FCC proposes cybersecurity changes to emergency alert system
Federal Communications Commission (FCC) chairwoman Jessica Rosenworcel has proposed several changes to the U.S. Emergency Alert System (EAS) and Wireless Emergency Alerts designed to beef up the cybersecurity of the systems following the discovery of vulnerabilities last month.
The systems allow the federal government, the president or state-level officials to send out emergency warnings about a range of issues including potential weather events or AMBER alerts for missing children.
But last month, the Federal Emergency Management Agency (FEMA) issued a warning to participants in the EAS that vulnerabilities can be used to allow threat actors to issue alerts over TV, radio, and cable networks.
The person who discovered the bugs — CYBIR.com security researcher Ken Pyle — told The Record that one of the main issues is that FEMA doesn’t actually manage the systems because they are administered and run by local stations, authorities and affiliates.
A spokesperson for the FCC told The Record that as of December, there were approximately 25,644 EAS participants in the U.S. and its territories.
“One of the problems is these are everywhere, anyone can launch an alert with the right access… even by accident,” he explained. “No one can or will tell you what the patch status is… but they will definitely say it’s not zero. That uncertainty should terrify you.”
Rosenworcel’s proposal this week would require EAS participants to report compromises of their EAS equipment and require that both EAS participants as well as participants in the Wireless Emergency Alerts program to “annually certify to having a cybersecurity risk management plan in place.”
The new rules would also demand that participants “employ sufficient security measures to ensure the confidentiality, integrity, and availability of their respective alerting systems.”
Wireless providers would be required to take steps to ensure that only valid alerts are displayed on consumer devices and more generally, Rosenworcel’s proposal asks that discussions be held about ways the FCC and FEMA can improve the operational readiness of the EAS, including the amount of time that broadcasters, cable providers, and other EAS participants may operate before repairing defective EAS equipment.
“The Emergency Alert System and Wireless Emergency Alerts are used every day across the country to warn the public about severe weather, missing children, and other crises — and to help save lives,” Rosenworcel said in a statement. “It is critical that these public safety systems are secure against cyber threats, which means that we must be proactive. The draft proposals shared today will help ensure that our national alerting systems work as intended during emergencies and the public can trust the warnings they receive.”
The proposal will be voted on by the full commission and if approved, the FCC would seek public comment on the proposed measures as well as “related questions about improving alerting security.”
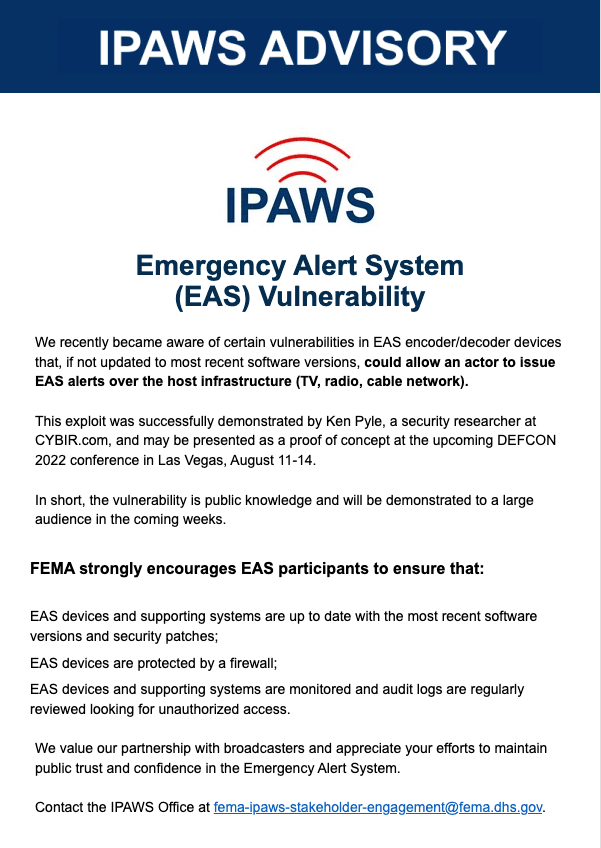
FEMA’s alert last month did not specify the issues in the warning system but said they are found in EAS encoder/decoder devices that have not been updated to the most recent software versions.
The agency warned that the vulnerability is public knowledge and was demonstrated by Pyle at the DEF CON 2022 conference in Las Vegas.
FEMA strongly encouraged EAS participants to make sure that their devices and supporting systems are up to date with all security patches and protected by a firewall. They also asked that all EAS devices and supporting systems are monitored and audit logs are “regularly reviewed looking for unauthorized access.”
FEMA Press Secretary Jeremy Edwards said the agency is working with the FCC to assist “broadcast partners to help correct this issue.”
The FCC sent out its own warning, demanding EAS participants ensure their equipment’s monitoring and transmitting functions are available whenever the stations and systems are operating.
“[The FCC] has previously warned EAS Participants about this vulnerability and encouraged them to secure their EAS equipment by installing current security patches and using firewalls,” the FCC notice said. “The Bureau again urges all EAS Participants, regardless of the make and model of their EAS equipment, to upgrade their equipment software and firmware to the most recent versions recommended by the manufacturer and secure their equipment behind a properly configured firewall as soon as possible.”
The agency added that any organization that fails to receive or transmit EAS messages during national tests or actual emergencies because of an equipment failure “may subject the EAS Participant to enforcement.”
A breached alert system would cause widespread panic, as seen after several mistaken warnings sent out by state level agencies in Hawaii, New York, Nebraska and more over the years.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



