‘Cyberspace has become a battleground,’ warns Australian Cyber Security Centre
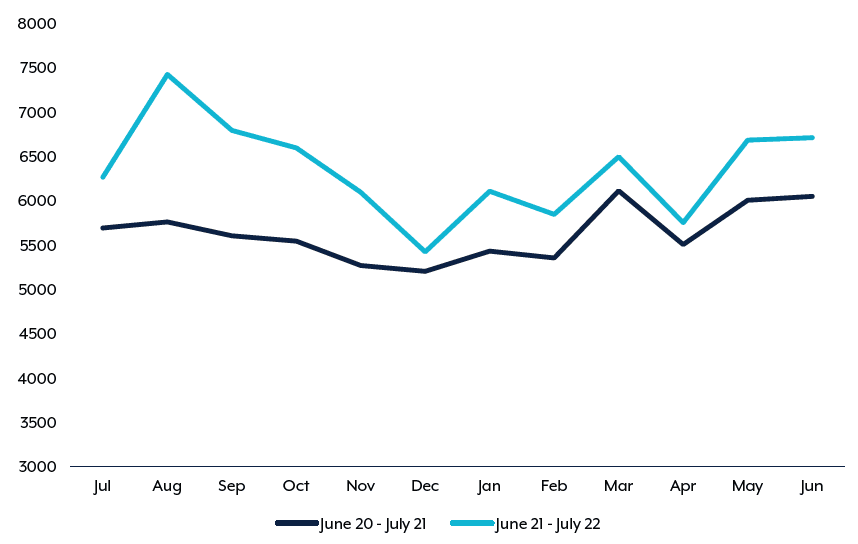
The Australian Cyber Security Centre received over 76,000 cybercrime reports during the last financial year — an increase of nearly 13% — and warned in its latest annual report that “cyberspace has become a battleground.”
“We are currently witnessing deteriorating strategic circumstances in our region and globally, including a military build-up unseen since World War II, and expanding cyber and gray zone capabilities are of particular concern,” the report stated.
The agency also warned that the regional dynamics in the Indo-Pacific were “increasing the risk of crisis” and cautioned that “cyber operations are likely to be used by states to challenge the sovereignty of others.”
In its annual publication on Friday, covering the year until June 2022, the agency said it received the equivalent of one cybersecurity incident report every seven minutes. It warned the "increase in the number and sophistication of cyber threats" was making "crimes like extortion, espionage and fraud easier to replicate at a greater scale."
The agency stated it had:
- Responded to more than 1,100 cyber security incidents, including 135 ransomware incidents, which was an increase of over 75%
- Seen Australians lose over AUS $98 million ($62 million) to business email compromise incidents, averaging AUS $64,000 ($41,000) per report
- Losses resulting from other cybercrime rose 14% on average, to over AUS $39,000 ($25,000) for small business, AUS $88,000 ($56,000) for medium business, and over AUS $62,000 ($39,000) for large businesses. It is not clear why large business losses were on average smaller than those for medium-sized enterprises.
‘Sophisticated actors’
The agency shared limited details about a forensics investigation at an Australian energy provider, following the public disclosure of a vulnerability in April. Initially its specialists had aimed to “reconstruct the steps taken by the malicious actors” who were fortunately not able to disrupt energy operations.
However their investigation “found that multiple instances of successful exploitation of the vulnerability occurred in a very short period of time,” reported the ACSC.
“Evidence suggests that exploitation was conducted by multiple actors, including state-sponsored and criminal entities, much of which was likely automated. Sophisticated actors sought to access user login data, with the likely intent to gain more persistent access once the compromise was remediated.”
Although no attribution was given for the state-sponsored entities in the report, the incident took place the same month that the ACSC released a joint advisory with the other Five Eyes members on the threat that Russian state and criminal actors posed to critical infrastructure.
The report follows the country's attorney-general announcing the government's intention to strengthen its online privacy laws after several major data breaches.
One of the country’s largest health insurers, Medibank, which initially claimed to have foiled a ransomware attack — saying that it had found “no evidence customer data has been removed from our network” — subsequently confirmed that criminals had access to all of the personal data of all of its customers.
In September, the country’s second-largest telecommunications company, Optus, announced the compromise of the personal information of almost 10 million Australians, about 40% of the population.
After the Optus incident, Australia’s Cyber Security Minister Clare O’Neil said that Australia is “probably a decade behind” in privacy protections, and the government “has to be involved when the stakes are this high.”
Alexander Martin
is the UK Editor for Recorded Future News. He was previously a technology reporter for Sky News and a fellow at the European Cyber Conflict Research Initiative, now Virtual Routes. He can be reached securely using Signal on: AlexanderMartin.79



