IBM: Cost of data breaches reaches all-time high of $4.5 million in 2023
The cost of a data breach has become higher than ever, according to the latest annual report from IBM that found organizations are now paying $4.5 million to deal with breaches – a 15% increase over the last three years.
In a report published by IBM Security this week, researchers at the Ponemon Institute examined data breaches at 553 organizations in 17 different industries across 16 countries and regions from March 2022 to March 2023.
The researchers calculate the cost of a breach based on several factors, but most of the expense can be traced back to the cost of hiring a company to conduct an investigation into the breach – which the researchers call “detection and escalation.”
These include “activities that enable a company to reasonably detect a breach and can include forensic and investigative activities, assessment and audit services, crisis management, and communications to executives and boards.”
That accounted for $1.6 million on average – the top cost involved in a breach. The other key cost is lost business, post-breach response and notification. Business disruption and system downtime costs – which involve the expenses related to the loss of customers, the acquisition of new customers, reputation losses and “diminished goodwill” – dropped in 2023 from $1.4 million to $1.3 million.
The cost of breach notifications also rose in 2023 to $370,000 due to increased expenses related to notifying victims, regulators and third party organizations.
The countries and regions with the highest costs per breach largely stayed the same as 2022, with the U.S., Middle East and Canada holding on to the top three spots again in 2023.
The U.S. had a whopping $9.5 million cost per breach, outpacing every other region or country by more than $1 million per breach. Healthcare organizations led all other industries in terms of average cost of a breach, topping out at $10.9 million while no other industry had an average cost above $6 million.
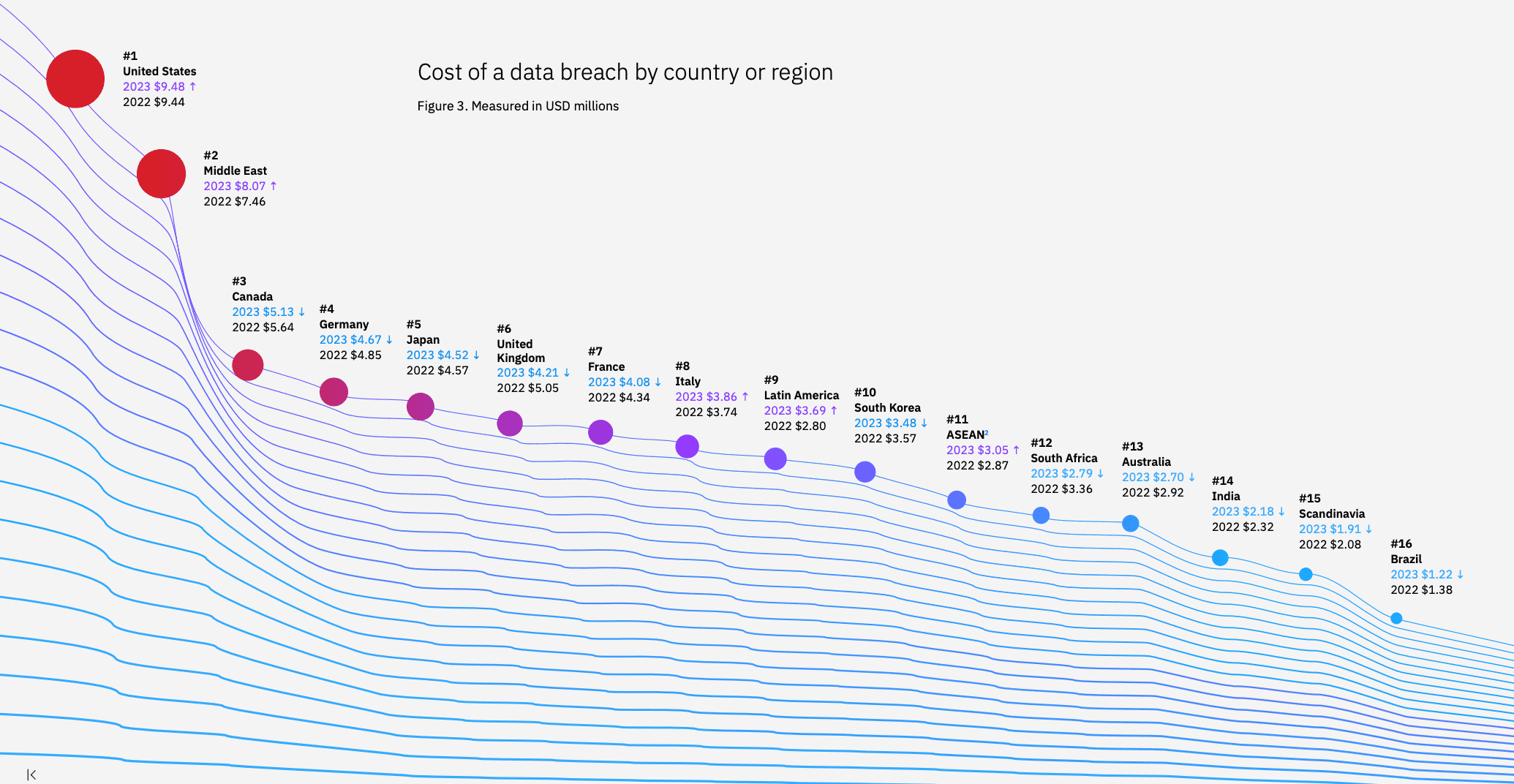 Image: IBM
Image: IBM
“Healthcare faces high levels of industry regulation and is considered critical infrastructure by the US government. Since the start of the COVID-19 pandemic, the industry has seen notably higher average data breach costs,” the researchers said.
