Experts warn of concerns around Microsoft RPC bug
Cybersecurity experts and researchers have raised alarms around a vulnerability disclosed by Microsoft Tuesday concerning Windows hosts running the Remote Procedure Call Runtime (RPC).
CVE-2022-26809 has a CVSS score of 9.8 and has already been patched by Microsoft.
Windows hosts running the Server Message Block protocol (SMB protocol) are vulnerable to this bug. SMB protocols allow users to share access to files and tools on remote servers.
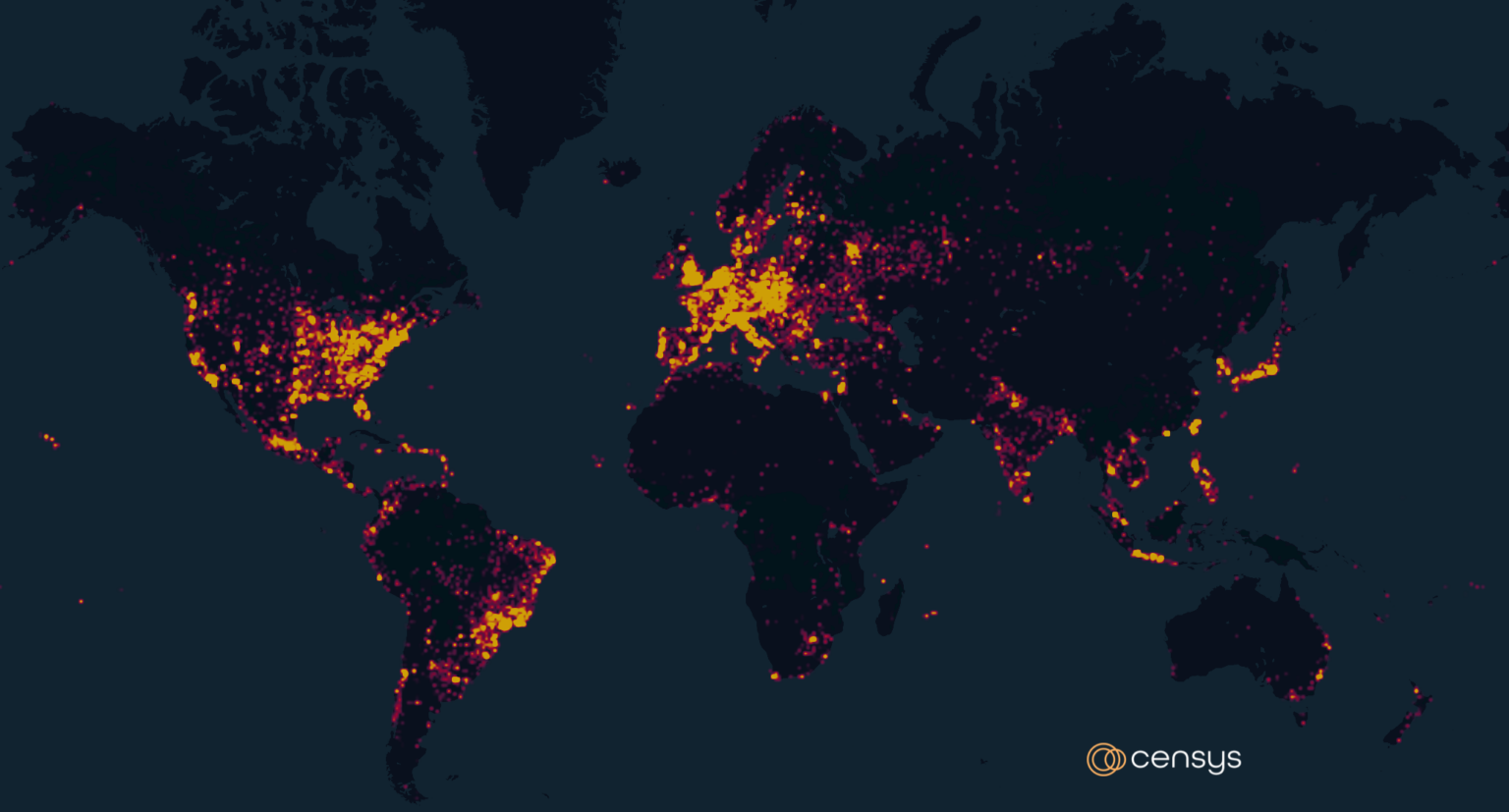
Research company Censys said 1,304,288 hosts are running the SMB protocol as of Wednesday. Of those, 824,011 (63%) were identified by Censys as running a Windows-based operating system. The company noted that they could not determine the running OS for approximately 369,485 (28%) hosts running SMB.
