Globant confirms reports of breach after Lapsus$ shares 70GB of stolen files
Multibillion-dollar software development company Globant has confirmed reports that their systems were breached and that someone gained access to the company's code repository.
In a statement on Wednesday afternoon, Globant said they recently detected that a “limited section” of their code repository was accessed.
“We have activated our security protocols and are conducting an exhaustive investigation. According to our current analysis, the information that was accessed was limited to certain source code and project-related documentation for a very limited number of clients,” the Luxembourg-based company said.
“To date, we have not found any evidence that other areas of our infrastructure systems or those of our clients were affected. We are taking strict measures to prevent further incidents.”
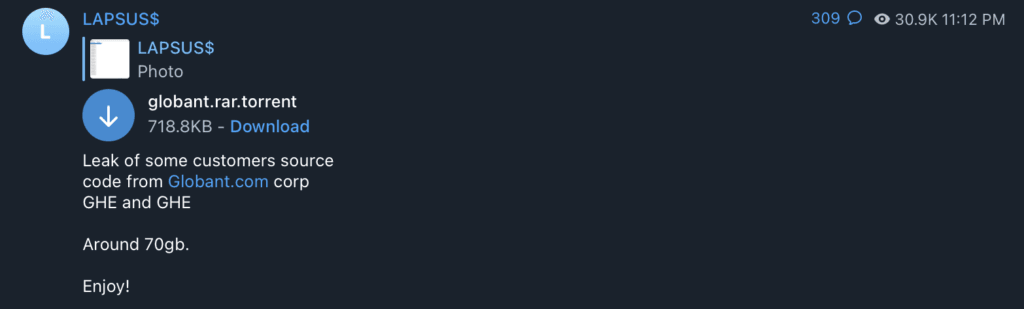
On Tuesday evening, members of extortion group Lapsus$ took to Telegram to share a 70GB file of “customer source code” from Globant.
“For anyone who is interested about the poor security practices in use at Globant.com. i will expose the admin credentials for ALL there devops platforms below,” the group said.
They shared Globant system administrator credentials for Github, Confluence, Crucible and Jira as well as other documents connected to the company and its customers
Cybersecurity expert Soufiane Tahiri wrote on Twitter that data from the Globant leak indicated that the leak may have started in Colombia and may have come from an employee account at Globant’s offices in Bogota.
Most of what I'm seeing for now, from this #Globant leak, points toward Colombia. If this leak comes from a compromised employee account (as #Lapsus tended to use) I bet on Globant offices in Bogota. pic.twitter.com/5GA7r2dzDW
— Soufiane Tahiri (@S0ufi4n3) March 30, 2022
The company, which has dozens of high-profile customers, was founded in Buenos Aires before moving to its headquarters in Luxembourg. It brought in a 2021 revenue of nearly $1.3 billion, a more than 63% year-over-year increase. It has more than 25,000 employees.
Lapsus$ has faced increased scrutiny from cybersecurity experts and law enforcement since it drew headlines for attacks on Microsoft, NVIDIA, Samsung, Okta and other corporate giants.
The City of London Police told Hacker News last week that seven people connected to Lapsus$ were arrested and then released as the investigation into the attacks continues. The arrests followed a story from Bloomberg that identified a UK teenager as a member of the group.
The FBI added the group to its “Most Wanted” list, asking the public for information about people connected to the group.
After the Okta attack, the group “took a vacation” but returned this week with a list of alleged victims that included dozens of high-profile companies including Facebook, DHL, Citibank, C-Span, Fortune and others.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



