Iran-linked cyberspies expand targeting to medical researchers, travel agencies
A cyberespionage group aligned with Iran’s Islamic Revolutionary Guard Corps (IRGC) has been observed attacking new targets over the last two years, including medical researchers, an aerospace engineer and even a Florida-based realtor.
The group, tracked as TA453 but also commonly referred to as Phosphorus, Charming Kitten and APT42, has historically gone after Middle East researchers and academics, policymakers, journalists and dissidents, according to a report published Wednesday by security firm Proofpoint. But deviations in both their targeting and tactics in recent months suggest the group has shifted its operations to support the IRGC’s intelligence needs.
“They are attacking new targets with new techniques and with more hostile intent,” Proofpoint Vice President of Threat Research and Detection Sherrod DeGrippo told The Record in an email. “All this serves as a window into aims of the Islamic Revolutionary Guard Corps and the flexible mandate under which TA453 works.”
Proofpoint said it started to observe differences in TA453’s targeting in late 2020, namely when the group was observed attacking senior professionals at various medical research organizations in the U.S. and Israel with credential harvesting attacks. The targets mainly had backgrounds in genetics, oncology and neurology.
In July and August 2021, Proofpoint researchers identified spear phishing attacks targeting scholars with backgrounds in women’s and gender studies at various North American universities. Around the same time, “multiple Iranian travel agencies operating out of Tehran” were targeted by a credential harvesting operation launched by the group — likely to collect details about the movement of Iranians outside Iran.
Another incident that deviated from the group’s traditional targeting was a February 2022 attack that centered on a Florida-based realtor “involved in the sale of multiple homes located near the headquarters of US Central Command.” CENTCOM is the U.S. Combatant Command responsible for Middle East military operations.
In addition to the shift in targeting, Proofpoint researchers said TA453 has adopted new techniques in recent months. For example, the group historically created email accounts and used them to send phishing emails to potential victims, but has recently started using compromised accounts to target individuals.
In one example from 2021, a press secretary for an unnamed U.S. government official who publicly commented on the Iran nuclear deal was targeted via a compromised email account from a local reporter.
Other techniques include the use of GhostEcho, a backdoor that’s used to “deliver follow-on espionage focused capabilities” once the group gains access to a victim, and leveraging a persona named “Samantha Wolf” for confrontational social engineering lures.
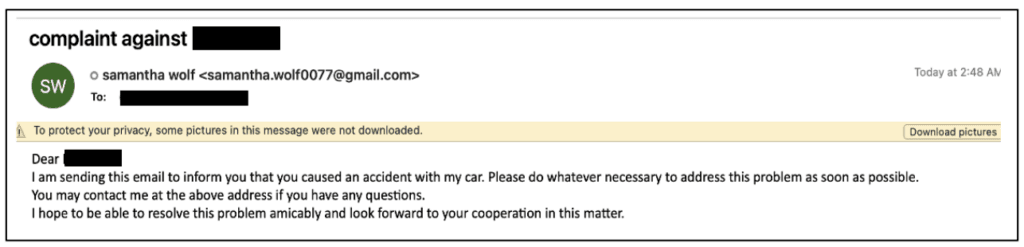
In one email lure shared by Proofpoint, the Wolf persona says the recipient has "caused an accident with my car" and needs them to "address this problem as soon as possible."
“In late 2022, Samantha encountered even more people with whom she has taken umbrage, sending additional complaint-themed benign conversation emails to senior US and European government officials,” the researchers said.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



