Microsoft, Fortra get legal permission to counter Cobalt Strike abuse
Microsoft and two partner organizations have been granted a court order to go after cybercriminal infrastructure associated with the rampant abuse of Cobalt Strike — a legitimate testing tool that attackers have used to wreak havoc on the healthcare industry.
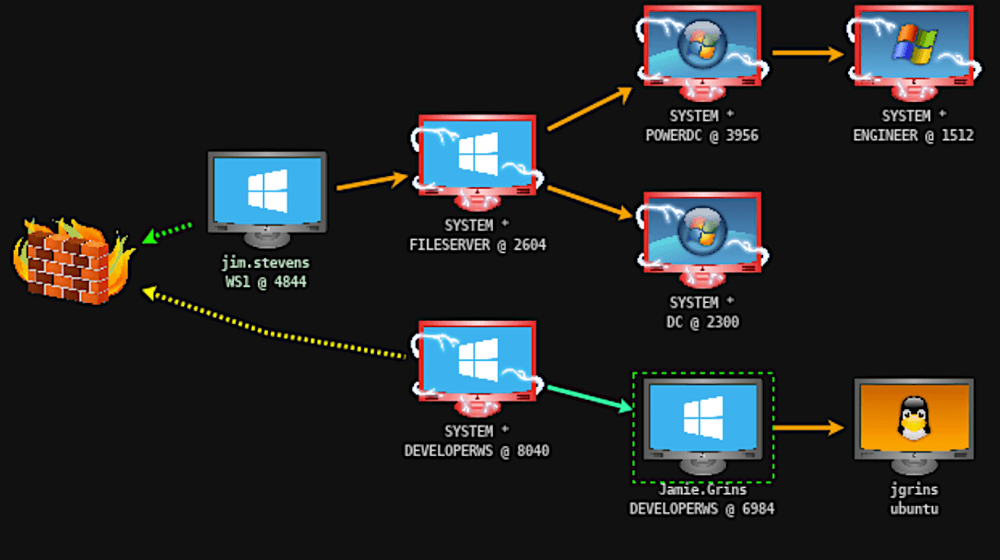
In an initiative announced Thursday, the company’s Digital Crimes Unit (DCU) — alongside the nonprofit Health Information Sharing and Analysis Center (Health-ISAC) and software maker Fortra — is working “to disrupt cracked, legacy copies of Cobalt Strike and abused Microsoft software, which have been used by cybercriminals to distribute malware, including ransomware.”
Fortra’s Cobalt Strike is an adversary simulator and penetration testing software used by red teams to detect vulnerabilities and plan response, but older versions of the program have been widely exploited by cybercriminals.
On March 31, the U.S. District Court for the Eastern District of New York issued an order allowing the three entities to go after the “malicious infrastructure” used in attacks, such as command-and-control servers.
“Doing so enables us to notify relevant internet service providers (ISPs) and computer emergency readiness teams (CERTs) who assist in taking the infrastructure offline, effectively severing the connection between criminal operators and infected victim computers,” Microsoft wrote. The company added that the initiative involves copyright claims for the use of software code that is “altered and abused for harm.”
Amy Hogan-Burney, general manager of cybersecurity policy and protection at Microsoft, said that going after the distribution methods of cybercriminals “is one of the best ways to disrupt the criminal ecosystem, forcing criminals to re-evaluate their tactics and decrease their ability to profit from their attacks.”
A global scourge
Using “detection, analysis, telemetry, and reverse engineering,” Microsoft and partners have tracked infrastructure worldwide, including in China, the U.S. and Russia, and they have observed nation-state groups in Russia, China, Vietnam and Iran using cracked copies of Cobalt Strike.
According to the announcement, the software has been used in more than 68 ransomware attacks on the healthcare sector in more than 19 countries. In 2021, the Department of Health and Human Services released a white paper about the tool and its targeting of healthcare organizations.
A cracked version of the software was also used by the Conti ransomware group to infiltrate the government of Costa Rica.
Microsoft and its partners are working with the FBI’s Cyber Division, the National Cyber Investigative Joint Task Force (NCIJTF) and Europol’s European Cybercrime Centre (EC3), they wrote.
Bob Erdman, associate vice president of development at Fortra, told The Record the company has been trying to slow down cybercriminals abusing its products “for quite some time.”
“Fortra expends a considerable amount of resources on researchers, infrastructure, and legal processes to combat these threats as well as enhance the product in every version to make it harder for malicious actors to abuse,” he said.
“Fortra has issued hundreds of DMCA [Digital Millennium Copyright Act] violation notices and other legal actions. … Relevant authorities have used criminal enforcement in the past, but this new action allows Fortra to greatly expand the disruption through civil enforcement with our partners.”
Jonathan Greig contributed to this story.
James Reddick
has worked as a journalist around the world, including in Lebanon and in Cambodia, where he was Deputy Managing Editor of The Phnom Penh Post. He is also a radio and podcast producer for outlets like Snap Judgment.