Cisco warns of critical vulnerabilities in routers
Cisco this week urged customers to patch three vulnerabilities discovered in a handful of its routers.
The company said the vulnerabilities — which could affect Cisco Small Business RV160, RV260, RV340, and RV345 Series Routers — could allow an unauthenticated remote attacker to execute arbitrary code or cause a denial of service (DoS) condition on an affected device.
The Cybersecurity and Infrastructure Security Agency (CISA) released its own warning about the vulnerabilities on Thursday, writing that they could allow someone to take control of an affected system.
Two of the bugs — labeled CVE-2022-20827 and CVE-2022-20841 — affect nine router models, while CVE-2022-20842 affects four.
Cisco said the vulnerabilities are dependent on one another because exploitation of one may be needed to take advantage of the others.
“In addition, a software release that is affected by one of the vulnerabilities may not be affected by the other vulnerabilities,” Cisco explained.
CVE-2022-20842 and CVE-2022-20827 are rated "critical" and carry vulnerability scores (CVSS) of 9.8 and 9, respectively. CVE-2022-20841 is rated "high" and has a CVSS of 8.3.
There are no workarounds for the vulnerabilities, and CIsco’s security team said it is not aware of their malicious use.
Chris Clements, VP of solutions architecture at Cerberus Sentinel, told The Record that the worst of the issues that can be exploited by a remote unauthenticated attacker appear to target Cisco devices' web management interface.
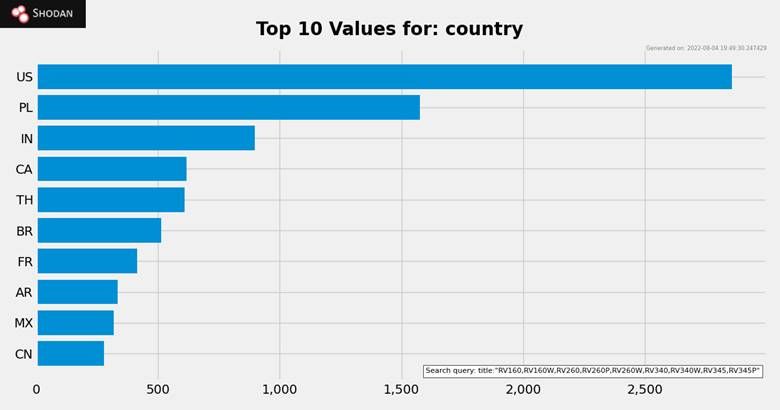
He said a non-exhaustive search on Shodan found more than 12,000 web management interfaces exposed to the internet, with most based in the U.S.
“Clearly this indicates that devices have been either mistakenly misconfigured to allow internet access to the management interface, or possibly purposefully by an internal or external IT provider looking to enable remote management of the devices without understanding the security risk that presents,” he said.
He added that compromising a gateway device can be a significant risk because attackers can use that entry point to intercept sensitive information and use it as a launchpad for further attacks against users and endpoints in the organization.
KnowBe4’s Roger Grimes said the vulnerabilities are serious but noted that most Cisco devices have unpatched vulnerabilities.
“In my 20-year career of penetration testing I never found a fully patched Cisco router... ever! So, this is just one more Cisco router exploit that an attacker can use,” he said. “But for the attackers who target potential victims with Cisco routers, it's another arrow in their attack quiver, one that is pretty likely to score a bull's eye. The attackers will be coming."
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



