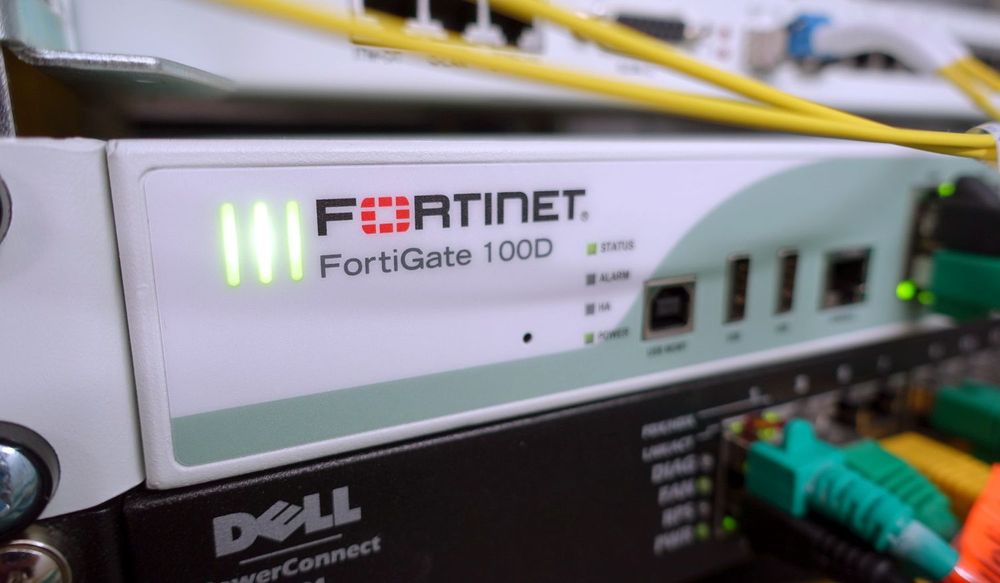
Nearly 70% of FortiGate Firewalls are vulnerable to new bug, experts say
Cybersecurity experts are raising the alarm about a new vulnerability that leaves hundreds of thousands of Fortinet customers vulnerable to attack.
Concerns about the issue — tracked as CVE-2023-27997 — grew last month due to how widely used Fortinet’s SSL-VPN product is among government organizations. Fortinet released a patch in June for the bug, which has a “critical” severity score of 9.8 out of 10 and was discovered by Lexfo Security vulnerability researchers.
Fortinet said the issue “may have been exploited in a limited number of cases” and noted that the hacking campaign was “targeted at government, manufacturing, and critical infrastructure.”
But this weekend, concerns were reignited when researchers from security firm Bishop Fox announced that they internally developed an exploit for CVE-2023-27997.
“There are 490,000 affected SSL VPN interfaces exposed on the internet, and roughly 69% of them are currently unpatched. You should patch yours now,” they said in a blog post explaining their findings.
“The exploit runs in approximately one second, which is significantly faster than the demo video on a 64-bit device shown by Lexfo.”
Using the researcher’s calculations, that leaves more than 335,000 instances currently vulnerable to the issue. The experts from Bishop Fox also expressed alarm at the dozens of unpatched instances that are running years-old versions, dozens of which reached end-of-life years ago.
Several cybersecurity experts echoed Bishop Fox’s alarm about the issue, explaining that the need to patch was an urgent problem.
Tanium chief security advisor Timothy Morris said the seriousness of the issue “cannot be understated” considering that exploit code now exists and the devices at the heart of the problem are typically on the perimeter of an organization.
He noted that many organizations have redundant systems that are running as spares, meaning several most likely need to be patched within any one company.
“This is one of those examples where the CVS rating feels like the Richter scale. Remote code execution on a security appliance is about as bad as it can get,” said Andrew Barratt, vice president at cybersecurity firm Coalfire.
“These devices are both the doors to the network, and a large volume of the devices still being vulnerable is probably due to an inability to take these firewalls offline and test the patch with the associated impact on the business.”
Other cybersecurity experts, including Ontinue director of threat intelligence Andre van der Walt, added that in recent years, several high-profile FortiGate vulnerabilities have been discovered and exploited.
There was some concern that Chinese hackers, as part of the Volt Typhoon hacking group, exploited the bug during an attack on the telecommunications network of Guam, a U.S. territory in the Pacific Ocean.
Fortinet dispelled the rumors that CVE-2023-27997 was involved in that compromise but said it “expects all threat actors, including those behind the Volt Typhoon campaign, to continue to exploit unpatched vulnerabilities in widely used software and devices.”
CVE-2023-27997, van der Walt said, could lead to data breaches, ransomware attacks, and other serious consequences.
He noted that the findings from Bishop Fox mirrors the overall trend of patching lagging significantly behind addressing new exposure in the attack surface, regardless of the technology in question.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.