Espionage malware targeted telecoms in Middle East using Microsoft, Google, Dropbox tools
An espionage campaign targeting telecommunications providers across the Middle East hid its activities through a range of popular tools from Microsoft, Google and Dropbox, according to a report released Thursday.
Researchers at cybersecurity company SentinelOne named the campaign “WIP26” — work in progress — because they were unable to attribute it to any actor or country.
But the campaign stood out because it relied heavily on the exploitation of public cloud infrastructure that allowed the hackers to evade detection by making malicious traffic look legitimate, the researchers said.
Microsoft Azure and Dropbox instances were used to hold stolen data and host malware that abused Microsoft 365 Mail and Google Firebase services.
“The WIP26 activity is initiated by precision targeting of employees through WhatsApp messages that contain Dropbox links to a malware loader,” the researchers said. “Tricking employees into downloading and executing the loader ultimately leads to the deployment of backdoors that leverage Microsoft 365 Mail and Google Firebase instances” as command-and-control servers for the malware.
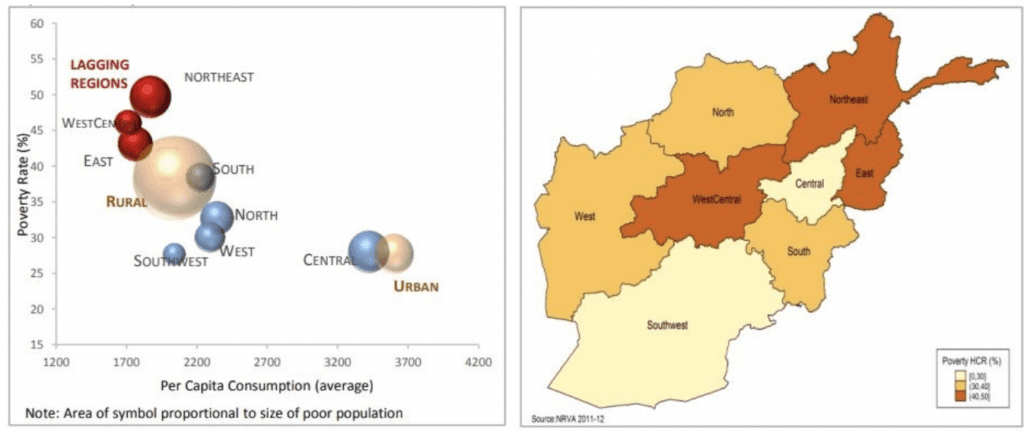
The WhatsApp messages contained Dropbox links that had files about poverty-related issues in Afghanistan. The backdoors — code used to break into systems — masqueraded as PDF editors, browsers or other software.
One of the backdoors that came with the Dropbox files — CMD365 — was used for “reconnaissance, privilege escalation, staging of additional malware, and data exfiltration” according to SentinelOne.
“The exfiltrated data included users’ private browser data and reconnaissance information on particular high-value hosts in the victim’s network. This is a typical precursor to the subsequent targeting of these hosts,” they added.
SentinelOne said it notified Microsoft, Google and Dropbox about the campaign and explained that telecoms are frequent targets for espionage because they carry troves of sensitive information.
They also allow hackers to target the private information of specific users and gain specific data on networks of high value.
The company worked on the report with German security firm QGroup and said the perpetrators of the campaign made several mistakes that gave researchers insight into their work, including an exposed JSON file that is still publicly accessible.
Part of why government-backed hackers use public cloud infrastructure is so that their activity blends into the typical traffic seen by network defenders.
“For example, the North Korean APT 37 (InkySquid) has used the Microsoft Graph API for C2 operations. Further, similar to CMD365, the SIESTAGRAPH backdoor, used in the REF2924 intrusion set targeting the Foreign Affairs Office of an ASEAN member, leverages the Microsoft Graph API to access Microsoft 365 Mail for C2 communication,” SentinelOne explained.
The researchers highlighted another campaign targeting nonprofits in Kashmir and Pakistani government officials that abused Google Firebase Cloud Messaging to stage malware. Russian APT group Fancy Bear has also been seen leveraging Microsoft OneDrive in attacks.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



