were sending student data to Google, while 14% were sending data to Facebook. On average, there were 10.6 third-party data channels per app.
The study evaluated these apps by examining software development kits, or SDKs, which provide developers with pre-packaged code modules. SDKs generally run behind-the-scenes as soon as someone opens the app, and users are rarely asked for consent before an SDK sends data back to its third-party developer. SDK providers use the data for a variety of reasons, including performing vital app functions, collecting analytics, advertising, and monetization.
The study identified 56 unique SDKs used by the apps, most of which were owned by recognizable tech companies like Google (12), Facebook (7), Apple (7), Amazon (3), Square (3), and Twitter (2). 100% of the Android apps that included SDKs sent data to Google, the report found.
“There are a lot of schools that have their own custom apps, and they’re leaning on these apps more because of the pandemic,” said Zach Edwards, who is in charge of data integrity testing for the Me2b Alliance. “We realized they don’t seem to have internal standards to remove advertising SDKs from these apps. As soon as we dipped our toes into it we realized it was a deeply problematic trend across the board.”
The group characterized SDKs based on their function—from medium-risk for SDKs that were designed for utility purposes to very high-risk for SDKs that were designed for advertising and monetization and routinely sync with hundreds of partners to track users across services and devices.
In total, 18% of the apps included what Me2ba deems very high-risk, though none of the private school apps sampled in the study included any of very high-risk third parties. Additionally, public schools in general were found to be more likely to send student data to third parties than private schools, with 67% of public school apps sending data vs. 57% of private school apps.
All apps examined by Me2ba were designed to access the following types of information:
- Identity—also known as a Mobile Advertising Identifier (MAID), or the "Ad ID" on Android and "IDFA" on iOS
- Calendar
- Contacts
- Photos/Media/Files
- Location
- USB Storage
Several apps were additionally accessing user devices’ cameras, microphones, and device ID and call information.
Apps and kids’ privacy
The study is just the latest research to examine how tech companies potentially syphon kids’ data for advertising and marketing purposes. Several studies in recent months have looked at apps that were tagged as “educational” in app stores, finding that they routinely send location information and other sensitive data to third parties including Facebook and Google.
Edwards said that those studies are valuable, but by only looking at “educational” apps they also pull in many adult learners. Me2ba specifically looked at school apps, where developers and app stores would know that the intended user is a child.
Additionally, most of the apps examined in the Me2ba study were funded by taxpayers because they were custom created for schools—they had no stated goal to profit off user data.
Edwards said one likely reason why these apps are sending data to third parties is because there’s a lack of auditing by both the schools and the app stores.
“If you’re an outsourced developer and you’re confident a school isn’t going to audit your work, you might install an advertising SDK and sell or rent the audiences for an extra $100 a month,” he said. “Otherwise, we can’t figure out why some of these SDKs would have been installed.”
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.