Cryptocurrency apps were heavily targeted by Android banking trojans in 2020
Android banking trojans had their most productive year to date in 2020, a year during which they more than doubled the number of apps they targeted for data theft.
In a report shared with The Record today, Dutch mobile security firm ThreatFabric said the operators of Android banking trojans created and deployed fake login screens (called overlays) for 1,980 different mobile apps in 2020.
The figure is a 129% increase to the 882 overlays deployed by Android banking trojans a year before, in 2019.
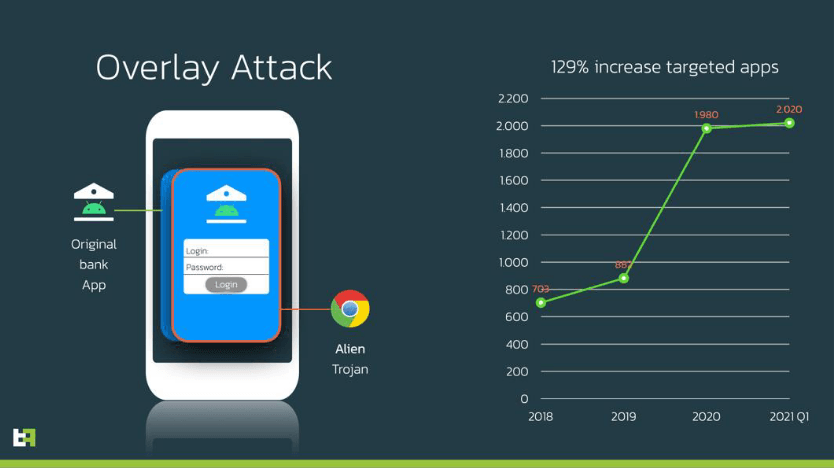
Overlays are pixel-perfect clones of a legitimate app's login screen.
An Android banking trojan uses overlays after it infects a device. The trojan works by keeping an eye on what apps a user is opening and showing the "overlay" on top of a legitimate app, tricking the user into entering login credentials that will be sent to the attacker.
Creating pixel-perfect overlays is a complex and time-consuming process.
Because most banking trojans are offered for rent on underground forums, the authors of banking trojans usually create overlays based on requests they receive from their customers.
Across the years, every time a mobile banking trojan launched, it usually took months or years for a banking trojan operator to build up its overlay portfolio (the apps it could target) because creating each app took time and resources.
This is why 2020 was such a noticeable year in terms of banking trojan operations.
The sudden explosion in the number of overlays created and deployed on the market suggests a thriving mobile banking scene, where trojan operators were busier than ever.
Most mobile banking trojans targeted cryptocurrency apps
ThreatFabric said that while the vast majority of targeted apps were e-banking applications, cryptocurrency apps also saw a lot of attention last year.
Overlays for the official Blockchain.com and Coinbase wallet apps were the top two most common banking trojan overlays spotted in samples discovered last year, ThreatFabric said.
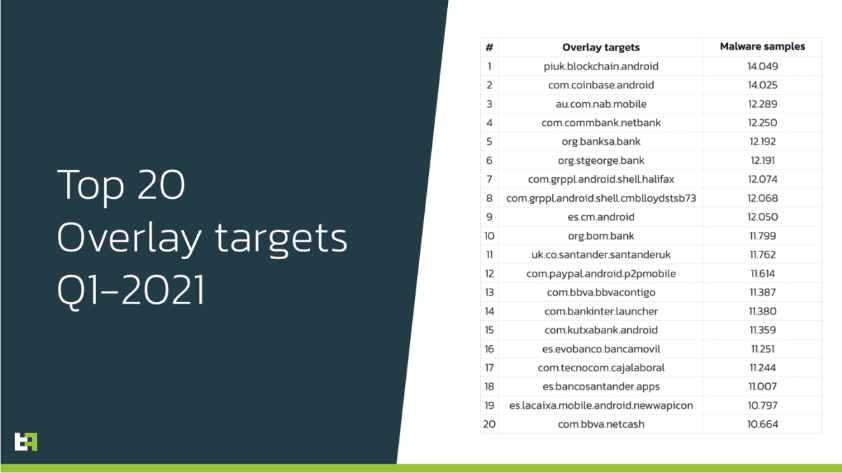
"With many different crypto-currencies hitting their highest market value in 2021, populating newsfeeds all over the world and now more than ever being discussed extensively in mainstream media, it is not a surprise that cryptocurrency wallets are the most common targets for this new wave of banking trojans," ThreatFabric said.
