Cybercrime group targeting banks in African Francophone countries
A cybercriminal group continues to target banks and financial institutions in Francophone countries across Africa, with attacks spreading since the outfit was first observed in 2018.
In a report published Thursday by Symantec, the researchers examined a recent campaign by a group they’ve named Bluebottle, which several other cybersecurity firms have investigated in recent years.
“Three different financial institutions in three African nations were compromised in the activity seen by Symantec, with multiple machines infected in all three organizations,” the researchers said. "The effectiveness of its campaigns means that Bluebottle is unlikely to stop this activity. The attackers appear to be French speaking, so the possibility of them expanding this activity to French-speaking nations in other regions also cannot be ruled out.”
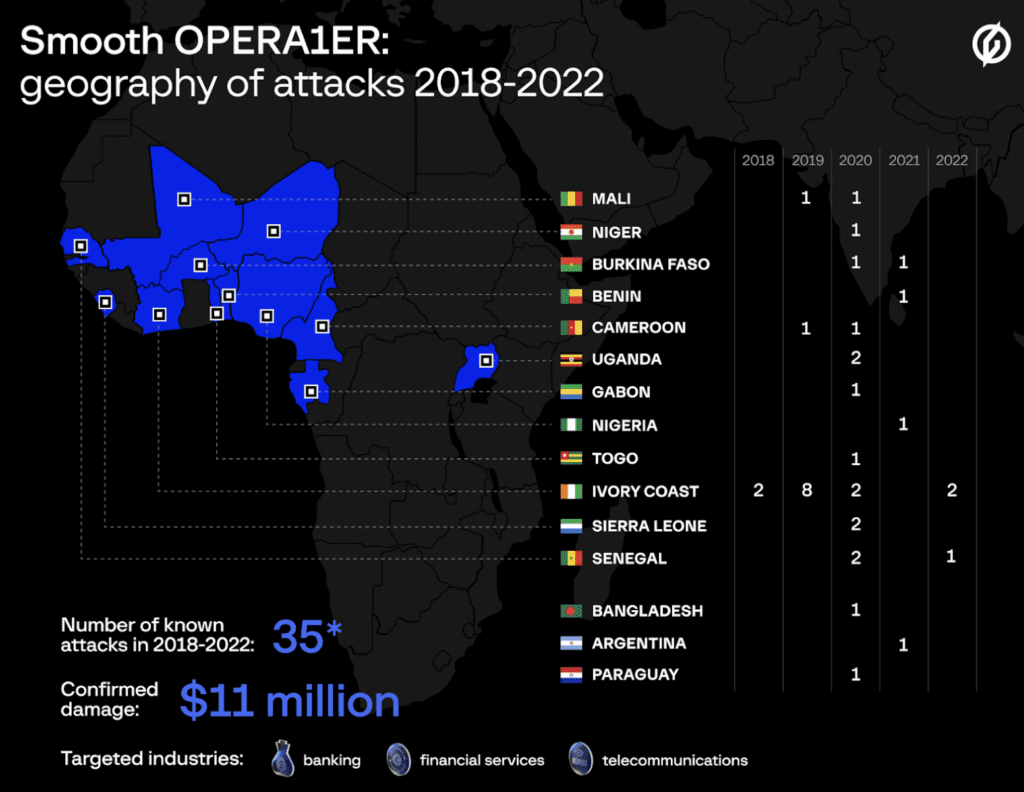
Symantec found that the group does not use custom malware in its attacks and demonstrates several similarities to the campaign uncovered by the cybersecurity company Group-IB, which tracked attacks on financial institutions in Ivory Coast, Mali, Burkina Faso, Benin, Cameroon, Gabon, Niger, Nigeria, Paraguay, Senegal, Sierra Leone, Uganda, Togo and others.
Group-IB documented a campaign by the same group – tracked by the company as OPERA1ER – that lasted three years, in which the group stole at least $11 million and potentially as much as $30 million in 30 different attacks on banks, financial services, and telecommunication companies mainly located in Africa between 2018 and 2022.
Both campaigns also had tools with industry-specific, and region-specific, domain names. The campaign tracked by Symantec lasted from about May 2022 to September 2022 and involved the use of GuLoader, a remote access trojan used frequently over the last two years.
Symantec was unable to identify the initial infection vector but said the earliest malicious files they found on victim networks had French-language, job-themed file names.
These files were likely used as lures to begin the attack, the researchers explained, noting that in some cases, the malware was named to trick the user into thinking it was a PDF file.
Examples of file names included: fiche de poste.exe ("job description"), fiche de candidature.exe ("application form"), and fiche de candidature.pdf.exe ("application form").
“It’s most likely these files were delivered to victims via a spear-phishing email, which would align with the initial infection vector documented by Group-IB for the OPERA1ER activity,” Symantec said.
“Although the majority of the activity observed by Symantec researchers began in July 2022, at least one victim was found to have an infostealer with a similar naming theme on its network as early as mid-May 2022,” they said, adding that the infection vector was consistent with what Group-IB saw with OPERA1ER.
One strange thing Symantec found was evidence the malware had been mounted as a CD-ROM, indicating a genuine disc was inserted into the computer.
When it comes to the GuLoader malware used, the researchers found that it was often attached to ieinstal.exe, the Internet Explorer Add-on Installer.
The group also used another malware designed to disable security products on victim networks.
“In August 2022, Symantec observed the same driver being used in suspected pre-ransomware attack activity against a non-profit in Canada. Another tool found on the victim network was Infostealer.Eamfo, a hacktool that has been associated with Cuba, Noberus, and Lockbit ransomware attacks,” Symantec said.
“The same driver also appears to have been used by multiple groups for similar purposes. Mandiant documented a financially motivated threat group it calls UNC3944 using this same driver to disable defenses.”
Mandiant noted in their report that the tool was used by several cybercriminal groups and cybersecurity firm Sophos found it in use by Cuba ransomware operators.
“While Symantec cannot confirm whether or not Bluebottle successfully monetized the campaigns we saw it carrying out, the group’s success at monetizing its activity between 2019 and 2021, as documented by Group-IB, indicates that this group has had a significant amount of success in the past,” the researchers said.
“It appears to be very focused on Francophone countries in Africa, so financial institutions in these countries should remain on high alert for the activity documented in this blog.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



