FBI says the Cuba ransomware gang made $43.9 million from ransom payments
The US Federal Bureau of Investigations said today that the operators of the Cuba ransomware have earned at least $43.9 million from ransom payments following attacks carried out this year.
In a flash alert sent out on Friday, the Bureau said the Cuba gang has "compromised at least 49 entities in five critical infrastructure sectors, including but not limited to the financial, government, healthcare, manufacturing, and information technology sectors."
The FBI said it traced attacks with the Cuba ransomware to systems infected with Hancitor, a malware operation that uses phishing emails, Microsoft Exchange vulnerabilities, compromised credentials, or RDP brute-forcing tools to gain access to vulnerable Windows systems.
Once systems are added to their botnet, Hancitor operators rent access to these systems to other criminal gangs in a classic Malware-as-a-Service model.
While an April 2021 McAfee report [PDF] on the Cuba ransomware found no connection between the two groups, the FBI report highlights what appears to be a new partnership between MaaS providers and ransomware gangs after other ransomware operations struck similar partnerships throughout 2020.
The FBI document [PDF] released earlier today highlights how a typical Hancitor-to-Cuba infection takes place and provides indicators of compromise that companies could use to shore up their defenses.
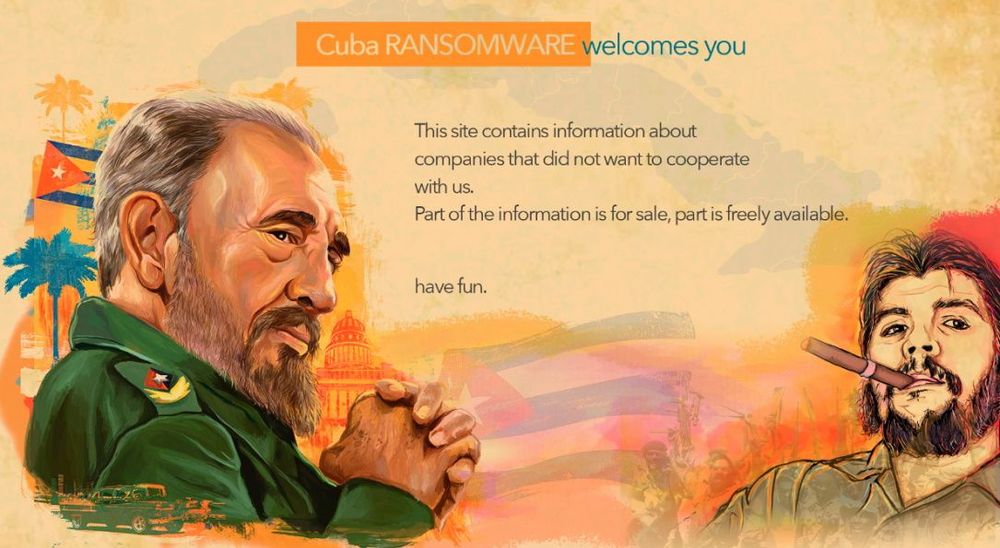
It is also worth mentioning that Cuba is also one of the ransomware groups that gather and steal sensitive files from compromised companies before encrypting their files. If companies don't pay, the Cuba group will threaten to dump sensitive files on a website they have been operating on the dark web since January this year.
According to data compiled by Recorded Future analysts, at least 28 companies have been listed on this site after refusing to pay so far this year.
The FBI said that the $43.9 million figure represents actual victim payment and that the group demanded more than $74 million from victims, some of which refused to pay. The figure falls in the usual range of most ransomware revenues reported so far:
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.