Censys explained that most of the systems running SMB are in the United States. The more than 366,000 systems running SMB in the US dwarfed the 144,622 in Russia, 72,885 in Hong Kong, 70,980 in Germany and 56,659 in France.
Extrahop’s Jamie Moles explained that the vulnerability is tied to the RPC runtime library, which allows applications to access the Remote Procedure Call functionality within Windows. While the bug details aren’t yet fully known, it appears that sending a specially crafted packet will be enough to trigger the exploit, Moles said.
“Due to the trivial nature of the vulnerability it is highly likely that the PoC code will appear very shortly. This CVE therefore has the potential to be crippling in a similar way that Wannacry utilized EternalBlue to spread internally, meaning ransomware attacks may blow up in the coming weeks,” Moles said.
“While Microsoft has issued guidance, blocking the suggested ports on the firewall/perimeter is not feasible on the inside of the perimeter, which is where this exploit could be used to much effect. Additionally, if you use File and Folder sharing internally then those ports will be open.”
Vulcan Cyber’s Mike Parkin said any vulnerability that can run code remotely with zero user interaction is a challenge but added that it is easy to mitigate remote RPC attacks by blocking external connections with a firewall rule.
Tod Beardsley, director of research at Rapid7, told The Record that there are still hundreds of thousands of Windows SMB servers that are both exposed to the internet and are subject to slow-to-no patch schedules.
“Obviously, people should be taking this seriously, but I’m unconvinced that the organizations that have exposed unpatched Windows servers to the internet have been waiting for this moment to spring into action and patch those machines or properly segment their networks,” Beardsley said. “So, I expect that we’ll see a lot of small, local disasters associated with this bug, but I’m optimistic that the internet overall will weather this.”
Vectra vice president Aaron Turner suggested CISO’s automatically disable legacy file sharing protocols as a way to manage these kinds of vulnerabilities.
Silverfort CTO Yaron Kassner noted that RPC is widely used and even if port 445 is closed for access from the Internet at the firewall level (which is not always the case), it is very often open inside the network, which means any attacker that gains access to one machine in the network would be able to exploit this vulnerability to spread very quickly to any Windows machine in the network.
“The vulnerability is very widespread because almost anyone running Windows that didn’t block RPC and didn’t patch yet is susceptible. So patch quickly and close port 445 wherever possible,” Kassner said.
While most experts confirmed that the vulnerability has not been exploited yet, many expect that it likely will be.
RPC vulnerabilities have been found and exploited since Windows became Windows – and even before that on Unix systems, according to KnowBe4’s Roger Grimes.
“Although it can be exploited remotely, over the network, without any end-user interaction against a listening critical service with full access to the underlying operating system (which makes it quite potentially dangerous), the ports it uses are not normally contactable over the Internet because of built-in Windows defenses and firewalls,” Grimes said.
“Most firewalls prevent anyone from accessing this service from over the internet. But the real potential for damage is for any attacker or malware program that makes it onto the local network. Then it is all bets off. The worst case scenario would be if a hacker turns into an automated, roving computer worm.”
Andrea Peterson
(they/them) is a longtime cybersecurity journalist who cut their teeth covering technology policy at ThinkProgress (RIP) and The Washington Post before doing deep-dive public records investigations at the Project on Government Oversight and American Oversight.