Hackers compromise Zimbra email accounts in phishing campaign
Hackers are targeting Zimbra Collaboration email servers in an ongoing phishing campaign, researchers have discovered.
According to a report from Slovak software company ESET, the attackers have been gathering credentials of Zimbra account users since at least April. The researchers haven’t attributed the attacks to any known threat actors.
Although this campaign is not “technically sophisticated,” the researchers said,it is still able to spread and successfully compromise organizations that use Zimbra Collaboration — software offering email, calendar and communication tools.
The program is used by businesses, government agencies and academic institutions, including Max Planck Institute and Kyoto University of Education.
“The popularity of Zimbra Collaboration among organizations expected to have lower IT budgets ensures that it stays an attractive target for adversaries,” ESET said.
The hackers appear to be targeting organizations largely at random, with Zimbra use being the only commonality among them. The majority of targets are located in Poland, Ecuador and Italy, according to ESET.
To breach targeted systems, hackers send victims an email containing a phishing page within an attached HTML file. This email warns users about an email server update, account deactivation, or a similar issue, and asks the user to click on the attached file.
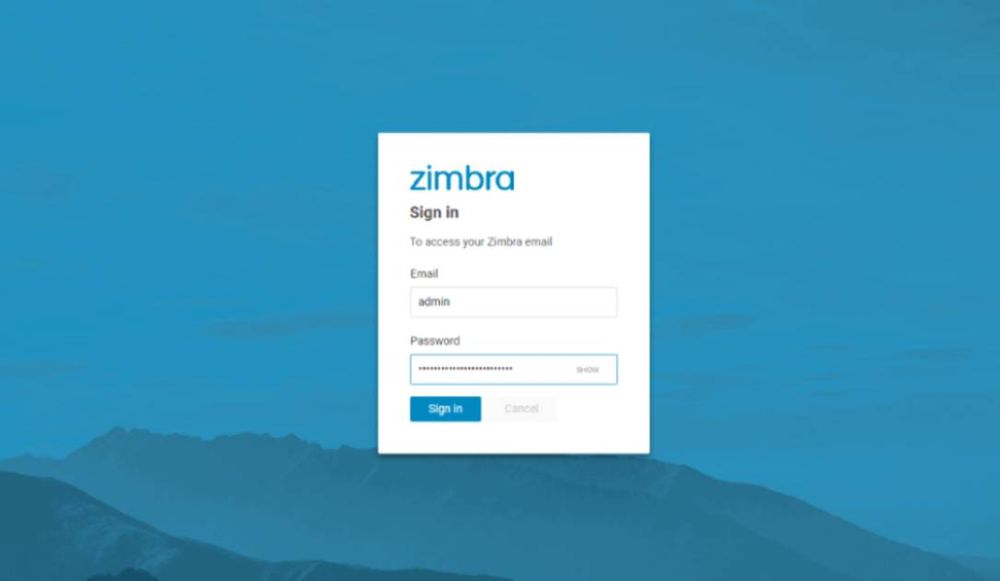
After opening the attachment, the user is redirected to a fake Zimbra login page designed to match the targeted organization. The username field on this page is prefilled, which makes it appear more legitimate.
Some phishing emails were sent from Zimbra accounts of previously targeted, legitimate companies. The attackers probably hacked into the victim's administrator accounts and set up new mailboxes, which they then used to send phishing emails to other targets.
It's unclear how administrator accounts were hacked, but ESET suggested that using the same password for both email and administration could be an explanation.
Daryna Antoniuk
is a reporter for Recorded Future News based in Ukraine. She writes about cybersecurity startups, cyberattacks in Eastern Europe and the state of the cyberwar between Ukraine and Russia. She previously was a tech reporter for Forbes Ukraine. Her work has also been published at Sifted, The Kyiv Independent and The Kyiv Post.