Google: Seven zero-days in 2021 developed commercially and sold to governments
Google’s Threat Analysis Group (TAG) released a new report on Thursday chronicling an Italian spyware vendor selling technology used on victims in Italy and Kazakhstan.
The report mirrors another from cybersecurity company Lookout that was published last week covering “Hermit” – a brand of surveillanceware developed by spyware vendor RCS Labs and telecoms company Tykelab Srl.
The Google report examined the spyware from RCS Labs, noting that the Italian vendor “uses a combination of tactics, including atypical drive-by downloads as initial infection vectors, to target mobile users on both iOS and Android.”
Google TAG researchers Benoit Sevens and Clement Lecigne also touch on the wider commercial spyware industry, noting that Google continues to track the activities of vendors and recently testified at the EU Parliamentary hearing on “Big Tech and Spyware” about the work they’re doing “to monitor and disrupt this thriving industry.”
Today I had the opportunity to testify at the European Parliament @EP_PegaInquiry's hearing on "Big tech and Spyware".
— Charley Snyder (@charley_snyder_) June 14, 2022
This issue is something we are focused on addressing @Google and I wanted to take a moment and share some thoughts
“Seven of the nine zero-day vulnerabilities our Threat Analysis Group discovered in 2021 fall into this category: developed by commercial providers and sold to and used by government-backed actors,” Sevens and Lecigne explained.
“TAG is actively tracking more than 30 vendors with varying levels of sophistication and public exposure selling exploits or surveillance capabilities to government-backed actors. Our findings underscore the extent to which commercial surveillance vendors have proliferated capabilities historically only used by governments with the technical expertise to develop and operationalize exploits. This makes the Internet less safe and threatens the trust on which users depend.”
iOS and Android versions
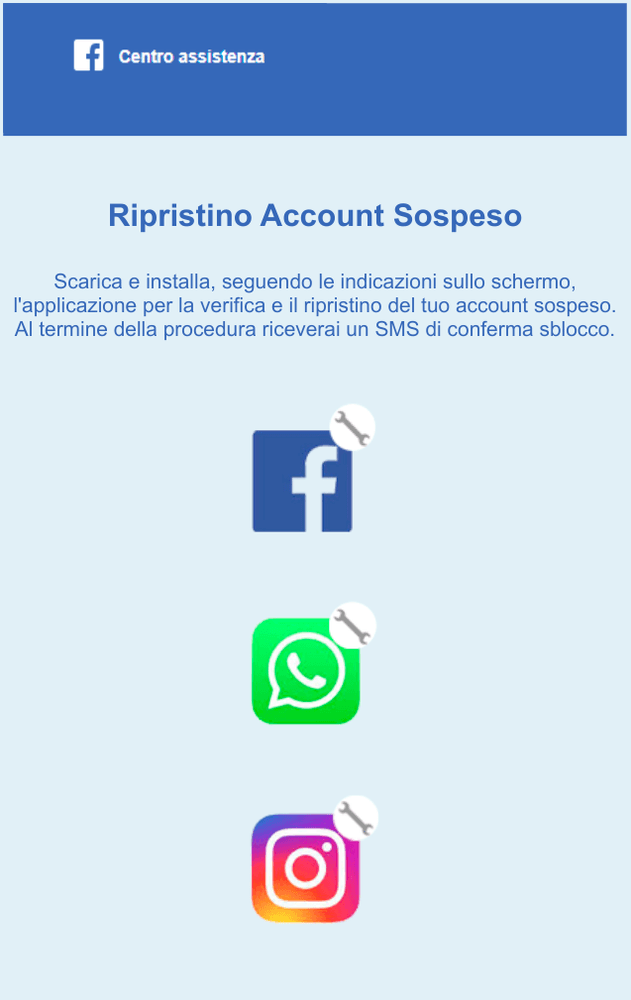
Like the Lookout report, Google found that RCS Labs’ spyware generally originates from a unique link sent to a victim. Once the link is clicked, the victim is asked to download and install a malicious app.
They found evidence that victims had both Android or iOS devices. Surprisingly, Google noted that they believe the actors behind the campaigns at times worked with victims' internet service providers to “disable the target’s mobile data connectivity.”
“Once disabled, the attacker would send a malicious link via SMS asking the target to install an application to recover their data connectivity,” the researchers said.
“We believe this is the reason why most of the applications masqueraded as mobile carrier applications. When ISP involvement is not possible, applications are masqueraded as messaging applications.”
Google said the applications are not available on the App Store but are signed with a certificate from a company named 3-1 Mobile SRL, which “satisfies all of the iOS code signing requirements on any iOS devices because the company was enrolled in the Apple Developer Enterprise Program.”
The app analyzed by Sevens and Lecigne contained exploits for six CVEs – CVE-2018-4344, CVE-2019-8605, CVE-2020-3837, CVE-2020-9907, CVE-2021-30883 and CVE-2021-30983.
“All exploits used before 2021 are based on public exploits written by different jailbreaking communities,” the researchers said.
“At the time of discovery, we believe CVE-2021-30883 and CVE-2021-30983 were two 0-day exploits. In collaboration with TAG, Project Zero has published the technical analysis of CVE-2021-30983.”
For Android devices, the app disguises itself as a legitimate Samsung application via its icon. But Google confirmed it was never available in the Google Play app store.
Google said it implemented changes to Google Play Protect and disabled Firebase projects used as C2 in the campaign as a way to protect its users. It also warned all of the Android device victims of the spyware campaign.
The report notes that the spyware industry is currently “thriving and growing at a significant rate” and is being fueled by numerous governments incapable of developing these kinds of capabilities themselves.
The industry is being exploited by governments “for purposes antithetical to democratic values: targeting dissidents, journalists, human rights workers and opposition party politicians.”
Sevens and Lecigne added that it is also concerning vendors like RCS Labs are “stockpiling zero-day vulnerabilities in secret” and noted that this is even more problematic considering a number of spyware vendors have been compromised over the past ten years, “raising the specter that their stockpiles can be released publicly without warning.”
“Tackling the harmful practices of the commercial surveillance industry will require a robust, comprehensive approach that includes cooperation among threat intelligence teams, network defenders, academic researchers, governments and technology platforms,” the two researchers said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



