"King of fraud" sentenced to 10 years in prison for role in Methbot/3ve botnet
A US judge sentenced a Russian national to 10 years in prison for running Methbot, a giant ad fraud botnet that stole more than $7 million from ad publishers and ad networks between 2014 and 2018.
The sentence concludes a controversial case during which Aleksandr Zhukov, 41, sustained his innocence until the last moment.
Zhukov was arrested in November 2018 while traveling to Bulgaria on an FBI-issued arrest warrant.
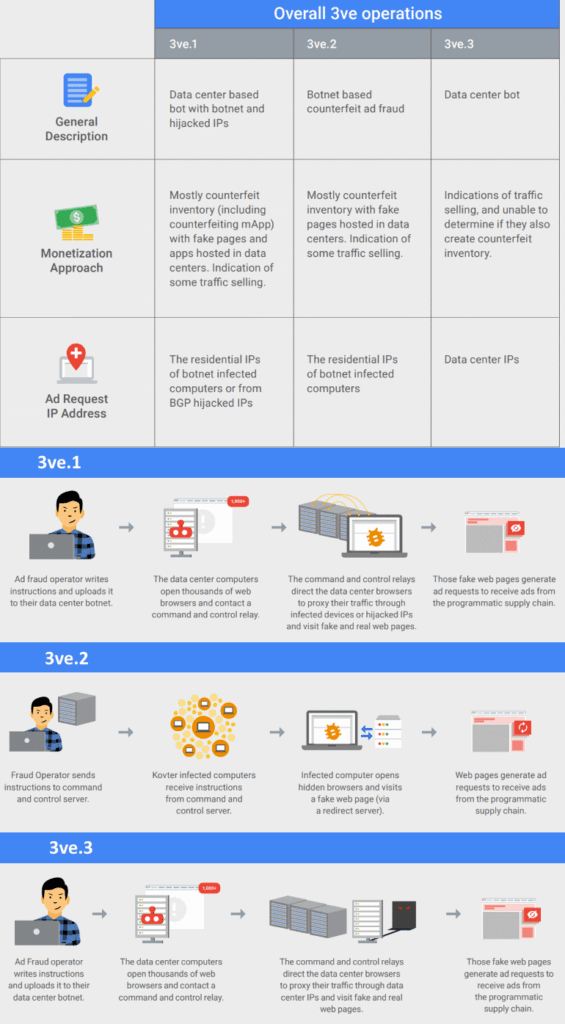
He was formally charged a week later when the FBI, together with Google and 20 tech and security firms, dismantled Zhukov's operation, a giant botnet that ran across infected devices and legitimate data centers.
The self-proclaimed "king of fraud"
Tracked under names such as 3ve, Methbot, Boaxxe, and Miuref, Zhukov is believed to have run one of the largest ad fraud botnets ever created, generating at one point in 2016 between $3 million and $5 million in revenue per day.
According to court documents [PDF], Zhukov hired programmers to help him build and manage this operation, which he disguised as a legitimate advertising network named Media Methane.
Prosecutors said Zhukov kept 75% of these profits and referred to himself as the "king of fraud" and his employees as "my developers."
But instead of running an actual advertising company, prosecutors said that Zhukov created thousands of fake websites where he loaded ads from legitimate publishers.
These websites ran on more than 2,000 servers rented across data centers and had no real visitors. Instead, Zhukov's team used automated tools to simulate real visitors.
Prosecutors said Zhukov often leased IP addresses for this activity, and in other cases, he also hijacked legitimate IP addresses from their legitimate owners.
In a report published after the botnet's takedown, Google said that at its peak, the Methbot/3ve operation generated over three billion fraudulent daily ad bid requests. It also employed more than 60,000 accounts selling fraudulent ad inventories, operated over 10,000 fake websites for showing the ads, ran over 1,000 servers, and controlled over one million IP addresses for hiding the various 3ve bots.
According to a White Ops (now Human) report, the scheme primarily targeted video ads, which yielded a higher profit when viewed by the fake Methbot users.
"I'm weaponless soldier in front of a tank with name FBI."
Aleksandr Zhukov
Zhukov maintained his innocence since he was first brought into custody. He pleaded not guilty in early 2019.
Throughout the trial, he claimed to have developed artificial intelligence tools to run an "absolutely legal" advertising business when confronted with the charges.
He was also dissatisfied with his defense and also asked the judge presiding over his case for a new attorney later that year, writing in a note, "I'm weaponless soldier in front of a tank with name FBI."
He was found guilty in a jury trial and convicted in May 2021 of wire fraud conspiracy, wire fraud, money laundering conspiracy, and money laundering.
Yesterday, he was sentenced to 10 years in prison and ordered to pay $3,827,493 in forfeiture.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



