Cloudflare detects one of the largest DDoS attacks on record targeting crypto platform
Internet infrastructure company Cloudflare said today that it mitigated one of the largest volumetric distributed denial of service (DDoS) attacks that has been recorded to date.
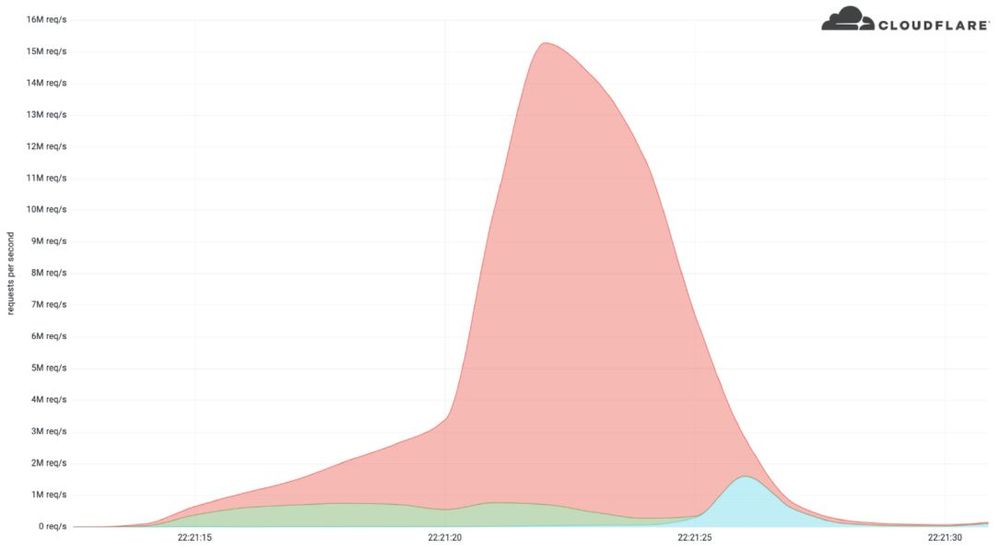
Cloudflare said it detected and mitigated a 15.3 million request-per-second (rps) DDoS attack earlier this month — making it one of the largest HTTPS DDoS attacks on record.
Volumetric DDoS attacks differ from traditional bandwidth DDoS attacks where attackers attempt to exhaust and clog up the victim’s internet connection bandwidth. Instead, attackers focus on sending as many junk HTTP requests to a victim’s server in order to take up precious server CPU and RAM and prevent legitimate users from using targeted sites.
Cloudflare previously announced that it stopped the largest DDoS attack on record in August 2021, when it mitigated a 17.2 million HTTP requests/second (rps) attack, a figure that the company described as almost three times larger than any previous volumetric DDoS attack that was ever reported in the public domain.
Earlier this month, the company said it stopped an attack targeting a company in the cryptocurrency space.
The attack, which lasted less than 15 seconds, was launched from a botnet of approximately 6,000 unique bots and originated from 112 countries around the world.
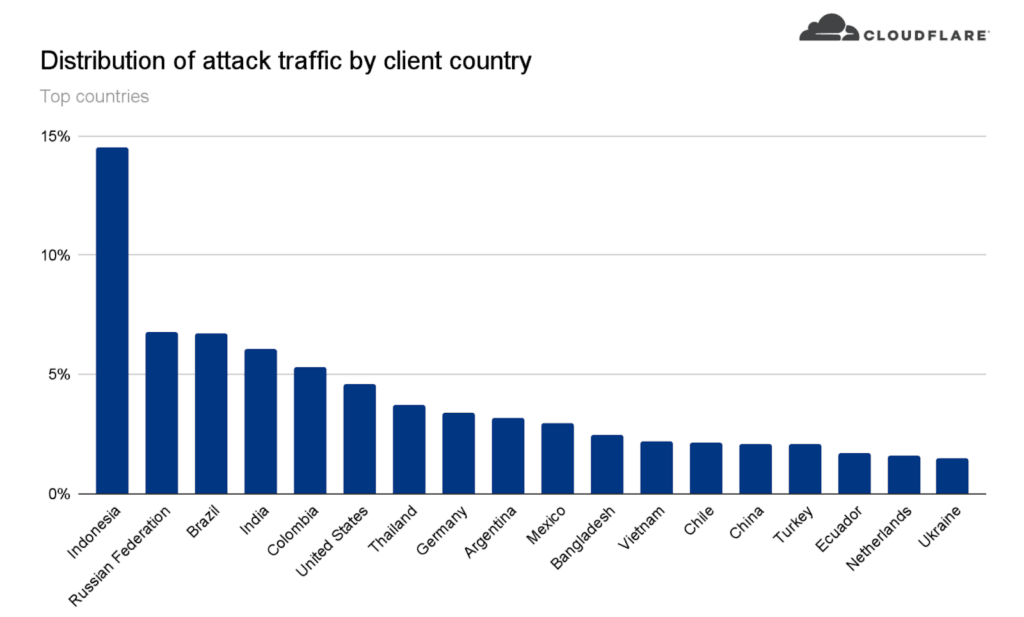
Almost 15% of the attack traffic originated from Indonesia, followed by Russia, Brazil, India, Colombia, and the United States, according to Cloudflare data.
Cloudflare noted that while it was not the largest application-layer attack they have seen, it is the largest they’ve seen over HTTPS.
“HTTPS DDoS attacks are more expensive in terms of required computational resources because of the higher cost of establishing a secure TLS encrypted connection,” Cloudflare researchers said.
“Therefore it costs the attacker more to launch the attack, and for the victim to mitigate it. We’ve seen very large attacks in the past over (unencrypted) HTTP, but this attack stands out because of the resources it required at its scale.”
The attack was aimed at a “crypto launchpad” which Cloudflare said are “used to surface Decentralized Finance projects to potential investors.”
Cloudflare did not respond to requests for comment about whether the attack was connected to the resurgent Emotet botnet. But the report does say that the attack came from a botnet that they have been tracking because of previous attacks “matching the same attack fingerprint” that reached as high as 10M rps.
“What’s interesting is that the attack mostly came from data centers. We’re seeing a big move from residential network Internet Service Providers (ISPs) to cloud compute ISPs,” Cloudflare explained.
“Within those countries, the attack originated from over 1,300 different networks. The top networks included the German provider Hetzner Online GmbH (Autonomous System Number 24940), Azteca Comunicaciones Colombia (ASN 262186), OVH in France (ASN 16276), as well as other cloud providers."
The biggest bandwidth DDoS attack ever recorded was 2.3 terabytes per second (Tbps), recorded by Amazon Web Services in February 2020.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.