Man who bribed AT&T employees to install malware on the company's network gets 12 years in prison
A Pakistani man who bribed AT&T employees to install malware on the company's internal network has been sentenced today to 12 years in prison after he illegally unlocked more than 1.9 million phones, causing the US telco losses in excess of $201 million.
Muhammad Fahd, 35, a citizen of Pakistan and Grenada, paid more than $1 million in bribes to AT&T employees in the mid-2010s, according to court documents.
Working with a now-deceased co-conspirator, Fahd began his scheme in the summer of 2012 when he approached AT&T employees working in the company's call center in Bothell, Washington.
Using Facebook as a means to communicate, Fahd promised large payments of money if call center employees agreed to unlock phones so they could be sold and used outside AT&T's network.
To receive their bribes, Fahd told AT&T employees "to create shell companies and open business banking accounts in the names of the shell companies," per the court docs.
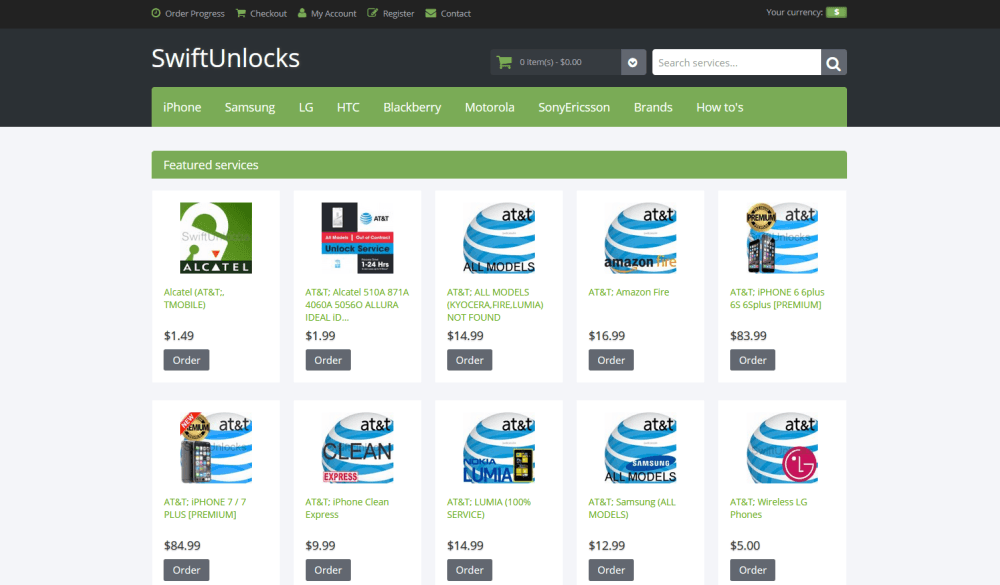
Fahd recuperated the bribes by selling phone unlocking services through the now-defunct SwiftUnlocks.com website [archived].
But the scheme lasted only for a few months, until April 2013, when AT&T implemented a new phone unlocking procedure and call center employees Fahd had bribed either left or were fired by AT&T.
At this point, seeking to go around AT&T's new systems, the US Department of Justice said Fahd hired a developer to write a piece of malware.
Fahd then bribed another employee to install the malware inside AT&T's Bothell call center.
An initial version of the malware worked as a basic keylogger, collecting information from inside the network, including network layout and employee credentials.
A second version was more sophisticated and deployed at a later stage, acting as a remote access tool and allowing Fahd easy access to AT&T's internal applications.
The mobile operator caught that something was wrong when engineers detected a large number of phone unlock operations from its Bothell call center.
A 2015 internal investigation ended up with AT&T firing and suing former employees on accusations of installing malware on its network, with the company unearthing the connection between the fired employees and the SwiftUnlocks website.
AT&T's forensic analysis shows the total number of cellular telephones fraudulently unlocked by members of the scheme was 1,900,033 phones. AT&T has further determined that the loss it suffered because customers, whose cellular phones were illegally unlocked, failed to complete payments for their cellular telephones was $201,497,430.94.
US Department of Justice
AT&T also filed a separate complaint with the FBI, which conducted its own parallel investigation, and eventually tracking the entire scheme to Fahd and his co-conspirator, Ghulam Jiwani.
US officials filed charges against the two in 2017. Fahd was arrested in Hong Kong in 2018 and extradited to the US in August 2019. He pleaded guilty in September 2020.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.


