If you bought an iPhone after 2017, update it now, CISA says
If the iPhone in your pocket is any newer than an iPhone 8 (circa 2017), or you own an iPad Pro or third generation iPad Air, you need to update the software. The Cybersecurity and Infrastructure Security Agency (CISA) added four new bugs in Apple and Microsoft products to its list of known exploited vulnerabilities this week.
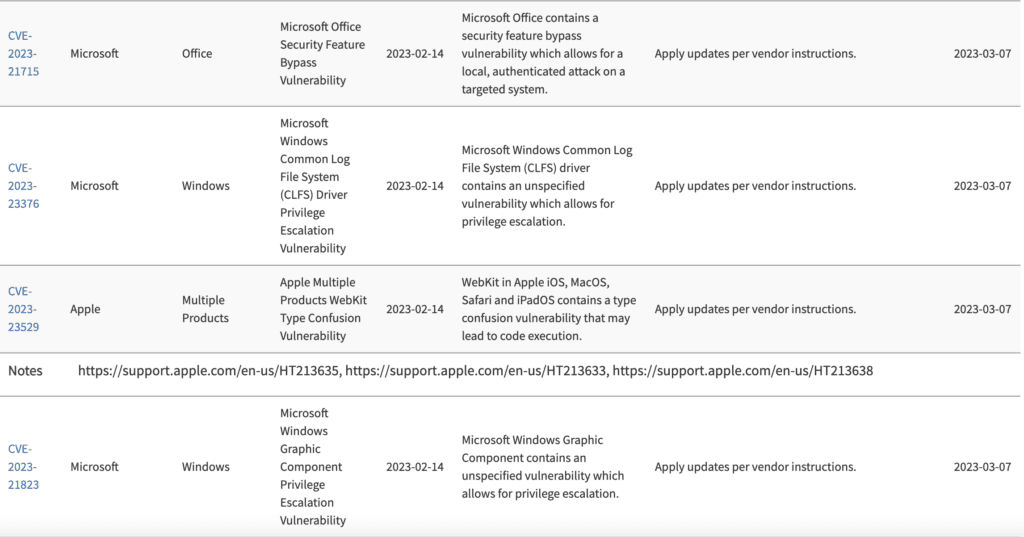
The list is a catalogue of bugs that have become frequent targets of attack for malicious cyber actors. CISA has given nonmilitary federal agencies until March 7 to patch the vulnerabilities — which include zero days for not just for a roster of Apple products but for Microsoft Office software as well.
The Apple zero day – designated CVE 2023-23529 – was patched in the company’s latest operating system update. The company said on Monday that the vulnerability affects all smartphone models after iPhone 8, as well as all iPad Pro models; iPad Air 3rd generation and later; and regular and mini iPads 5th generation and later. Apple said it was aware of reports that the issue “may have been actively exploited.”
A zero day is a previously unknown vulnerability in software. The term “zero-day” refers to the fact that the vendor or developer didn’t know about the flaw before it was exploited – which means they have “zero days” to fix it before a hacker takes advantage.
According to researchers from Nucleus Security, a Florida-based vulnerability management company, an attacker would need to convince a user to load up malware on a vulnerable Apple device, which isn’t as hard as it sounds. The vulnerability “can be easily delivered by mobile phishing attacks via SMS, messenger apps or fake QR codes,” JT Keating, a senior vice president at Zimperium, a mobile device security company, added. He said that after gaining access, an attacker could then take control and execute commands on the infected device.
Microsoft zero days
Microsoft provided patches for the zero-day vulnerabilities as part of its most recent Patch Tuesday, a monthly offering of updates to fix bugs in the company’s software. The most recent release involved the disclosure of 75 fixed bugs. The three cited by CISA are CVE-2023-21715, CVE-2023-21823 and CVE-2023-23376.
The most critical of the bunch, according to Peter Pflaster, a product manager at the IT operations company Automox, is CVE-2023-21715 because hackers have been actively exploiting it to bypass a number of Microsoft Office’s security features. “Attackers could lcoerce an authenticated end user to download and open a specially crafted file that enables a local attack on the device,” he said.
Mike Walters, vice president of vulnerability and threat research at Action1, said the CVE-2023-23376 zero day is dangerous too. It targets the Windows Common Log File System Driver, which basically logs the activity on a system. The vulnerability could allow a user to escalate their privileges on a network and, Walters said, the vulnerability is relatively simple to exploit and requires low levels of access and no user interaction.
Windows operating systems from Windows 7 onwards carry a high vulnerability score of 7.8. He added that Microsoft has confirmed that the vulnerability is currently being exploited in the wild.
Researchers at Nucleus Security also warned that the bug could be used alongside another code execution vulnerability in a ransomware campaign.
The last bug, CVE-2023-21823, affects the Windows Graphics system and according to Walters is also relatively simple to exploit while requiring low levels of access.
In addition to offerings from Microsoft and Apple, February’s Patch Tuesday included security updates for products from Adobe, SAP, VMWare, Android, and OpenSSL.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.