CISA adds F5 vulnerability to catalog of exploited bugs
The Cybersecurity and Infrastructure Security Agency (CISA) added a vulnerability affecting F5’s BIG-IP product to its list of known exploited vulnerabilities on Tuesday following reports earlier in the week that it was being actively exploited.
CISA urged F5 customers last week to patch the vulnerability, which carries a CVSS score of 9.8 and could allow an attacker “to take control of an affected system.”
Over the weekend, several researchers released proof-of-exploit code and by Monday, Bleeping Computer and Ars Technica confirmed reports that hackers had begun exploiting the vulnerability – which is tagged as CVE-2022-1388.
Cronup security researcher Germán Fernández said he was seeing “massive” exploitation of the bug, with hackers installing WebShells “as a backdoor to maintain access” even after the vulnerability is patched.
Fernández later said that he has seen more than 300 compromised F5 devices via CVE-2022-1388.
Logré identificar +300 dispositivos F5 comprometidos vía CVE-2022-1388, aún si ya parcharon deben realizar análisis de seguridad ASAP.
— Germán Fernández (@1ZRR4H) May 10, 2022
No solo debes eliminar los PHP creados recientemente en /usr/local/www/xui/common/* también debes limpiar el archivo /config/startup ⚠️ https://t.co/my8d0G0VP6 pic.twitter.com/zYSPBXZ5hI
Cybersecurity expert Kevin Beaumont also confirmed that the bug is being exploited in the wild. “One thing of note - exploit attempts I've seen so far, not on management interface. If you configured F5 box as a load balancer and firewall via self IP it is also vulnerable so this may get messy,” he added.
He later said devices were being erased through the vulnerability.
F5 released an advisory about the bug last week and said it could allow an attacker with access through the BIG-IP system’s management port to execute arbitrary system commands, create or delete files, or disable services.
BIG-IP products — which include software and hardware — are used widely by companies to help keep their applications up and running. The bug revolves around the iControl REST component, which helps manage interaction “between user or script and F5 device,” according to the company.
F5 said BIG-IP versions 16.1.0 to 16.1.2, 15.1.0 to 15.1.5, 14.1.0 to 14.1.4, 13.1.0 to 13.1.4, 12.1.0 to 12.1.6 and 11.6.1 to 11.6.5 are affected.
F5 published fixes for each version except for 12.1.0 to 12.1.6 and 11.6.1 to 11.6.5. It urged those using these versions to upgrade to a version with the fix.
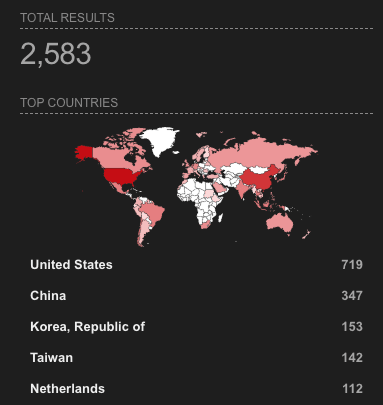
CISA gave the bug a remediation date of May 30, but a search on Shodan revealed more than 2,500 exposed instances across the globe. Some experts have argued that a number of these may be "honeypots" from researchers looking into hackers attempting to exploit the vulnerability.
Several cybersecurity companies, including Scythe and Randori, have released guides and explainers to help those attempting to address the issue.
CISA also added five other bugs to the catalog last week addressing several bugs in Apple, Microsoft and OpenSSL products.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



