DOJ to go after government contractors who don't disclose breaches
The US Department of Justice has announced today plans to pursue government contractors who hide or fail to notify the government about cyber-security breaches.
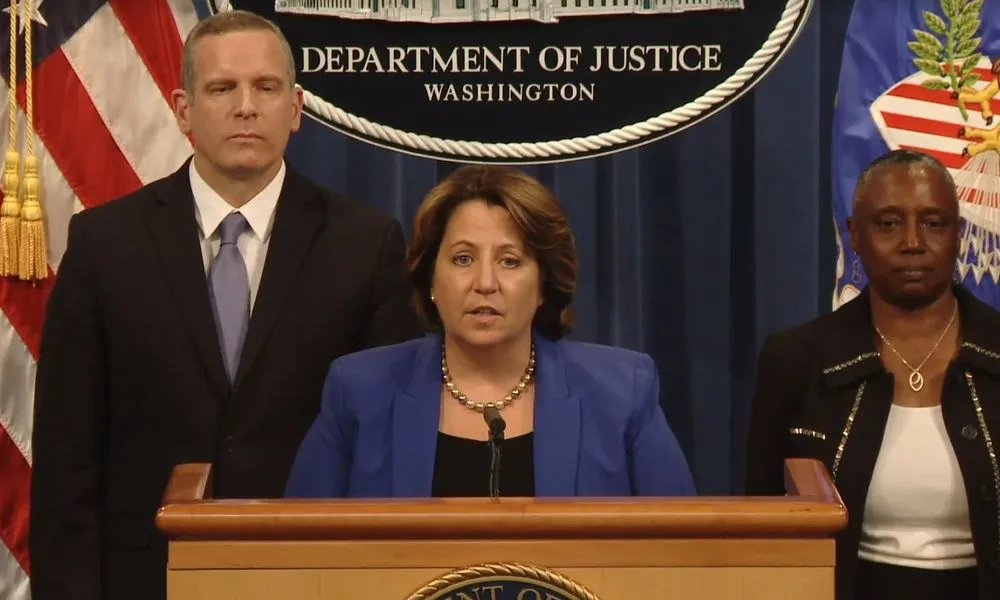
Named the Civil Cyber-Fraud Initiative, the new team will operate inside the Justice Department's fraud investigation and litigation branch, Deputy Attorney General Lisa O. Monaco said today at the Aspen Cyber Summit.
Monaco said the Civil Cyber-Fraud Initiative would use the False Claims Act to pursue government contractors, recipients of government grants, and anyone who takes funds from the US government but then fails to adequately secure its networks or hides security breaches.
"For too long, companies have chosen silence under the mistaken belief that it is less risky to hide a breach than to bring it forward and to report it," Monaco said.
"Well that changes today. We are announcing today that we will use our civil enforcement tools to pursue companies, those who are government contractors who receive federal funds, when they fail to follow required cybersecurity standards," she added.
Monaco said the initiative is meant to improve cybersecurity across the entire US government by ensuring that external contractors aren't weak links in the US federal network.
The creation of the Civil Cyber-Fraud Initiative comes after the US government has dealt with the aftermath of several hacks that targeted external entities but indirectly allowed threat actors to access government data or impact. This includes the attacks on IT company SolarWinds and attacks targeting Microsoft Exchange software, broadly used across the US government IT network.
In addition, Monaco also announced today the creation of a second initiative inside the Justice Department. Named the National Cryptocurrency Enforcement Team, this team will be tasked with pursuing criminals who abuse cryptocurrency for crimes and money laundering.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.