JBS ransomware attack likely came from a Russian group, White House says
A cyberattack that shut down some operations at JBS, a major meat processor with plants across Australia and the Americas, is believed to be a ransomware incident originating from a criminal organization based in Russia, the White House said Tuesday.
JBS first disclosed details about the attack on Monday, calling it “an organized cybersecurity attack” that affected some of the servers supporting its IT systems in North America and Australia. According to press reports, White House spokeswoman Karine Jean-Pierre told reporters on Air Force One that the Brazil-based meatpacker notified the Biden administration Sunday that it was a ransomware attack.
Principal Deputy Press Secretary @K_JeanPierre announces the FBI is investigating a ransomware attack on JBS, the world’s largest meat supplier.
— The Recount (@therecount) June 1, 2021
The company says the ransom demand came from a criminal organization likely based in Russia. pic.twitter.com/pD2NIVNPui
“The White House is engaging directly with the Russian government on this matter and delivering the message that responsible states do not harber ransomware criminals,” Jean-Pierre said, adding that the FBI is investigating the incident.
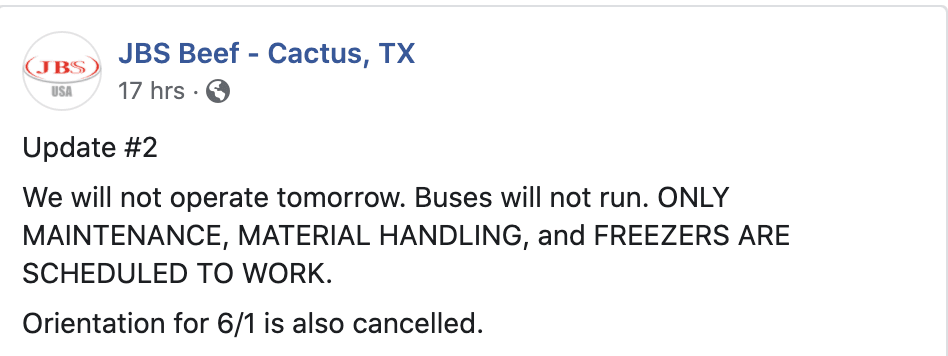
The company employs tens of thousands of workers in the U.S., and slaughters more than 20% of the country’s cattle, according to industry estimates. Although the scope of the attack is still unclear, several meat processing plants said on Facebook that they were cancelling shifts on Monday and Tuesday.
“IMPORTANT ANNOUNCEMENT! A-Shift Slaughter and Production areas will NOT be running on Monday May 31st,” JBS Canada said on its Facebook page. Similar posts were added Tuesday.
A spokesperson for JBS did not immediately respond to The Record’s request for comment.
“The company took immediate action, suspending all affected systems, notifying authorities and activating the company's global network of IT professionals and third-party experts to resolve the situation. The company’s backup servers were not affected, and it is actively working with an Incident Response firm to restore its systems as soon as possible,” the company said in its Monday statement. It added that the company is not aware of any evidence that customer, supplier, or employee data has been compromised or misused.
The incident comes less than a month after suspected Russian hackers infected Colonial Pipeline with ransomware, shutting down fuel distribution along the U.S. East Coast for several days.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



