Google: More than 40% of zero-days in 2022 were variants of previous vulnerabilities
The second most zero-day vulnerabilities in the wild were discovered in 2022, according to security researchers from Google.
Zero-day vulnerabilities are bugs that were previously unknown by the vendor or provider, giving threat actors ample time to exploit them until they are patched.
Maddie Stone, a security researcher with Google’s Threat Analysis Group, said in a blog post this week that the most zero-days ever discovered was in 2021, when 69 were detected. That compares to 41 found in 2022.
“Although a 40% drop might seem like a clear-cut win for improving security, the reality is more complicated,” Stone explained.
Stone warned that there were several alarming developments throughout 2022, including a trend where patches for Android vulnerabilities were not available for lengthy periods of time, exposing users to bugs even after they were discovered.
According to Stone, this is partially due to the gap between upstream vendors and downstream manufacturers.
Google's 2022 Year in Review of in-the-wild 0-days is out! 4 key takeaways:
— Maddie Stone (@maddiestone) July 27, 2023
N-days function like 0-days on Android
0-clicks and new browser mitigations drive down browser 0-days
Over 40% of itw 0-days are variants
Bug collisions are high#itw0dayshttps://t.co/fFVUnWlmAF pic.twitter.com/bTkBF417XY
As an example, Stone used CVE-2022-38181 – a vulnerability used in a spyware campaign against people in Italy, Malaysia and Kazakhstan. The bug was reported to Android’s security team in July 2022 by GitHub security researcher Man Yue Mo. Android determined that it was a device-specific issue and referred it to British semiconductor and software design company Arm.
“In October 2022, ARM released the new driver version that fixed the vulnerability. In November 2022, TAG discovered the bug being used in-the-wild,” Stone said.
“While ARM had released the fixed driver version in October 2022, the vulnerability was not fixed by Android until April 2023, 6 months after the initial release by ARM, 9 months after the initial report by Man Yue Mo, and 5 months after it was first found being actively exploited in-the-wild.”
Hackers have also increasingly used 0-click exploits – where victims do not have to click anything to be exploited. Due to improvements made by browser providers, threat actors are moving toward 0-click vulnerabilities that target components instead.
There was a 42% dip in zero-days affecting browsers in 2022, with Chrome, Safari and Firefox releasing pivotal security updates that improved their defenses.
Stone noted that no in-the-wild 0-clicks – like the ones discovered by Citizen Lab in 2021 – were publicly detected and disclosed in 2022, but said security experts know multiple attackers used them. They are nearly impossible to detect because they lack the kind of footprint found in 1-click bugs.
One of the most concerning changes in 2022 was the fact that more than 40% of the zero-days seen were variants of vulnerabilities that had already been reported. More than 20% of the bugs are variants of previous in-the-wild zero-days as well, Stone added.
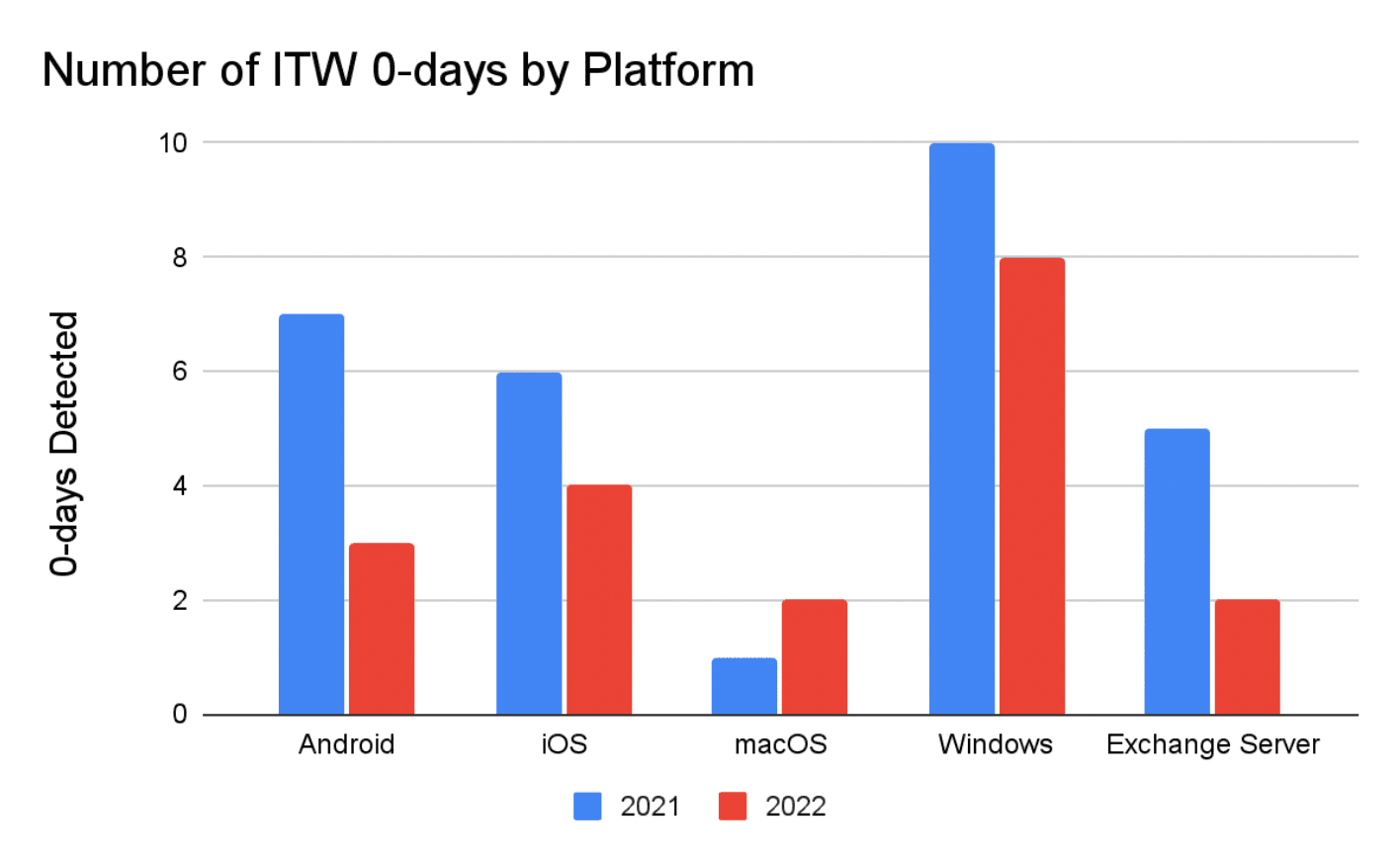 Image: Google
Image: Google
“This continues the unpleasant trend that we’ve discussed previously in both the 2020 Year in Review report and the mid-way through 2022 report. More than 20% are variants of previous in-the-wild 0-days from 2021 and 2020,” Stone said.
“2022 brought more frequent reports of attackers using the same vulnerabilities as each other, as well as security researchers reporting vulnerabilities that were later discovered to be used by attackers. When an in-the-wild 0-day targeting a popular consumer platform is found and fixed, it's increasingly likely to be breaking another attacker's exploit as well.”
The report includes a range of other interesting statistics. The number of zero-days discovered in the first and second half of 2022 were almost identical and the number of organizations discovering the bugs was similar to 2021.
For 2023, Stone said vendors need to get patches and mitigations to users at a faster pace while also releasing more detailed information on the root causes so that variants are not discovered.
More platforms also need to follow the lead of browsers and release “broader mitigations” in an effort to eradicate entire classes of vulnerabilities.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



