EpsilonRed ransomware group hits one of India's financial software powerhouses
Nucleus Software Exports, an Indian company that provides lending software to banks and retail stores, has suffered a major ransomware attack that crippled some of its internal networks and encrypted sensitive business information.
The incident took place last Sunday, on May 30, according to a document the company filed on Tuesday with the Indian National Stock Exchange authority.
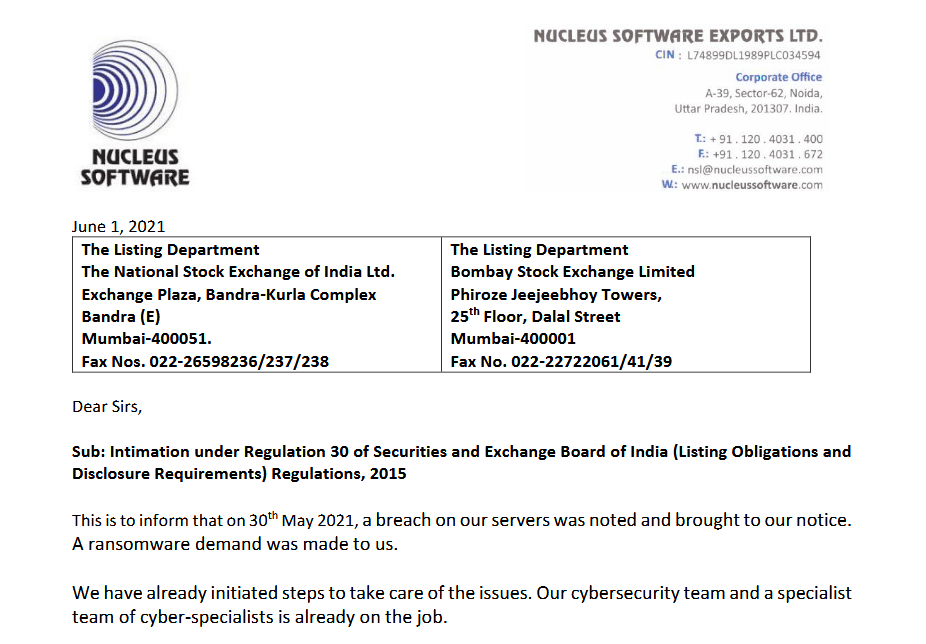
In a quarterly report filed on Thursday, NSE said it's in the process of containing the damage and recovering and restoring impacted systems.
"So far as sensitive data is concerned, we'd like to assure our customers that there is NO financial data of any customer available/stored with us and therefore the question of any leakage or loss of client data does not arise," the company told Indian financial regulators.
But while an NSE spokesperson has declined to comment on the attack on several occasions, members of the cyber-security community have been able to track down the ransomware strain that was deployed on the company's network.
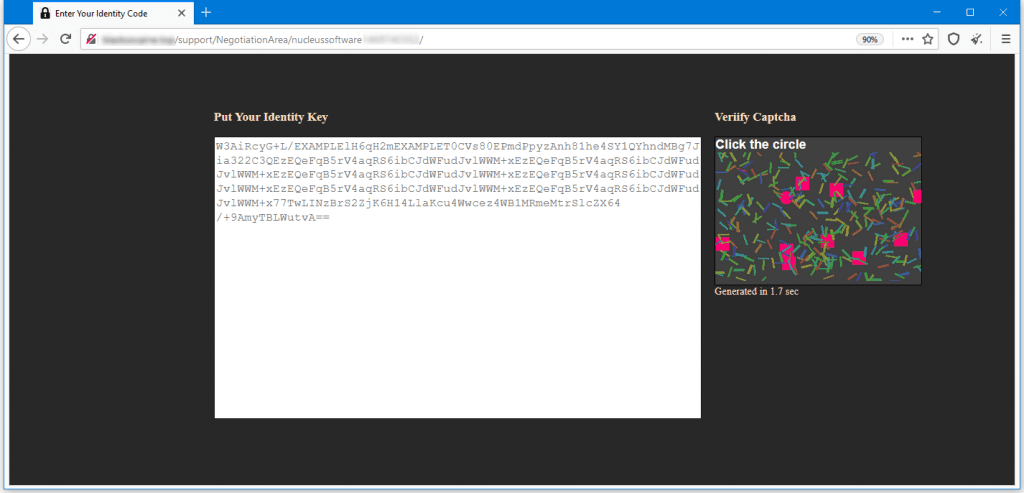
The ransomware, identified as BlackCocaine, but more commonly known as EpsilonRed, is among the most recent ransomware strains discovered.
First spotted last month by UK security firm Sophos, the EpsilonRed gang works by targeting unpatched Microsoft Exchange email servers vulnerable to the ProxyLogon exploit, getting a foothold on the vulnerable system, and then deploying a collection of PowerShell scripts to allow it to move internally inside a victim's network.
In its report, Sophos said the ransomware gang has been successful in at least some of their attacks, discovering payments of $210,000 from previous incidents.
While NSE has not confirmed that the entry point for their breach was an Exchange server nor if it paid the ransom demand, the incident proves that even with tools that Sophos described as "bare-bones," a ransomware gang was capable of infiltrating a major financial software supplier and hold it for ransom with little effort.
But because the ransomware is still new, its code is not yet top-notch. An Emsisoft malware analyst, which took a look at the BlackCocaine/EpsilonRed sample, recommended that companies to reach out in case of an attack, as there might be ways to recover files under certain conditions.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.