Chinese Android malware gang still active and targeting Koreans 8 years later
Despite having its operations publicly exposed in the mid-2010s, a Chinese malware gang has not faced any legal consequences for their actions and has continued to operate undisturbed, spreading Android banking trojans inside South Korea.
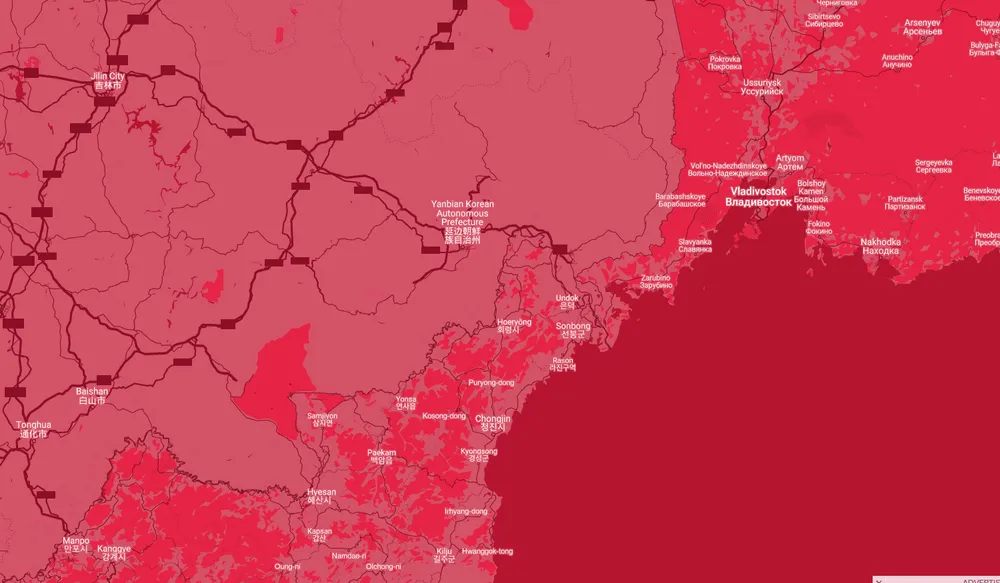
Known as the Yanbian Gang, the group gets its name from the Yanbian Chinese prefecture, where the gang's members are believed to reside.
The group has been active since 2013 and had its operations exposed in a 2015 Trend Micro report, which claimed the gang was formed at the time of four people acting in roles of leader, malware coder, Korean translator, and cowboy (money mule on the ground in South Korea).
At the time, Trend Micro said the group was using boobytrapped Android apps hosted on third-party sites to infect South Koreans with banking trojans that stole their e-banking credentials and emptied accounts.
The group turned heads in 2015 after it developed a whopping 1,007 Android apps that mimicked official Google applications — with 994 of them posing as the official Google Play app.
Yanbian gang deploys 377 new malicious Android apps
But more than eight years later, the group is still active today, suggesting that Chinese law enforcement officials failed to act on Trend Micro's discovery.
In a new report published on Wednesday, security firm RiskIQ said it detected new activity linked to this group.
The RiskIQ team said it discovered a new wave of Android banking trojans developed by the Yanbian gang. In total, the security firm said it detected 377 Android apps hosted across a large cloud infrastructure, consisting of 266 IP addresses hosting the malware and 177 IP addresses working as command-and-control (C&C) servers.
This new infrastructure appears to have been set up around December 2020 and has been actively used in attacks.
RiskIQ also said that just like in previous campaigns, the Yanbian group has continued to target South Korean users. However, the difference in these more recent attacks was that the group stopped using apps that posed as Google applications and instead switched to using apps that mimicked local mobile banking tools.
These malware-laced apps were hosted on third-party websites and were not spread via the official Google Play Store, which means most users would be safe from attacks as long as they don't install apps downloaded from random internet sites.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.