Hawaiʻi Community College hit with ransomware attack
Hawaiʻi Community College is the latest university to deal with a ransomware attack, announcing on Tuesday night that it was forced to shut off its network and to contact federal authorities about the incident.
The two-year community college on the island of Hawai'i is part of state school system and has campuses in Kona and Pālamanui. The school serves more than 2,500 students each year.
A spokesperson told Recorded Future News that college representatives are now working with federal authorities and cybersecurity experts to deal with the situation after being notified of the attack on June 13.
The University of Hawaiʻi was first notified of the issue before informing officials at the Hawaiʻi Community College campus.
“UH System Information Technology Services responded immediately and took the Hawaii CC network offline and took additional steps to protect all UH networks. Hawaiʻi Community College is the only UH campus identified in the attack by the group claiming responsibility,” the spokesperson said.
“At this time, UH cybersecurity experts do not believe that other UH campuses have been impacted.”
The spokesperson declined to comment on how campus systems were affected and whether a ransom will be paid.
Emsisoft ransomware expert Brett Callow said at least 49 post-secondary schools in the U.S. have been hit with ransomware this year, with at least 43 having had data stolen.
“This includes five schools that were impacted by MOVEit, although I’m not sure whether we’ll end up classing those as ransomware,” he said.
The attack on Hawaiʻi Community College follows several others announced in recent weeks, including large incidents affecting colleges in the United Kingdom, Germany and elsewhere in the U.S.
The community college released its statement on the attack following claims from the NoEscape ransomware group, which is also stylized as N0_Esc4pe.
The gang posted the school on its leak site and claimed to have stolen 65 gigabytes of data, threatening to leak what was taken after a week.
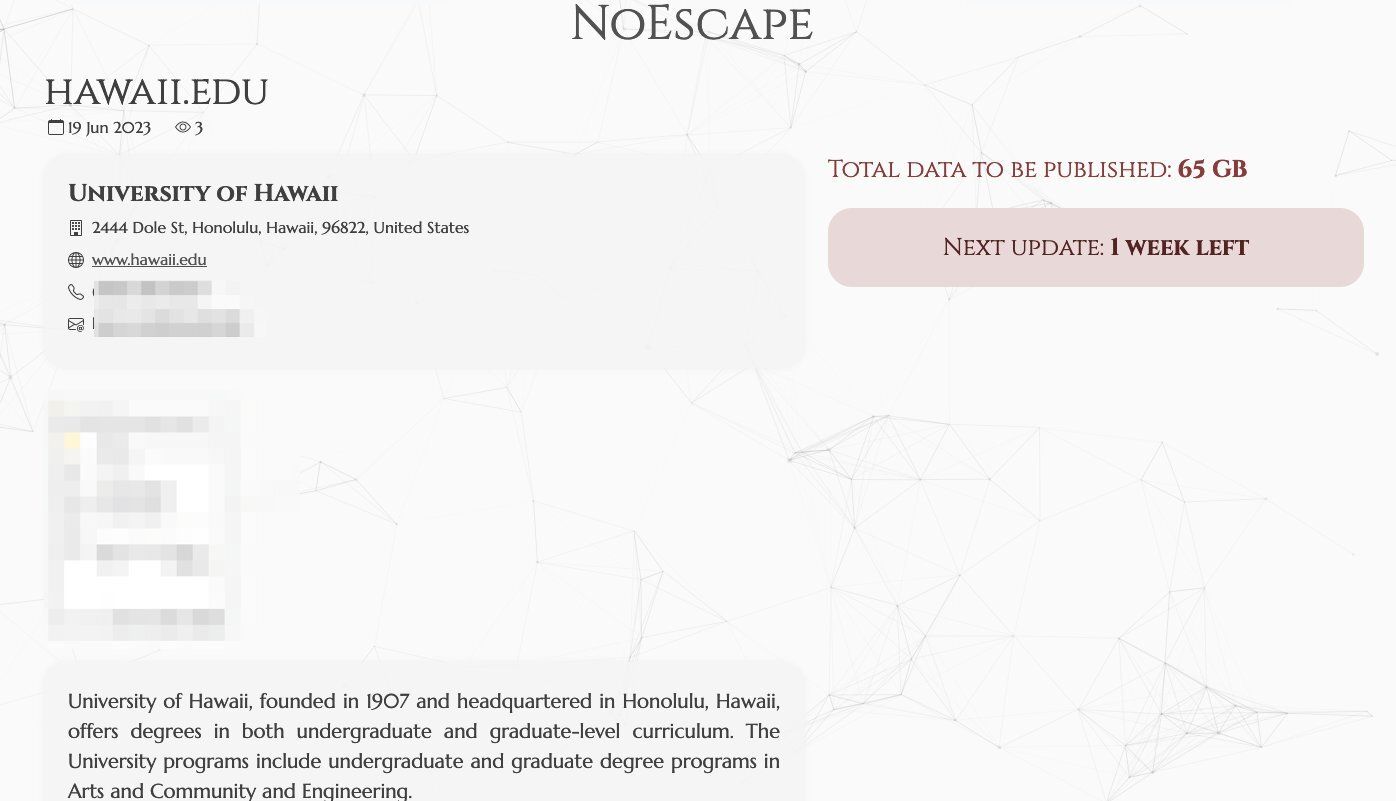 A post on NoEscape's leak site.
A post on NoEscape's leak site.
Recorded Future ransomware expert Allan Liska said NoEscape is a very new ransomware group first seen in May. It was first spotted advertising its services on the cybercriminal forum RAMP.
“NoEscape does appear to be new ransomware, not based on previous/stolen source code and it is written in C++,” he said.
“Despite being relatively new, they have already hit at least half a dozen victims including a hospital in Belgium, a manufacturing company in the US and another manufacturing company in the Netherlands.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



