CISA urges F5 users to address 'critical' vulnerability in BIG-IP software
The Cybersecurity and Infrastructure Security Agency is urging F5 customers to address a vulnerability in BIG-IP products that could allow an attacker "to take control of an affected system."
The company also released an advisory about the bug, CVE-2022-1388, which could allow an attacker with access through the BIG-IP system's management port to execute arbitrary system commands, create or delete files, or disable services.
BIG-IP products — which include software and hardware — are used widely by companies to help keep their applications up and running. The CISA alert revolves around the iControl REST component, which helps manage interaction "between user or script and F5 device," according to the company.
The vulnerability — which F5 said it discovered internally — has a CVSS score of 9.8 out of 10, ranking it as "critical."
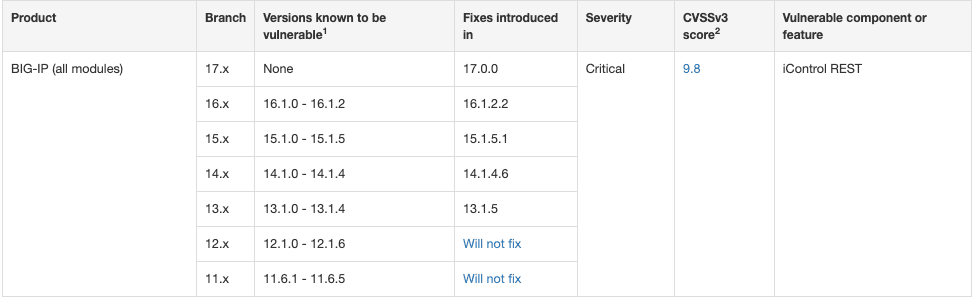
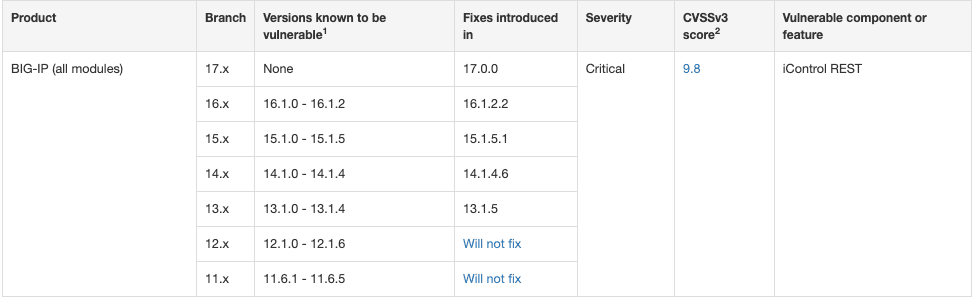
F5 said BIG-IP versions 16.1.0 to 16.1.2, 15.1.0 to 15.1.5, 14.1.0 to 14.1.4, 13.1.0 to 13.1.4, 12.1.0 to 12.1.6 and 11.6.1 to 11.6.5 are affected.
F5 published fixes for each version except for 12.1.0 to 12.1.6 and 11.6.1 to 11.6.5. It urged those using these versions to upgrade to a version with the fix.
The company released several mitigations that involve restricting access to iControl REST to only trusted networks or devices, thereby limiting the attack surface.
Vulcan Cyber’s Mike Parkin told The Record that industry best practices restrict access to management interfaces in general, which would make it difficult for an external attacker to reach the management interface and exploit this vulnerability.
A search on Shodan shows there are at least 15,890 BIG-IP products exposed to the internet, leaving them potentially vulnerable to CVE-2022-1388. There 3,770 vulnerable instances in the US, followed by 1,396 in China and 897 in India, according to Shodan.
Nicole Hoffman, senior cyberthreat intelligence analyst at Digital Shadows, said the critical vulnerability is particularly concerning because it can lead to complete system takeover.
“It likely won't be long before ransomware groups and initial access brokers will start mass scanning for vulnerable devices,” Hoffman noted.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



