Costa Rica’s new president declares state of emergency after Conti ransomware attack
The newly-inaugurated president of Costa Rica – Rodrigo Chaves – declared a state of emergency due to a devastating ransomware attack launched by the Conti group.
Following his swearing-in ceremony on Sunday, Chaves held his first government council, where he announced a national emergency and attributed it to the attack’s effects on the Ministry of Finance, which has been hit hardest by the attack.
#EnDesarrollo El presidente @RodrigoChavesR declara emergencia nacional por los ciberataques en sistemas informáticos de varias instituciones del país pic.twitter.com/ttFmh3DZUe
— Amelia Rueda (@ameliarueda) May 8, 2022
Two weeks ago, the country’s outgoing president Carlos Alvarado Quesada said the attack was meant to “threaten the stability of the country in a transition situation” and that the country would refuse to pay the reported $10 million ransom.
The attack crippled the country’s customs and taxes platforms alongside several other government agencies, even bringing down one Costa Rican town’s energy supplier. The country’s treasury department has been unable to operate any of its digital services since the attack began, making it nearly impossible for paperwork, signatures and stamps required by law to be processed.
Organizations affected by the attack include:
- The Finance Ministry
- The Ministry of Science, Innovation, Technology, and Telecommunications
- The Labor and Social Security Ministry
- The Social Development and Family Allowances Fund
- The National Meteorological Institute
- The Costa Rican Social Security Fund
- The Interuniversity Headquarters of Alajuela
Finance Minister Elian Villegas told Reuters at the end of April that the group breached the platforms managing customs, which included troves of historical taxpayer information considered “sensitive.”
One exporter union estimated after the attack that $200 million was lost due to the bottlenecks caused by outages related to the disruption of the tax and customs platforms.
The Finance Ministry warned the country’s residents to be wary of phishing messages asking to create a new set of passwords.
Business leaders told the Associated Press that they were fearful of financial and personal information being stolen, leaked to the press or sent to government officials. Conti has threatened to leak troves of sensitive information related to government officials and regular citizens.
Conti released its own message on Sunday, dumping most of the 672 GBs of files they stole and criticizing the country for refusing to pay the ransom. The message explicitly mentioned Costa Rica’s decision to seek help from the United States for dealing with the ransomware attack.
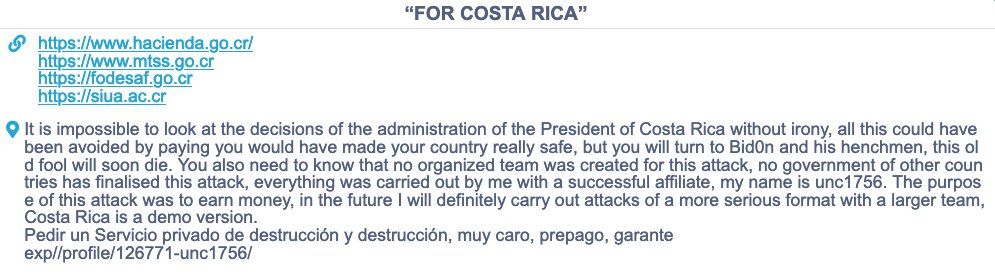
Calling themselves “unc1756,” the hacker claimed only two people were involved in the attack and that it was not launched by another country – something Quesada implied in his speeches about the incident.
"It is impossible to look at the decisions of the administration of the President of Costa Rica without irony, all this could have been avoided by paying you would have made your country really safe, but you will turn to Biden and his henchmen, this old fool will soon die,” the Conti member said.
“The purpose of this attack was to earn money, in the future I will definitely carry out attacks of a more serious format with a larger team, Costa Rica is a demo version.”
Costa Rican news outlet Amelia Rueda reported that executive decree No. 42542 covers “the entire public sector of the Costa Rican State” and calls Conti operators “cyberterrorists.”
The outlet noted that the Finance Ministry is still unsure of what information was stolen related to taxpayers and businesses.
The announcement about a state of emergency comes two days after the U.S. State Department issued a $10 million bounty for information about Conti operators.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



