EU urged to drop new law that could allow member states to intercept and decrypt global web traffic
More than 300 of the world’s most respected cybersecurity experts have written to European Union lawmakers to warn that a proposed legal reform that may soon become law could fundamentally undermine security online.
A similar joint letter has been sent by industry organizations — including the Linux Foundation, Cloudflare, and Mozilla — telling the EU lawmakers that the proposed regulations are a “dangerous intervention” that risk breaking the fragile system of trust that underpins the use of cryptographic certificates on the web.
The letters were prompted by a proposed update to the bloc’s eIDAS (Electronic Identification, Authentication and Trust Services) regulations which would give EU member states the ability to issue so-called Qualified Website Authentication Certificates (QWACs).
These are effectively cryptographic certificates that web browsers would have a legal obligation to accept as valid — potentially paving the way for governments to arbitrarily issue certificates allowing them to intercept encrypted web traffic globally.
Although the near-final text cited by the letters’ signatories is not public, a draft seen by Recorded Future News corroborated the description of Article 45 of the new law, which states: “Qualified certificates for website authentication issued in accordance with paragraph 1 shall be recognised by web-browsers.”
Wait, explain it to me gently
Sure thing. Visitors to therecord.media, for example, see a padlock icon beside the URL in their web browser. This indicates that the browser is connecting to the server using https — a secure extension of the hypertext transfer protocol (http) that is basically the foundation of the web.
The https protocol secures communications between the web browser and the server by authenticating the identity of the server (i.e. it is really therecord.media, and not someone pretending to be us) and by encrypting the page content so that it cannot be read by anyone intercepting network traffic.
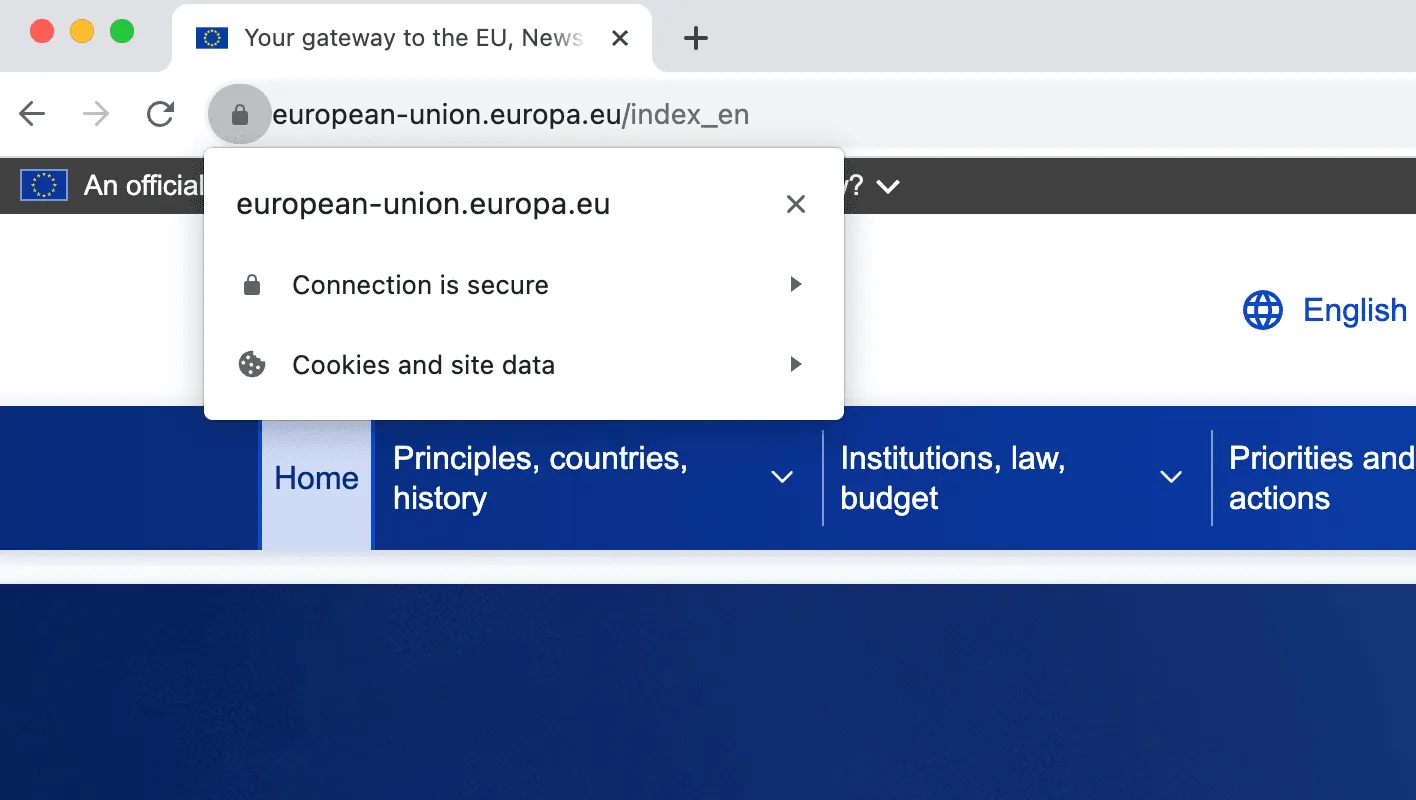
If users click on that padlock icon, their browser allows them to inspect the certificate. This will show the chain of trust that the certificate has been verified by — in this case with an intermediate certificate from our hosting provider Cloudflare up to the root certificate authority DigiCert, which itself has been vetted by the browser developers so they know they can trust it.