"Another important fact to consider is that, while banking apps tend to have different versions of their APK based on the country they serve, crypto-wallets tend to have one unique APK, making it easier for malicious actors to target them."
Android bankers are now on par with their desktop counterparts
But another commonality among banking trojans like Gustuff, Alien, Medusa, EventBot, Anatsa, or FluBot last year was the fact that they now appear to have reached parity with desktop-targeting banking trojans.
Since the early 2010s, most desktop banking trojans had come with a feature called an ATS.
Standing for Automated Transfer System, this feature allowed desktop banking trojans to initiate transactions on the infected device, on victim's behalf, allowing crooks to steal funds from a compromised account.
While there have been some Android banking trojans that experimented with an ATS in previous years, according to ThreatFabric, 2020 was the first year when ATS was a standard feature in almost all Android banking trojans.
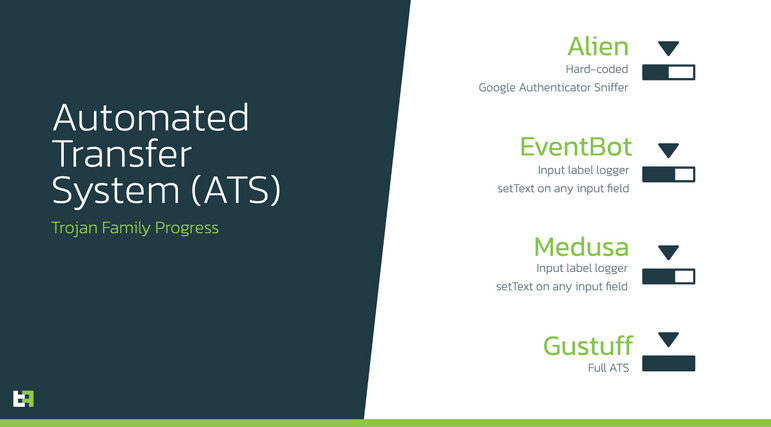
ThreatFabric said that most of these ATS mechanisms had been built around the Android Accessibility service, a feature of the Android OS that allows apps to mimic screen taps and take actions on behalf of users with various disabilities.
In previous years, some Android bankers used the Accessibility service to download a remote control app like VNC or TeamViewer, which allowed crooks to manually log into user devices and steal funds when needed.
However, ThreatFabric said that in recent months, some Android banking trojan operators have realized they could also use the Accessibility together with other Android native code, such as the RTSP protocol, to stream a device's screen in real-time to an attacker server and control the device without the help of VNC or TeamViewer.
"This attack vector is achieved by abusing Accessibility features of the Android operating system," ThreatFabric said.
"Chaining this native screen streaming feature of Android with Accessibility controls, such as performing actions (clicks) on the victims' behalf, results in a full hidden Remote Access Trojan (RAT)," ThreatFabric said. "We can consider these developments a significant threat to mobile payments on the Android platform."
The company expects mobile trojans to evolve further, especially since some groups are moving away from advertising their offerings on hacking forums to private channels.
Coupled with the doubling of detected overlays, this suggests the Android mobile banking scene is now profitable enough to fuel its own development through a closed community of threat actor groups—made up of coders, distributors, spammers, and money mules.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.