Microsoft accuses China of abusing vulnerability disclosure requirements
Microsoft on Friday accused state-backed hackers in China of abusing the country’s vulnerability disclosure requirements in an effort to discover and develop zero-day exploits.
In July 2021, the Cyberspace Administration of China (CAC) issued stricter rules around disclosing vulnerabilities for companies operating within its borders.
Concerns that the Chinese military would exploit vulnerabilities before reporting them more broadly was an integral part of the investigation into the handling of the widespread Log4j vulnerability. Reports emerged earlier this year that the Chinese government had sanctioned Alibaba for reporting the vulnerability to Apache first, rather than to the government.
The Homeland Security Department’s Cyber Safety Review Board spoke with the Chinese government and “did not find evidence” that China used its advanced knowledge of the weakness to exploit networks.
But in a 114-page security report released on Friday, Microsoft openly accused the Chinese government of abusing the new rules and outlines how state-aligned groups have increasingly exploited vulnerabilities globally since they were implemented.
“The increased use of zero days over the last year from China-based actors likely reflects the first full year of China’s vulnerability disclosure requirements for the Chinese security community and a major step in the use of zero-day exploits as a state priority,” Microsoft said.
“While we observe many nation state actors developing exploits from unknown vulnerabilities, China-based nation state threat actors are particularly proficient at discovering and developing zero-day exploits.”
Microsoft said the rules went into effect in September 2021 and marked “a first in the world for a government to require the reporting of vulnerabilities into a government authority for review prior to the vulnerability being shared with the product or service owner.”
The tech giant added that the regulation “might enable elements in the Chinese government to stockpile reported vulnerabilities toward weaponizing them.”
China’s Foreign Ministry did not respond to requests for comment about Microsoft’s claims.
Microsoft went on to pin the abuse of specific zero-day vulnerabilities on Chinese government hackers, including SolarWinds vulnerability CVE-2021-35211, two vulnerabilities affecting Zoho products and CVE-2021-42321, a zero-day exploit for a Microsoft Exchange vulnerability.
Microsoft added that a “China-affiliated actor” likely had the zero-day exploit code for CVE-2022-26134 — a vulnerability affecting Atlassian products — four days before the vulnerability was publicly disclosed on June 2. The actor “likely leveraged it against a US-based entity.”
Global hacking campaigns
In its report, Microsoft accuses China of conducting prolific global hacking campaigns against both allies and adversaries.
The attacks, they wrote, spanned Africa, the Caribbean, the Middle East, Oceania, and South Asia, with a particular focus on countries in Southeast Asia, and the Pacific Islands.
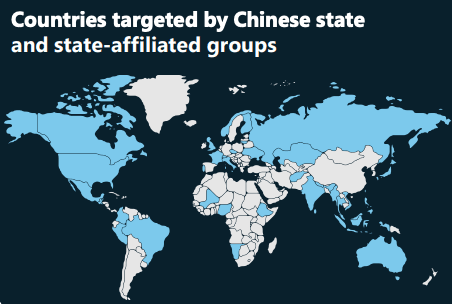
“In line with China’s Belt and Road Initiative [BRI] strategy, China-based threat groups targeted entities in Afghanistan, Kazakhstan, Mauritius, Namibia, and Trinidad and Tobago,” Microsoft said.
Trinidad and Tobago was the first Caribbean country to join the initiative in 2018, signing construction deals at the outset. Nonetheless, Chinese hackers targeted the country’s networks throughout 2021 and conducted reconnaissance activities against one of its government agencies in March 2022, according to Microsoft.
Countries across Southeast Asia and throughout the Pacific were also targeted widely, according to Microsoft, which confirmed reports from several other cybersecurity companies that tracked widespread attacks by Chinese state-backed hackers.
State hackers targeted an energy company and an energy-associated government agency in Vietnam in January, while also going after an Indonesian government agency that same month.
Another hacking group allegedly connected to the Chinese government compromised more than 100 accounts affiliated with a prominent intergovernmental organization (IGO) in the Southeast Asia region in February and March. That attack coincided with an announcement that the IGO would be meeting with the United States and other regional leaders.
A hacking campaign targeting the Solomon Islands also stood out to Microsoft researchers, who noted that the attacks started in May, just one month after China signed a security agreement with the island nation that allowed the country to deploy armed police and military.
Malware from a China-based hacking group was found on Solomon Islands government systems in May. Other hacks targeted organizations in Papua New Guinea as well, according to Microsoft.
In December 2021, Microsoft obtained a court warrant that allowed it to seize 42 domains used by a Chinese cyber-espionage group in recent operations that targeted organizations in the U.S. and 28 other countries.
The tech giant noted that since that action, the same Chinese hacking group has sought to establish the access it lost. Between March and May of this year, the group was able to re-compromise at least five government agencies across the globe.
“As China continues to establish bilateral economic relations with more countries— often in agreements associated with BRI— China’s global influence will continue to grow,” Microsoft said.
“We assess Chinese state and state-affiliated threat actors will pursue targets in their government, diplomatic, and NGO sectors to gain new insights, likely in pursuit of economic espionage or traditional intelligence collection objectives.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