The financial, pharmaceuticals, energy and industrial sectors rounded out the top five, with technology dropping out of the top five compared to 2022.
IBM noted that the time it took organizations to identify a breach was 204 days in 2023, only dropping by three days compared to 2022.
“Time is the new currency in cybersecurity both for the defenders and the attackers. As the report shows, early detection and fast response can significantly reduce the impact of a breach," said Chris McCurdy, general manager with Worldwide IBM Security Services.
Passing costs to customers
The study found that with the rising cost of breaches, businesses typically passed the costs on to consumers, raising the prices of goods and services as a result of breaches. Nearly 60% of respondents told IBM that they increased their prices following a breach.
The researchers noted that those price increases were ironic considering the costliest data to have compromised in 2023 was customers and employee information. Customer personal information like names and Social Security numbers cost organizations $183 per record compared to other data which typically cost around $140 per record.
Customer personal information was also the most commonly breached record type in 2023, IBM added, with 52% of all breaches involving some kind of customer data.
Phishing and stolen credentials were the top attack vectors for the hackers behind breaches, with both accounting for 16% and 15% of all breaches respectively.
One new aspect of the annual report was an examination of ransomware attacks. IBM found that data breaches disclosed by the attacker, as most ransomware attacks are, cost significantly more than other breaches, with an average cost of $5.2 million. Almost 25% of all breaches involved ransomware in 2023.
The report also focused on positive developments, most notably that organizations using some combination of threat intelligence, artificial intelligence and incident response tools all saw reduced amounts of time it took to identify a breach.
“Security teams must focus on where adversaries are the most successful and concentrate their efforts on stopping them before they achieve their goals,” McCurdy said. “Investments in threat detection and response approaches that accelerate defenders speed and efficiency – such as AI and automation – are crucial to shifting this balance.”
Organizations that involved law enforcement also saw savings both in terms of time spent and cost. Nearly 40% of ransomware victims did not involve law enforcement at all, but those that did saw lower overall breach costs.
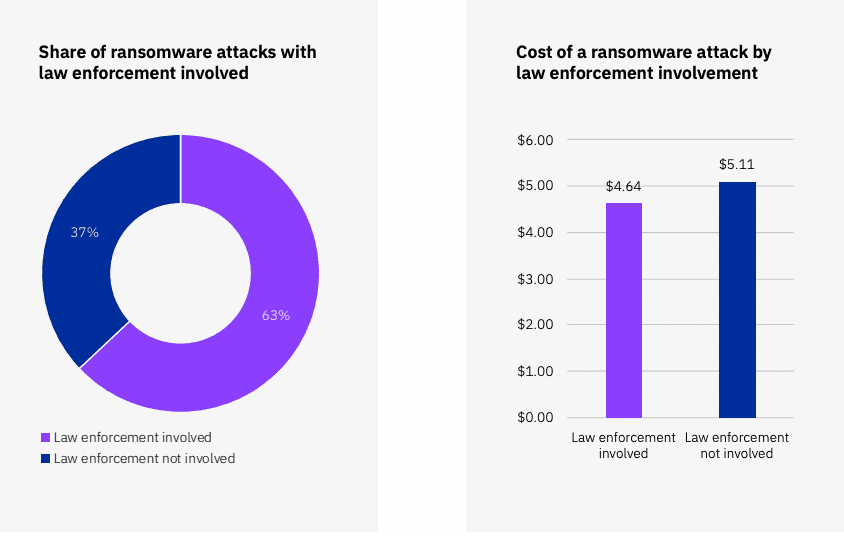 Image: IBM
Image: IBM
When law enforcement was involved, the average cost of a ransomware breach fell to $4.6 million.
“Law enforcement helped shorten time to identify and contain ransomware breaches. Total time to identify and contain a ransomware breach was 11.4%, or 33 days, shorter with law enforcement involvement, at 273 days in total compared to 306 days,” IBM said.
“The mean time to contain a ransomware breach was 63 days, or 23.8%, shorter with law enforcement involvement compared to 80 days without. It’s clear that involving law enforcement can help reduce the cost and duration of a ransomware breach.”
The report notes that paying ransoms “led to minimal cost savings” of an average of $110,000. But that figure does not include the cost of the ransom itself – leading the researchers to believe that overall, ransomware victims that paid ransoms ended up spending more overall than those that did not pay.
Regulation also played a role in when organizations dealt with costs. Organizations in high-data regulation environments saw their peak costs incur more than two years after a breach while those in low regulatory environments took on less than half of their data breach costs within the first year.
Less than 30% of organizations involved in the study faced any type of fine related to their data breach and those that were fined almost always paid less than $250,000.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



