Microsoft ties Vice Society hackers to additional ransomware strains
Microsoft tied hackers with the Vice Society ransomware gang to several ransomware strains on Tuesday, noting that the group has been behind a wave of attacks on primary schools and colleges across the world.
Microsoft Security Threat Intelligence said Vice Society hackers — which they track as DEV-0832 — have been seen using ransomware payloads including BlackCat, QuantumLocker, and Zeppelin.
Even though the extension seen after a victim’s files are encrypted carry the Vice Society name, Microsoft said the group’s latest attacks actually involve a variant of Zeppelin. The FBI said last year that Zeppelin was one of the five most commonly seen ransomware strains targeting U.S. organizations, based on data from the FBI’s Internet Crime Complaint Center (IC3).
Microsoft noted that in several cases, the Vice Society group did not actually deploy ransomware, instead simply extorting victims using data that had been exfiltrated and stolen.
“While many ransomware groups have shifted away from branded file extensions in favor of randomly generated ones, DEV-0832 incorporated branding with their Vice Society variant using .v-s0ciety or .v-society file extensions,” Microsoft explained, adding that in late September the group modified its ransomware payload to a variant dubbed RedAlert, with a .locked file extension.
The group has been active since at least June 2021, and its latest attacks between July and October 2022 have “heavily impacted the education sector.”
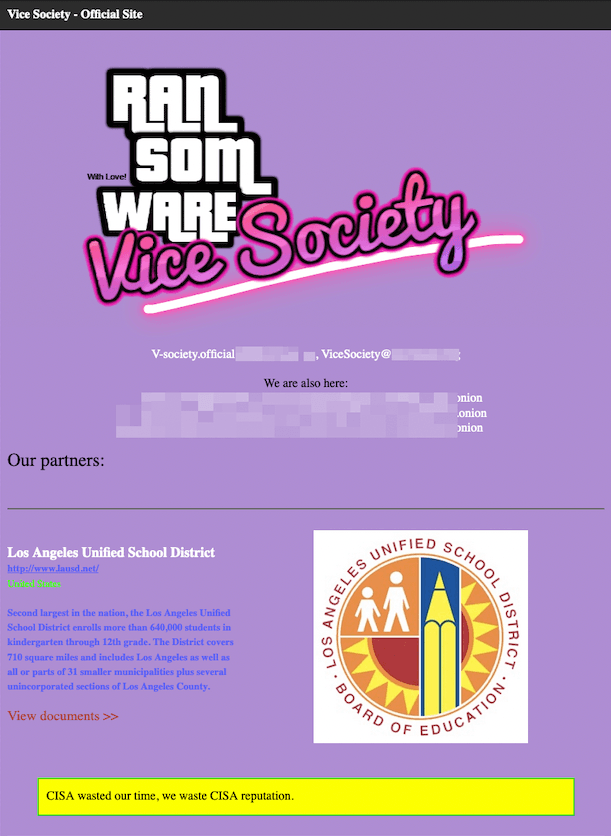
The FBI, Cybersecurity and Infrastructure Security Agency (CISA) and other agencies noted in an alert in September that Vice Society has “disproportionately” attacked dozens of educational institutions over the last year and stepped up its level of attacks this fall.
The group publicly took credit for a crippling attack last month on the Los Angeles Unified School District — the second-largest school district in the country.
Microsoft noted on Tuesday that the group “continues to focus on organizations where there are weaker security controls and a higher likelihood of compromise and ransom payout.”
Emsisoft threat analyst Brett Callow noted that one part of the Microsoft report that stood out to him was the assessment that Vice Society explicitly focuses on the education sector.
“Groups are opportunistic and make a buck whenever and wherever they can, with no preference for any particular sector,” he said. “Vice Society is the only group I can think of that does seem to have a preference.”
‘De-RaaSing of ransomware’
The company said it identified multiple campaigns over the past year that can be attributed to Vice Society based on several unique identifiers.
The group makes a point of damaging victim systems so significantly that they cannot recover without paying a ransom.
In one instance, Microsoft said it saw Vice Society take over two domain administrator accounts and reset user passwords of over 150,000 users — effectively locking out legitimate users before deploying ransomware to some devices. This action made it nearly impossible for the organization to initiate remediation processes and incident response.
Another July 2022 incident saw the group initially deploy the QuantumLocker ransomware and then five hours later deploy the Zeppelin ransomware. Microsoft said the incident “might suggest that DEV-0832 maintains multiple ransomware payloads and switches depending on target defenses or, alternatively, that dispersed operators working under the DEV-0832 umbrella might maintain their own preferred ransomware payloads for distribution.”
“The shift from a ransomware as a service (RaaS) offering (BlackCat) to a purchased wholly-owned malware offering (Zeppelin) and a custom Vice Society variant indicates DEV-0832 has active ties in the cybercriminal economy and has been testing ransomware payload efficacy or post-ransomware extortion opportunities,” Microsoft explained.
An August 2022 attack saw the group use an exploit for CVE-2022-24521 — a vulnerability affecting Windows Common Log File System Driver that CISA said in April was being exploited. Vice Society has also been seen by Microsoft exploiting the PrintNightmare vulnerability as a way to escalate their access to a system.
Several cybersecurity researchers said the report highlights a recent trend they have noticed, of ransomware groups having access to different ransomware variants. Emsisoft’s Callow said Vice Society’s actions appear to indicate that it has some form of a relationship with other ransomware operations, potentially beyond the scope of a typical affiliate-type arrangement.
Recorded Future ransomware expert Allan Liska corroborated Microsoft’s findings, agreeing that sometimes Vice Society deploys their own ransomware and other times they use the Black Cat variant — which was seen used in several attacks on U.S. universities and colleges earlier this year.
“I think it really shows that the distinction between affiliate and ransomware group is extremely fluid. Affiliates jump from ransomware variant to ransomware variant all the time, depending on the situation,” Liska said.
“We, as an industry, have to get better at focusing on the actor behind the attack and not just conflating the ransomware name with the group. This is not easy to do, most of the time we don’t have the necessary insight to make those distinctions.”
Liska explained that many ransomware groups now have access to other ransomware variants, leading to what he says is a “De-RaaSing of ransomware.” Due to the leak of so many ransomware code bases, affiliates “are really the ones with power now,” according to Liska.
“You only need to use a RaaS offering in specific situations,” he said. “I mean why share the cut with a RaaS group if you can keep it all?”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.