DDoS attacks hit multiple email providers
At least eight email service providers have been hit by large distributed denial of service (DDoS) attacks over the weekend resulting in prolonged outages, The Record has learned from sources familiar with the incidents, all of which have been carried out by the same threat actor as part of a DDoS extortion campaign.
The attacks, which began on Thursday, October 21, and have continued throughout the weekend and on Monday, have targeted Runbox, Posteo, Fastmail, TheXYZ, Guerilla Mail, Mailfence, Kolab Now, and RiseUp–all small-time companies that provide privacy and security-centric email services.
Victims were targeted with a DDoS attack, and an email was later sent to the organizations, asking for a 0.06 BTC (~$4,000) ransom demand. Companies were given three days to pay, with the attackers threatening to take their networks offline if they didn't pay, according to a copy of the email seen by The Record.
"We have received a threatening letter and a demand for money," Posteo also confirmed in a blog post on Friday. The company said it did not intend to pay.
Some DDoS attacks peaked at 256Gbps
In blog posts after this article's publication, Runbox and TheXYZ also confirmed receiving similar ransom demands. The emails came after DDoS attacks that peaked at 50Gbps and 256Gbps, respectively, the two companies said.
The emails in this campaign were signed by a group calling itself the Cursed Patriarch, and after their campaign was exposed, later emails also incorporated a link to this article.
This extortion campaign is, however, unrelated to DDoS attacks that have hit UK VoIP provider Voipfone and gaming server provider Sparked. According to a source familiar with the matter, these two attacks have been carried out by different threat actors, unrelated to the coordinated extortion campaign on email providers.
While generally overshadowed by the extortion attempts orchestrated by ransomware gangs, threat actors who rely on DDoS attacks to force companies to pay ransom requests are still very active.
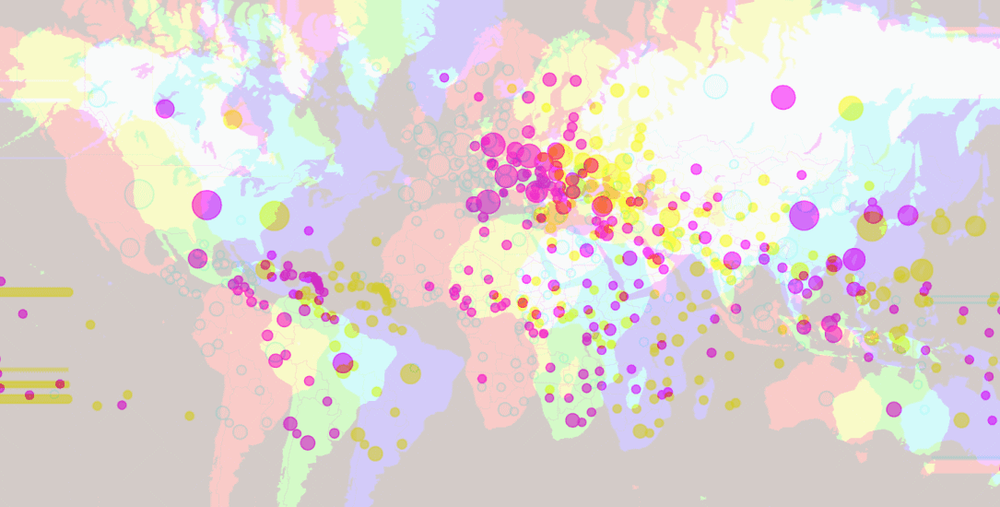
Last month, several DDoS extortion attempts were registered against internet service providers and financial entities across several countries, such as Russia, the UK, the US, and New Zealand—with some of the attacks being carried out using a new botnet called Meris.
Article updated on Monday, October 25, to add details about attacks on five other providers, besides the initial three.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.