Coinbase explains how ‘0ktapus’ hacker accessed corporate directory
Cryptocurrency platform Coinbase says a persistent cybercriminal connected to the 0ktapus hacking group ultimately used a social-engineering technique to break into the company’s corporate directory.
Company officials said late last week that an employee was fooled by a scam SMS message and then took a bogus phone call from the hacker.
The text messages — sent Sunday, February 5 to multiple employees — contained a phishing link and an urgent plea for people to log in to their work accounts. While most recipients ignored the message, one did click on the link and enter a username and password.
“What happened next was that the attacker, equipped with a legitimate Coinbase employee username and password, made repeated attempts to gain remote access to Coinbase. Fortunately our cyber controls were ready,” Coinbase’s Jeff Lunglhofer said. “The attacker was unable to provide the required Multi Factor Authentication (MFA) credentials — and was blocked from gaining access."
The lack of MFA credentials — like a code generated from an app, or a physical security key — typically "would be the end of the story,” as Lunglhofer puts it. It wasn't.
Lunglhofer explained that the first security barrier did little to dissuade the hacker. He noted that 0ktapus is “highly persistent and sophisticated” and has been accused of attacking several companies over the last year including Twilio, Cloudflare and more.
Whose voice is that?
The hacker eventually called the employee, claiming to be from Coinbase’s IT department. The employee entered their credentials into the phishing page, and the hacker eventually asked the person to log into their workstation and follow more instructions.
The employee became suspicious because of the kinds of requests and questions the alleged IT staff member was asking. The employee ended the conversation after being contacted by Coinbase’s Computer Security Incident Response Team (CSIRT).
In the end, Coinbase said the hacker gained access to “limited contact information for our employees” including employee names, e-mail addresses, and some phone numbers.
No user funds or information were accessed, according to Coinbase.
The CSIRT suspended the employee’s access to the company’s systems and began an investigation into the incident.
In addition to better security training for all employees, Lunglhofer suggested companies watch out for downloads involving remote desktop viewers like AnyDesk and ISL Online.
This is not Coinbase's first run in with hackers. In 2021 the company found that more than 6,000 of its users were robbed after attackers leveraged a vulnerability in its SMS-based two-factor authentication process to break into their accounts.
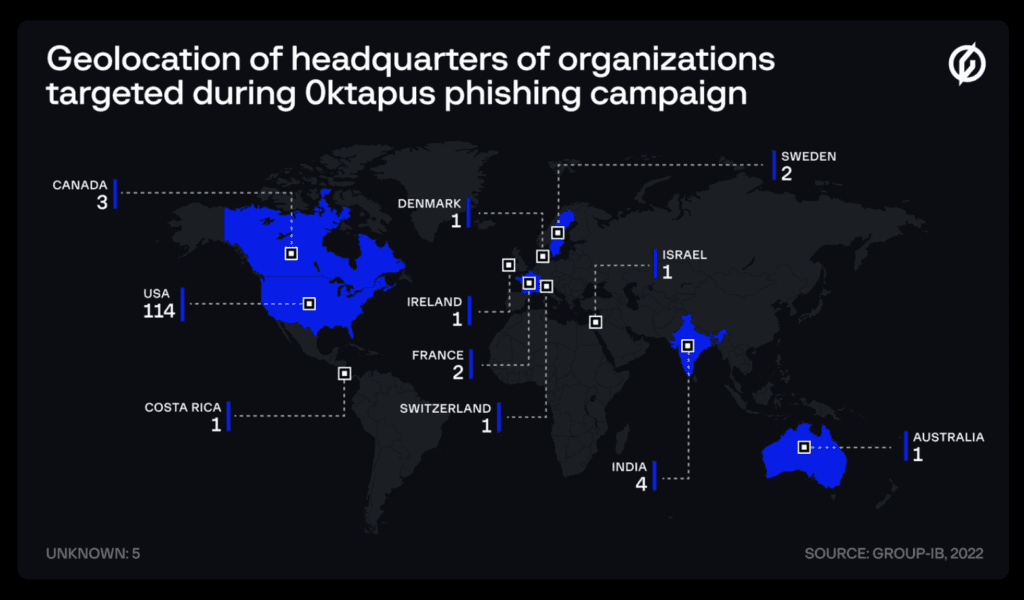
The 0ktapus hacking group has repeatedly targeted the employees of major technology companies with phishing attacks over the last year. A report from cybersecurity company Group-IB said the cybercrime campaign resulted in 9,931 thousand accounts of over 136 organizations being compromised.
The group is named “0ktapus” because it targets users of Okta’s Identity and Access Management services. Typically it sends victims to lookalike pages to steal Okta credentials.
“The methods used by this threat actor are not special, but the planning and how it pivoted from one company to another makes the campaign worth looking into,” said Rustam Mirkasymov, head of cyber threat research at Group-IB Europe.
It's unclear where 0ktapus is based, but it mostly targets U.S. companies.
“0ktapus shows how vulnerable modern organizations are to some basic social engineering attacks and how far-reaching the effects of such incidents can be for their partners and customers.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



