DHS chief lays out a cybersecurity vision with a focus on ransomware and infrastructure
The top official at the Department of Homeland Security announced today a series of 60-day cybersecurity “sprints” aimed at focusing the department’s efforts on ransomware, industrial control systems, and other priorities.
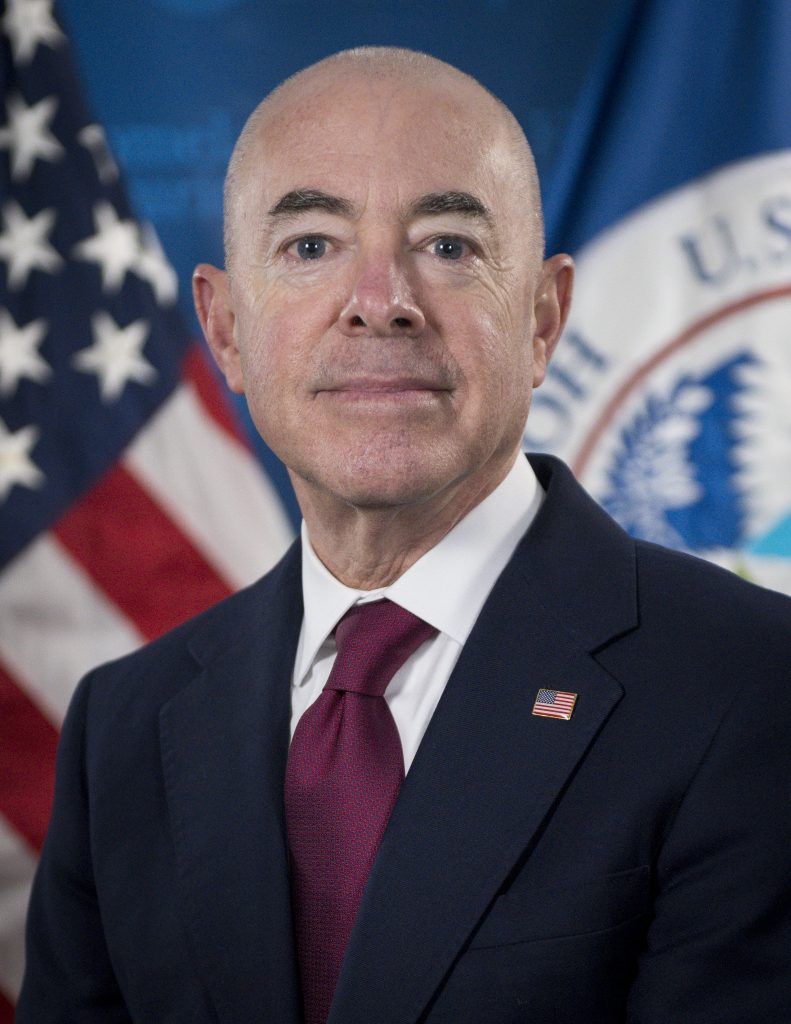
Alejandro Mayorkas, who was sworn in as DHS Secretary last month, said during a virtual talk hosted by the RSA Conference that his department is working on a proposal for a “Cyber Response and Recovery Fund” to provide assistance to state, local, tribal and territorial governments dealing with cyberattacks. He also announced an upcoming awareness campaign to highlight resources and services that the DHS’s Cybersecurity and Infrastructure Security agency has to offer, and gave additional details about an anticipated cybersecurity-focused executive order that will contain “nearly a dozen actions” involving detection, information sharing, responding to cyberattacks, and modernizing federal cybersecurity procurement.
The announcement comes as the DHS and the Biden administration confront an onslaught of high-profile cybersecurity incidents, including a sprawling breach attributed to Russia that has impacted a wide variety of government agencies and private companies. On Monday, the Associated Press reported that the hackers behind the SolarWinds compromise even gained access to email accounts belonging to DHS Secretary Chad Wolf and members of the department’s cybersecurity staff who were tasked with hunting foreign threats.
Additionally, cybersecurity officials have been dealing with the fallout from exploited vulnerabilities in Microsoft Exchange servers—the company said a Chinese hacking group had been targeting the flaws—as well as the news last month that hackers accessed a Florida water treatment plant and attempted to change the levels of sodium hydroxide to poisonous amounts. The attack was stopped before it could inflict harm on Tampa area residents.
“Our government got hacked last year and we didn't know about it for months,” Sec. Mayorkas said of the SolarWinds attack, emphasizing that the only reason the government learned about it was because FireEye, a private security firm, had disclosed a related incident. He said that increased information sharing between the public and private sectors is needed to better detect and respond to future attacks.
All eyes on CISA
Sec. Mayorkas, who served as Deputy Secretary of the department under President Barack Obama and was previously the Director of United States Citizenship and Immigration Services, repeatedly mentioned the key role that CISA would play for federal cybersecurity efforts, calling the agency the government’s “quarterback” and “tip of the spear” on such issues.
Although CISA is one of the youngest federal agencies, having been stood up about three years ago, Sec. Mayorkas said it was positioned to take a leading role especially after CISA helped secure the 2020 election from foreign interference and cyberattacks.
Lawmakers have argued recently that one gap in the federal government’s defensive posture is that so many agencies and departments play a role, but there isn’t necessarily one that steers the ship: the Federal Bureau of Investigation, the U.S. Secret Service, the National Security Agency, U.S. Cyber Command, and even the National Institute of Standards and Technology all play key roles in cybersecurity alongside CISA, and their responsibilities often overlap. That could potentially make it harder for the federal government to detect attacks and orchestrate a unified response.
Gen. Paul Nakasone, who leads the NSA and Cyber Command, said in a hearing last week that not one of these agencies is positioned at the moment take on that leadership role—the NSA, for example, only focuses on foreign adversaries, which results in a “blind spot” when those attackers use domestic infrastructure to attack U.S. targets. Although Gen Nakasone did not make specific policy suggestions, he said the agencies he leads were not necessarily the ones that had to have these cybersecurity authorities—some lawmakers have also suggested that CISA would be a better fit given its mandate.
“The government seeks to speak with one voice, but too often we speak through different channels,” Sec. Mayorkas said, adding that CISA has become the private sectors “most trusted interlocutor” and is well positioned to play a cybersecurity leadership role for the federal government.
Sprinting ahead
In his talk, which was positioned as a roadmap for the department’s cybersecurity efforts, Sec. Mayorkas emphasized several areas that he saw as short and medium-term priorities.
Although his video feed cut out while he was introducing these areas of focus, it appeared that ransomware and defending industrial control systems were top-of-mind for the department. He said DHS intended to soon focus on additional issues, including transportation systems, election security, and international capacity building—basically, helping other countries on cybersecurity issues.
Sec. Mayorkas said his four medium-term priorities were the resilience of democratic institutions, “building back better” or modernizing federal IT systems, addressing supply chain risks like the ones seen in the SolarWinds compromise, and looking beyond the crisis of the day to emerging threats like post-quantum encryption.
As the U.S. relies more on the internet and as foreign adversaries continue to target those technologies, Sec. Mayorkas warned that the stakes are increasing to unprecedented levels.
“Cyberthreats are coming dangerously close to threatening our lives,” he said.
Adam Janofsky
is the founding editor-in-chief of The Record from Recorded Future News. He previously was the cybersecurity and privacy reporter for Protocol, and prior to that covered cybersecurity, AI, and other emerging technology for The Wall Street Journal.