In truth, people rarely inspect the certificates, but most browsers are designed to show dramatic warnings (“This connection is untrusted!”) when they detect that something is wrong. This system is imperfect, but it has been refined over the past decade and is continuing to be improved largely as a result of industry efforts. The problem is, the European Union is now attempting to force in another change through an update to its eIDAS law — and industry says that the “improvement” will not only not work, but actually cause things to be less secure.
What’s the improvement?
The update is effectively a replacement of a failed attempt by industry to improve certificate transparency through what is known as an Extended Validation (EV) certificate. These certificates would not only authenticate the domain, but also show who the legal owner and operator of the website was. For a number of reasons — particularly the expense of validating legal ownership — these EV certificates haven’t been widely adopted.
The proposed QWACs are intended to allow governments’ to replace the lack of EV certificates for particular sites, something that has obvious benefits considering the importance of authenticating when web users are genuinely interacting with a government service rather than a phishing page.
Steven Murdoch, one of the letter’s signatories and a professor of security engineering at University College London, explained: “There are some cases where you might want to use your government-issued identity for doing stuff, so signing legally binding contracts under your name, and the eIDAS is really all about that, and that’s fine, governments are the people who would issue the certificates for government-issued identities.
“But where this proposal is problematic is that it has been extended to web browsers, and it’s not just the digital signatures that are used for signing contracts and things related to government identities,” explained Murdoch.
“Root certificates, controlled by so-called certificate authorities, provide the authentication mechanisms for websites by assuring the user that the cryptographic keys used to authenticate the website content belong to that website. The owner of a root certificate can intercept users’ web traffic by replacing the website’s cryptographic keys with substitutes he controls,” explained the security researchers.
Such cases of abuse have been documented, most infamously in the DigiNotar case when the Dutch certificate authority was hacked allowing the attackers to intercept communications between Google and Iranian Google users. Similar cases have affected companies including Comodo and GlobalSign, as the cybersecurity researchers write.
The European Union has legislation to tackle these potential incidents (the NIS2 directive) which is “complemented by public processes and continuous vigilance by the security community to reveal suspicious activities,” as the letter states. However no such recourse would be possible under the abuse scenario described in the letter.
“We ask that you urgently reconsider this text and make clear that Article 45 will not interfere with trust decisions around the cryptographic keys and certificates used to secure web traffic,” states the letter signed by more than 300 security experts.
The letter from industry states: “[We] believe that eIDAS Article 45 and 45a represent a dangerous intervention in a system that is essential to securing the Internet. We request that the EU Parliament and Members reconsider this action.”
Article 45a, which was highlighted in both letters, states that “Qualified certificates for website authentication shall not be subject to any mandatory requirements other than the requirements laid down in paragraph 1,” according to a near-final draft seen by Recorded Future News.
This, according to both joint letters, is unintentionally establishing a maximum level of security that the certificate system can provide by legally prohibiting new developments. Professor Murdoch explained: “So if someone came up with a great idea of how to improve web security, would that be permitted to be included in the browser, or would this clause be an obstacle to including the improvement?
“If that obstacle was insurmountable, then you’ve got something that is going to harm everyone using a web browser, because the developers are probably not going to develop an EU-specific web browser, it’s going to be the same everywhere, so the impact is not just going to be restricted to the EU.”
As the letter states: “This runs counter to well established global norms where new cybersecurity technologies are developed and deployed in response to fast moving developments in technology. This effectively limits the security measures that can be taken to protect the European web. We ask that you reverse this clause, not limiting but encouraging the development of new security measures in response to fast-evolving threats.”
The letters aim to convince European lawmakers to amend the final text of the document, which is still being negotiated and is expected to be confirmed early next year.
Alexander Martin
is the UK Editor for Recorded Future News. He was previously a technology reporter for Sky News and is also a fellow at the European Cyber Conflict Research Initiative.



