Free decrypter available for Lorenz ransomware
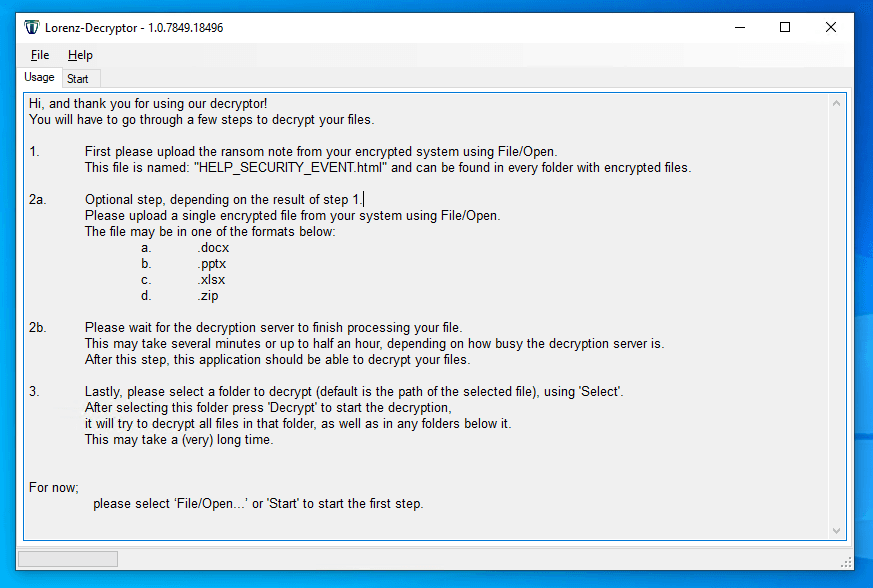
Dutch cybersecurity firm Tesorion has released today a free application that can help victims of the new Lorenz ransomware to recover encrypted files without paying the ransom.
The decrypter was announced in a blog post last week and officially released and added to the NoMoreRansom project earlier today.
According to a technical report authored by Tesorion security researcher Gijs Rijnders, the Lorenz ransomware encryption process contains a bug where files that have a size that is a multiple of 48 bytes are permanently destroyed during encryption as the last 48 bytes are not written to the encrypted file and are permanently lost.
"Even if you managed to obtain a decryptor from the malware authors, these bytes cannot be recovered," Rijnders explained.
"Based on our analysis of the Lorenz ransomware we have come to the conclusion that we can decrypt (non-corrupted) affected files in some cases without paying the ransom," the Tesorion researcher said.
"Supported file types include Microsoft Office documents, PDF files and some image and movie types," he added.
Rijnders said the decrypter is not universal and will work only "in some cases." However, this is more of a chance than many Lorenz victims have at recovering their files without paying hundreds of thousands of US dollars to the Lorenz gang.
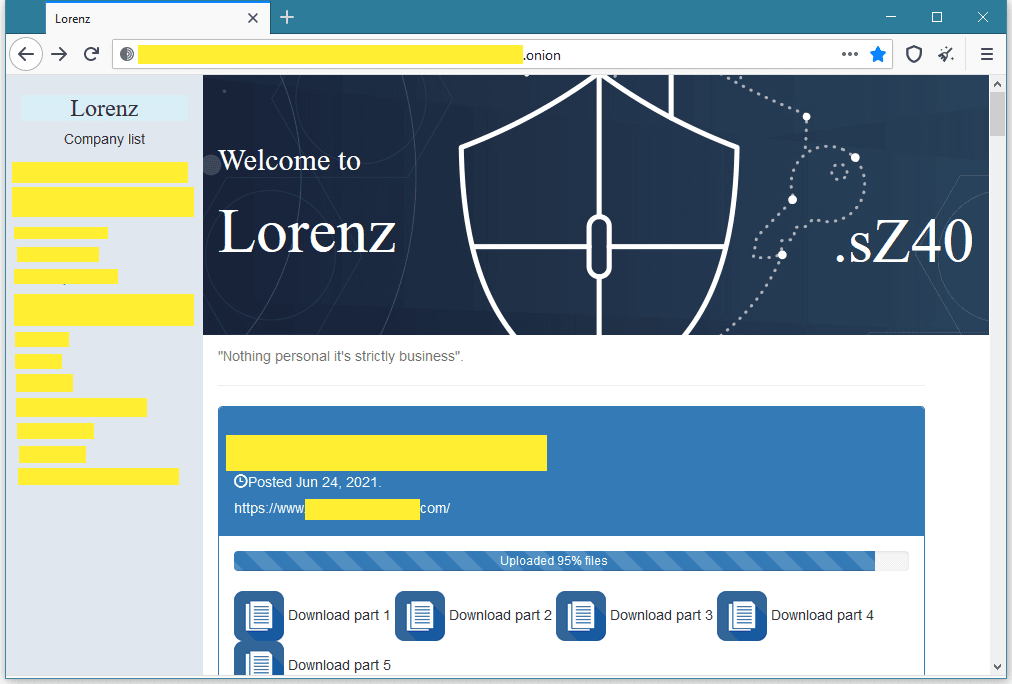
The Lorenz ransomware was first seen in attacks that took place this spring, and according to security researchers, the ransomware's code appears to have evolved from the old ThunderCrypt and SZ40 families.
In its most recent incarnation, Lorenz has been used exclusively in attacks carried out against enterprise targets.
Just like similar "big-game hunting" ransomware operations, the Lorenz gang also runs a leak site on the dark web where it publishes data from victims who refuse to pay. Thirteen victims have been listed on this site so far.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



