Jailed Indian activist was targeted by state-linked hacking group, report says
California-based cybersecurity firm SentinelOne released an investigative report Wednesday revealing the decade-long work of hackers known to plant incriminating evidence on the devices of activists, human rights defenders, journalists, academics, and lawyers in India.
The findings were a result of a 2018 violent clash between government critics and supporters near Bhima Koregaon, India, which furthered the country’s racial and political strains. Following the strife, law enforcement carried out raids and arrests against a number of dissidents, in which they found devices containing evidence of terrorism plans and ideals.
Of those charged was activist and human rights defender, Rona Wilson. In 2021 the computer forensics service Arsenal Consulting released findings that showed Wilson’s computer was compromised, and the incriminating files were planted by two different groups — the cyberespionage group known as SideWinder and another actor dubbed ModifiedElephant.
One glaring commonality between the two threat actors caused alarm bells to ring for SentinelOne — they both shared the same hacking infrastructure.
Cybersecurity researchers have assumed ModifiedElephant to be a state-sanctioned political espionage group for some time and SentinelOne’s investigation adds evidence to that theory.
“The objective of ModifiedElephant is long-term surveillance that at times concludes with the delivery of ‘evidence’ — files that incriminate the target in specific crimes — prior to conveniently coordinated arrests,” the report says.
The phishing campaigns conducted by the threat actor proved not to be an isolated incident but rather had targeted hundreds of groups and individuals since at least 2012.
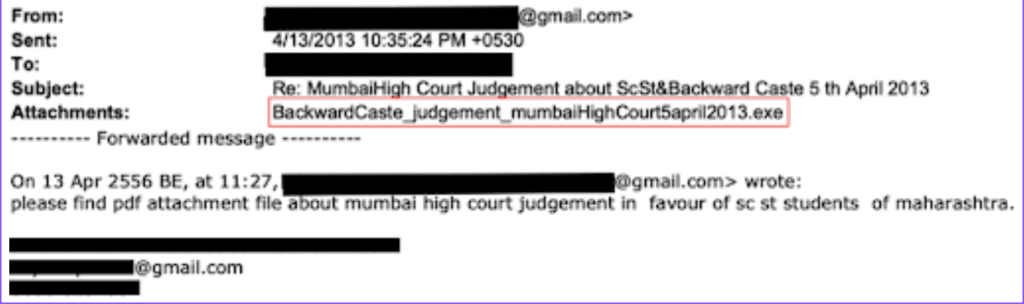
Like most cyberespionage groups, ModifiedElephant’s tactics evolved over time to become increasingly sophisticated. However, their primary method uses spearphishing emails that contain attachments which are then planted through weaponized Microsoft Office documents.
The report further details how the group’s approach has evolved since 2013.
Spearphishing emails allow the attacker to create a seemingly legitimate email account using free service providers like Yahoo and Gmail, a long history of forwarding, listed email recipients, and a curated body of content that utilizes relevant keywords (activism, climate change, news, and politics).
The group used well-known malware like NetWire and DarkComet remote access trojans (RAT). “The malware most used by ModifiedElephant is unsophisticated and downright mundane, and yet it has proven sufficient for their objectives — obtaining remote access and unrestricted control of victim machines,” the report says.
Although SentinelOne cannot define the relationship between ModifiedElephant and other threat actors like SideWinder, there is strong enough evidence that shows overlap — whether it be a common controlling entity or it be that they work in conjunction with one another. There have been several instances in which targets of ModifiedElephant have also been targets of mobile surveillance spyware. Furthermore, ModifiedElephant’s email payload infrastructure overlaps with the espionage network called Operation Hangover which surveils those of interest to Indian national security.
The findings within the report don’t provide definitive answers as to what Rona Wilson’s investigation means on a bigger scale, but it makes clear that the activities of ModifiedElephant and the interests of the Indian government do not just relate by coincidence.
“Many questions about this threat actor and their operations remain; however, one thing is clear: Critics of authoritarian governments around the world must carefully understand the technical capabilities of those who would seek to silence them,” the report states.
Emma Vail
Emma Vail is an editorial intern for The Record. She is currently studying anthropology and women, gender, and sexuality at Northeastern University. After creating her own blog in 2018, she decided to pursue journalism and further her experience by joining the team.


