FDA, CISA warn of vulnerabilities in medical devices used for genetic testing
The U.S. Food and Drug Administration (FDA) and Cybersecurity and Infrastructure Security Agency (CISA) warned on Thursday that vulnerabilities have been found in software from Illumina, a company that produces tools used for genetic analysis.
CISA said if exploited, the bugs would allow an attacker “to take control of the affected product remotely and take any action at the operating system level.”
“An attacker could impact settings, configurations, software, or data on the affected product and interact through the affected product with the connected network,” CISA explained in its own advisory.
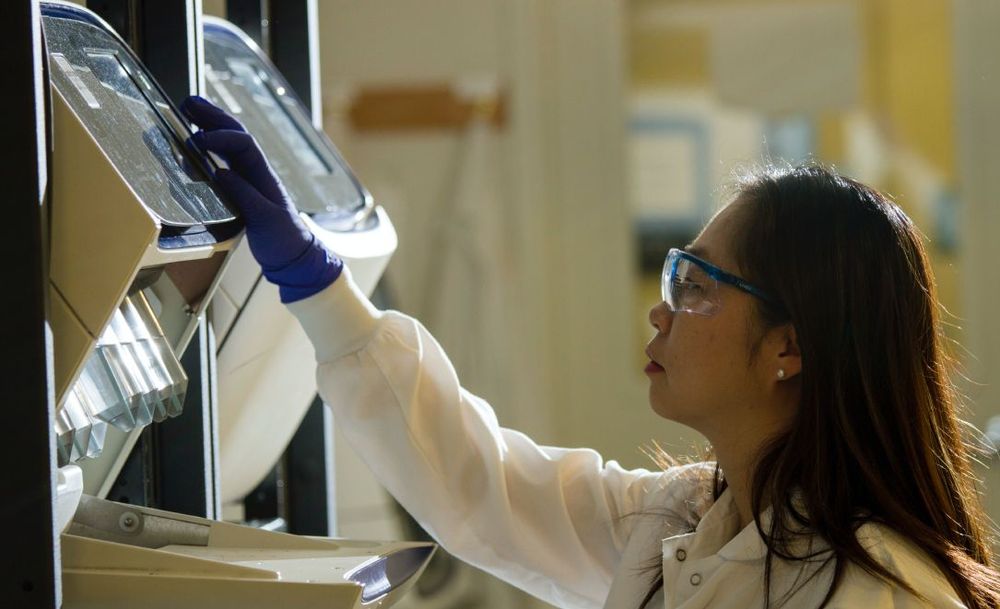
The vulnerabilities affect software in medical devices used for clinical diagnostic use in sequencing a person’s DNA, testing for various genetic conditions, or for research purposes.
According to the FDA, the vulnerability affects the Local Run Manager (LRM) software and could impact patient test results in the instruments intended for clinical diagnosis, “including causing the instruments to provide no results or incorrect results, altered results, or a potential data breach.”
An Illumina spokesperson told The Record that it has released a patch and is in the process of developing a permanent remediation. They urged customers to contact the company's customer support channel for help installing the patch.
The company released an “Urgent Safety Notification” on May 3 to customers that may be affected.
The FDA urged users to either install the patches or contact the company for assistance if an instrument is not connected to the internet. Those who suspect they may have already been compromised were told to contact both the company and the FDA. The FDA noted that it nor Illumina has received reports that the vulnerabilities have been exploited.
The most concerning vulnerability – CVE-2022-1517 – has a CVSS score of 10 and allows an attacker to upload and execute code remotely at the operating system level. There are also several other vulnerabilities cited in the CISA notice, including CVE-2022-1518, which also has a CVSS score of 10 and allows attackers to upload outside the intended directory structure.
CVE-2022-1519 provides similar permissions to attackers and also carries a CVSS score of 10. CVE-2022-1521 – carrying a CVSS of 9.1 – allows malicious actors to inject, replay, modify, and intercept sensitive data. And CVE-2022-1524 similarly allows attackers to gain access to sensitive data in-transit, including credentials but has a CVSS of 7.4.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.