China-based spies are hacking East Asian semiconductor companies, report says
Chinese state-backed hackers have targeted the semiconductor industry in East Asia with a new espionage campaign, according to new research.
The Dutch cybersecurity firm EclecticIQ attributed the campaign to China because the hackers used the HyperBro loader, which is associated with a state-backed group labeled Budworm or APT27 by researchers.
Budworm has been associated with espionage operations that targeted a Middle Eastern telecom organization and an Asian government in September, as well as a U.S. state legislature last year.
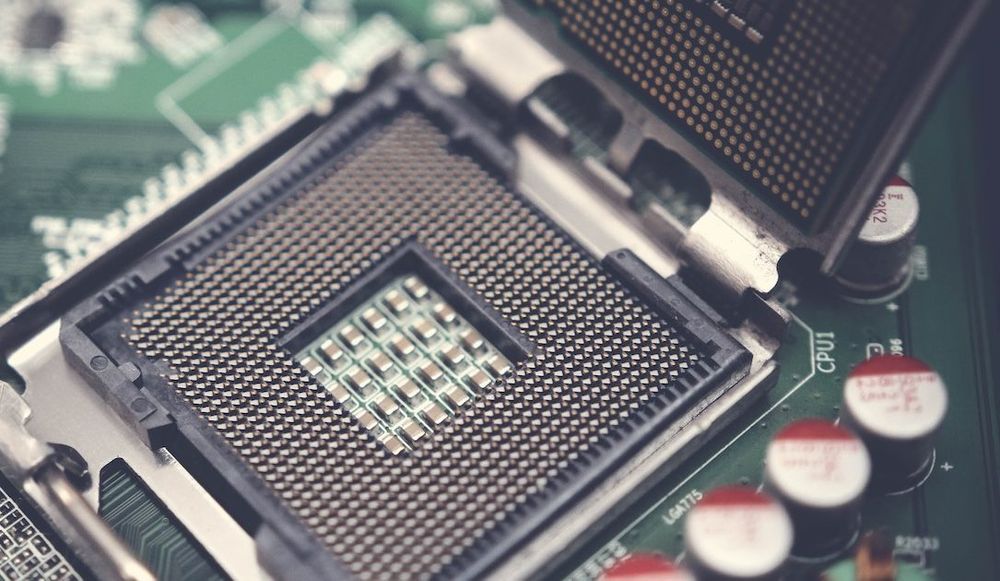
In the recent campaign targeting semiconductor companies, the group posed as Taiwan Semiconductor Manufacturing Company (TSMC) to trick victims into clicking on malicious links. TSMC is a major player in the industry, making microchips for big companies like Apple and Nvidia.
Targets were infected with a Cobalt Strike beacon, EclecticIQ said. The software is a penetration testing tool commonly used by cybersecurity professionals to simulate cyberattacks and test the security of computer systems. However, it is often abused by criminals to remotely issue commands and steal information from victims.
The Cobalt Strike beacon was installed on victims' computers using the HyperBro loader. When the loader is executed, it shows a PDF file that pretends to be from TSMC, to confuse the user.
The hackers also used a new backdoor called ChargeWeapon, which was designed to get remote access to the victim and send device and network information from an infected computer to an attacker’s server.
“This information is very likely collected by threat actors to perform initial reconnaissance against infected hosts and identify high-value targets,” said EclecticIQ.
While the report doesn't specify how the attackers first got into the system, they likely sent phishing emails to their targets.
Earlier this month, researchers identified another China-linked cyber espionage campaign targeting government agencies in Guyana with a previously undocumented backdoor called DinodasRAT.
Daryna Antoniuk
is a reporter for Recorded Future News based in Ukraine. She writes about cybersecurity startups, cyberattacks in Eastern Europe and the state of the cyberwar between Ukraine and Russia. She previously was a tech reporter for Forbes Ukraine. Her work has also been published at Sifted, The Kyiv Independent and The Kyiv Post.